Vercel Data Breach 2026: Business Impact and Response

Key Takeaways

- Hackers claim access to API keys, NPM tokens, and internal deployments worth $2M ransom demand
- 580 employee records exposed including names and email addresses
- Immediate action required: rotate secrets, audit environment variables, review access logs
According to [BleepingComputer](https://www.bleepingcomputer.com/news/security/vercel-confirms-breach-as-hackers-claim-to-be-selling-stolen-data/), cloud development platform Vercel has confirmed a security breach after threat actors claimed to have stolen internal data and are now attempting to sell it, with an alleged ransom demand of $2 million.
Read in Short
Vercel's confirmed breach potentially exposes customer API keys, NPM tokens, GitHub tokens, and source code. If your company deploys on Vercel, rotate all secrets immediately. This isn't just a Vercel problem. It's a wake-up call for every business relying on third-party deployment platforms without proper secret management protocols.
What Was Stolen in the Vercel Breach?
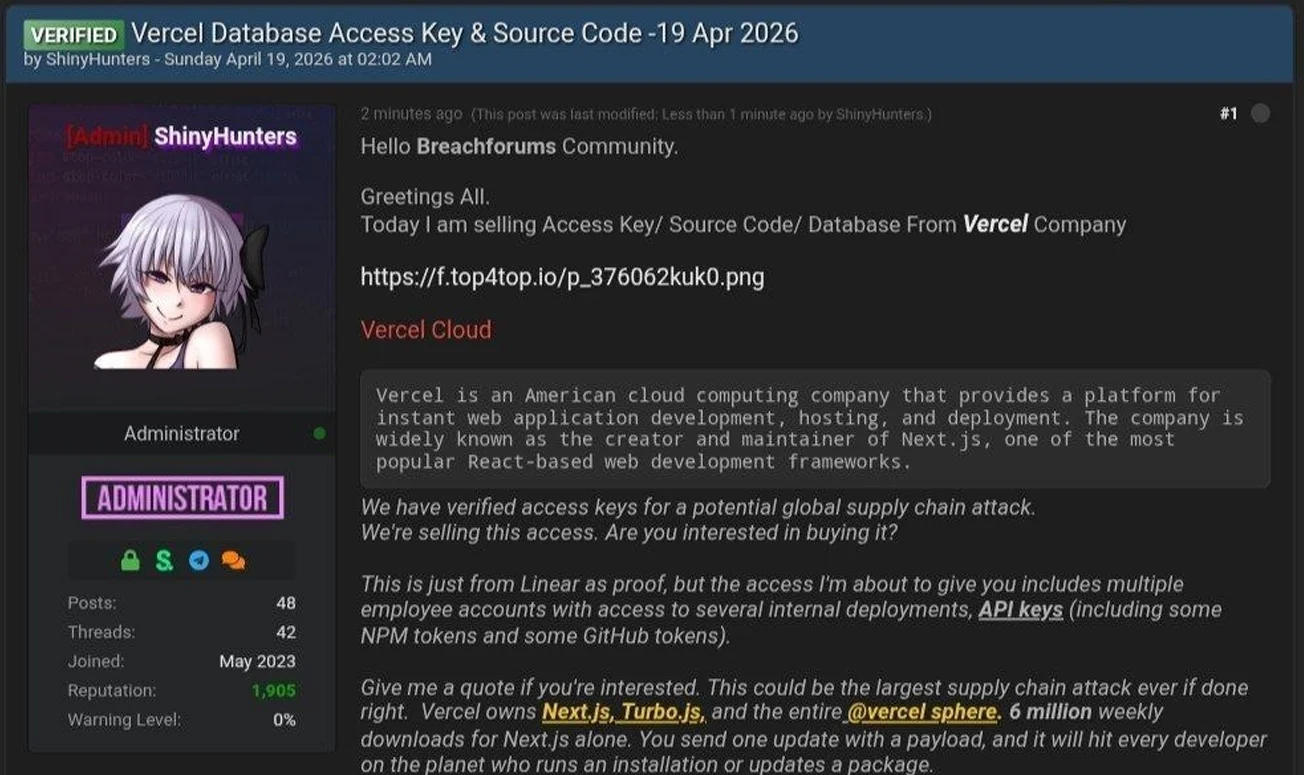
The threat actor, claiming to be part of the notorious ShinyHunters group, posted on hacking forums offering access to what they describe as a significant haul of Vercel's internal assets. Though ShinyHunters members have denied involvement to BleepingComputer, the data being shopped around tells a concerning story for Vercel's enterprise customers.
