Vercel Security Breach 2026: What CTOs Must Do Now
Key Takeaways
- Vercel confirmed unauthorized access to internal systems affecting some customers
- Immediate action required: rotate all environment variables and API keys
- This is a wake-up call for vendor risk assessment in your tech stack
According to [Vercel's official security bulletin](https://vercel.com/kb/bulletin/vercel-april-2026-security-incident), the company has identified a security incident involving unauthorized access to certain internal Vercel systems. The company is actively investigating with external incident response experts and has notified law enforcement.
If your company runs production applications on Vercel, this isn't just another security headline to skim past. It's an action item for your Monday morning standup.
Read in Short
Vercel confirmed a breach of internal systems in April 2026. While they say only a "limited subset" of customers were impacted, every Vercel customer should rotate environment variables immediately. This incident exposes a broader truth: your cloud vendors are part of your attack surface, and most companies don't treat them that way.
What Happened in the Vercel Security Breach?
Here's what we know from Vercel's disclosure: unauthorized actors gained access to internal Vercel systems. The company hasn't specified