The alleged stolen data includes multiple categories that should concern any CTO whose team uses Vercel for deployments:
- Access keys and API credentials from internal systems
- Source code from internal repositories
- Database data from company systems
- NPM tokens that could compromise package publishing
- GitHub tokens providing access to code repositories
- Access to internal deployments and enterprise dashboards
The attacker shared screenshots of what appears to be an internal Vercel Enterprise dashboard along with a text file containing employee information. While BleepingComputer couldn't independently verify the authenticity of this data, the fact that Vercel has confirmed a breach adds credibility to at least some of these claims.
Why Should CEOs Care About This Breach?
Vercel isn't just another cloud service. It's the deployment backbone for thousands of companies, from early-stage startups to enterprises running mission-critical applications. The company developed Next.js, one of the most popular React frameworks, and provides serverless functions, edge computing, and CI/CD pipelines that power production applications worldwide.
Here's what makes this breach particularly dangerous for your business: environment variables and secrets stored in Vercel often include database credentials, third-party API keys, payment processor tokens, and authentication secrets. If attackers gained access to customer deployment configurations, they potentially have the keys to your entire application infrastructure.
The Real Business Risk
A compromised API key isn't just a technical problem. It's a potential data breach affecting your customers, a compliance violation that could trigger regulatory action, and a trust issue that damages customer relationships. The cost of rotating credentials proactively is measured in engineering hours. The cost of a resulting breach is measured in millions.
What Is Vercel Doing About the Security Incident?
Vercel's response has been measured but limited in details. The company published a security bulletin acknowledging unauthorized access to internal systems and has taken several steps:
- Engaged incident response experts to investigate and remediate
- Notified law enforcement authorities
- Committed to updating customers as the investigation progresses
- Working directly with impacted customers
Vercel states that its services have not been impacted by the breach. However, the company is advising all customers to take protective measures regardless of whether they've been directly notified. This cautious approach suggests the full scope of the breach may still be unclear even to Vercel's own security team.
Detailed technical response guide for engineering teams
How to Protect Your Company Right Now
Vercel has published specific guidance for customers, but I'd go further. Here's a prioritized action plan based on the potential exposure:
| Priority | Action | Timeline | Who Owns It |
|---|---|---|---|
| Critical | Rotate all Vercel environment variables and secrets | Immediately | DevOps/Platform Team |
| Critical | Rotate any NPM tokens used in deployments | Within 24 hours | Engineering Lead |
| High | Audit GitHub token permissions and rotate if necessary | Within 24 hours | Security Team |
| High | Review Vercel access logs for suspicious activity | Within 48 hours | Security Team |
| Medium | Enable Vercel's sensitive environment variable feature | Within 1 week | DevOps Team |
| Medium | Implement secrets management solution if not present | Within 2 weeks | Platform Team |
The sensitive environment variable feature Vercel mentions prevents secrets from being readable through their API or dashboard after being set. If you're not using this feature, you're essentially trusting that Vercel's access controls will never be compromised. This breach proves that trust was misplaced.
Vendor Security Assessment: Questions to Ask Now
This incident should trigger a broader conversation in your organization about vendor security practices. Every deployment platform, CI/CD tool, and cloud service you use represents a potential attack vector. Here are the questions your security team should be asking about every critical vendor:
- What data do they have access to, and how is it encrypted at rest and in transit?
- What's their incident response track record and notification timeline?
- Do they support hardware security modules (HSMs) for secret storage?
- What compliance certifications do they hold (SOC 2, ISO 27001, etc.)?
- Can we implement our own encryption layer on top of their infrastructure?
- What's their employee access control model for customer data?
The ShinyHunters group, regardless of whether they're actually behind this specific attack, has a history of high-profile breaches including AT&T, Ticketmaster, and Microsoft. Their tactics often involve targeting internal tools and employee credentials. This should inform how you think about supply chain security for your development infrastructure.
The Bigger Picture: Cloud Platform Security Risks
Vercel's breach comes at a time when organizations are increasingly dependent on specialized cloud platforms for core infrastructure. The convenience of managed deployment platforms is undeniable, but it comes with a trade-off: you're trusting a third party with credentials that could unlock your entire application.
✅ Pros
- • Managed platforms reduce operational burden on engineering teams
- • Built-in scaling and edge deployment capabilities
- • Faster time-to-market for new features
- • Professional security teams monitoring infrastructure 24/7
❌ Cons
- • Single point of failure for credential exposure
- • Limited visibility into internal security practices
- • Dependency on vendor's incident response capabilities
- • Potential for supply chain attacks affecting all customers
This doesn't mean you should abandon Vercel or similar platforms. It means you need to architect your systems assuming that any vendor could be compromised. Defense in depth isn't just a security buzzword. It's the difference between a vendor breach becoming a headline and it becoming your company's extinction event.
Build better security research workflows for your team
Financial Impact of Data Breaches in 2026
The $2 million ransom demand allegedly made to Vercel might seem significant, but it's a fraction of what a major data breach actually costs. According to IBM's Cost of a Data Breach Report, the average breach cost in 2025 exceeded $4.5 million, with cloud-based breaches trending higher due to the blast radius of compromised credentials.
For companies affected by this Vercel incident, the costs extend beyond immediate remediation. Consider the engineering time for credential rotation across all environments, the security audit expenses, potential regulatory notifications if customer data was exposed, and the long-term trust implications with your own customers.
FAQ: Vercel Breach Business Impact
Frequently Asked Questions
Is my company's data compromised in the Vercel breach?
Vercel states that a limited subset of customers was affected. However, the company is advising all customers to rotate secrets and review environment variables as a precaution. If you haven't received direct notification from Vercel, you're likely not in the directly impacted group, but you should still take protective measures.
How much will it cost to respond to this breach?
Direct costs depend on your infrastructure complexity. Expect 20-40 engineering hours for a comprehensive credential rotation and audit for a mid-sized deployment. Add security consulting costs if you need external help. The alternative, dealing with a resulting breach of your systems, would cost 100x more.
Should we migrate away from Vercel?
Not necessarily. Every major cloud provider has experienced security incidents. The question is whether Vercel's response and future security improvements meet your risk tolerance. Use this as an opportunity to implement proper secrets management regardless of which platform you use.
How long will the Vercel investigation take?
Major breach investigations typically take 2-6 months to complete fully. Vercel has committed to updating customers as the investigation progresses. Expect incremental updates over the coming weeks, with a comprehensive post-mortem likely taking several months.
What regulatory implications does this breach have?
If customer personal data was exposed, GDPR, CCPA, and other privacy regulations may require notification to affected individuals. Vercel is working with law enforcement, which suggests they're taking regulatory compliance seriously. Monitor their updates for guidance on your own notification obligations.
Logicity's Take
We deploy client applications on Vercel regularly. It's our go-to platform for Next.js projects because the developer experience is genuinely excellent. But this breach reinforces something we've been pushing with clients for the past year: never store secrets directly in any deployment platform's environment variables without a secondary encryption layer. For our projects, we use external secrets managers like HashiCorp Vault or AWS Secrets Manager that inject credentials at runtime. Yes, it adds complexity. Yes, it slows down onboarding for new team members. But it also means that even if a platform vendor gets breached, attackers get encrypted blobs instead of plaintext API keys. The $2 million ransom demand is interesting from a negotiation standpoint. It suggests the attackers believe they have something valuable enough to warrant that price, but not so catastrophic that Vercel would immediately pay. For companies evaluating their own security posture, ask yourself: what would attackers demand if they had access to your deployment secrets? If the answer makes you uncomfortable, your secret management needs work.
Need Help Implementing This?
Logicity helps companies implement proper secrets management, security audits, and incident response planning for cloud deployments. If this breach has you rethinking your security posture, let's talk about building resilient infrastructure that assumes vendors will eventually be compromised.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read
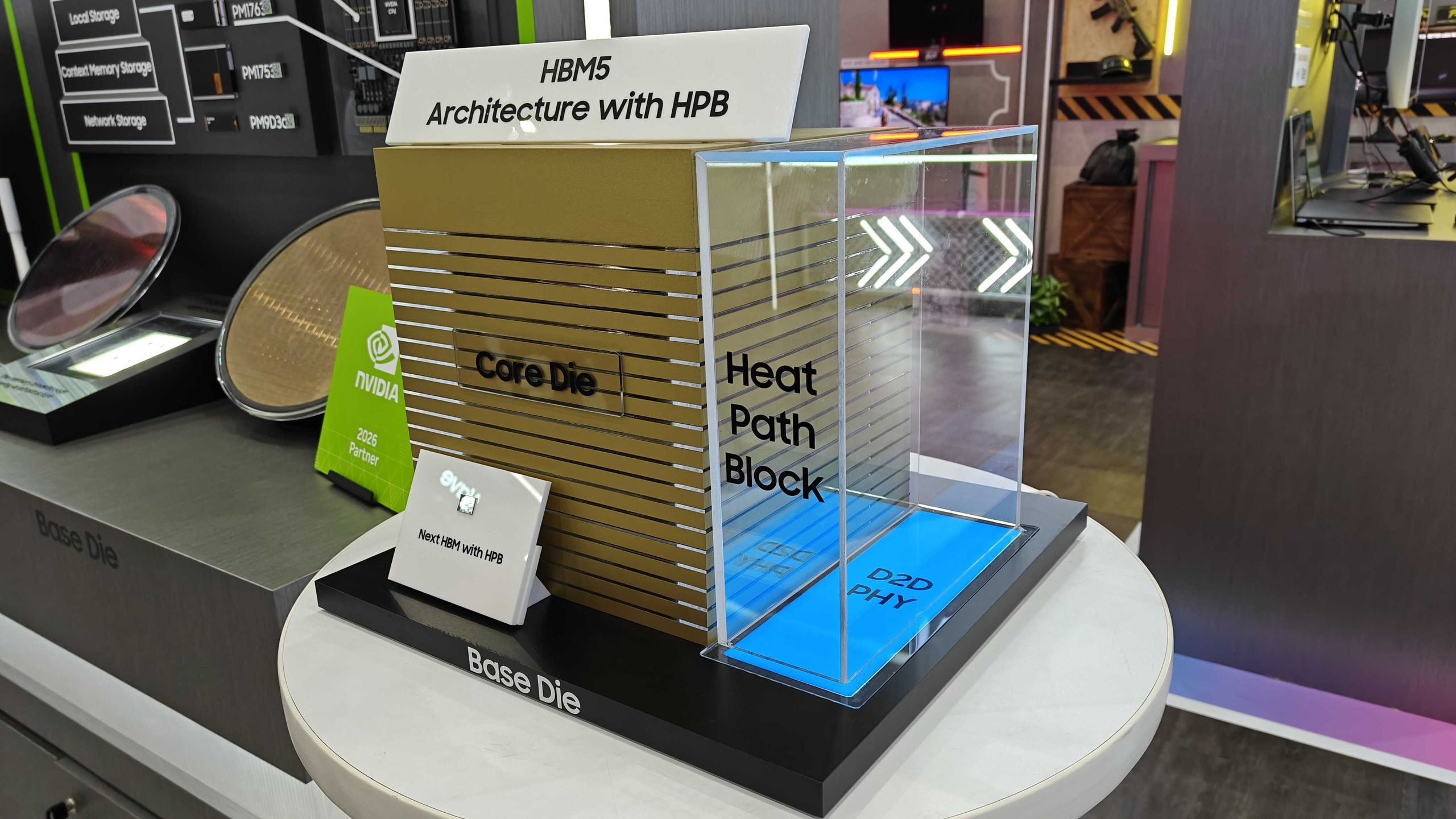
Samsung Shows HBM5 Mockup With Heat Path Block Cooling
Samsung unveiled its first physical HBM5 memory mockup at Computex 2026, featuring a new thermal design called Heat Path Block. The company confirmed it will manufacture HBM5's base die on its 2nm process, setting up a direct thermal engineering competition with SK hynix.

CISA Warns of Active Exploits Targeting Android, Linux Flaws
The U.S. Cybersecurity and Infrastructure Security Agency added two vulnerabilities to its Known Exploited Vulnerabilities catalog. Federal agencies must patch by June 5, 2026. The flaws affect Android 14-16 and multiple Linux kernel versions.

6 Ways to Stay Cool Indoors This Summer Without Breaking the Bank
As summer electricity bills hit a projected 12-year high of $784, homeowners are rethinking indoor cooling strategies. From supercooling techniques to strategic window management, here's how to survive the heat without destroying your budget.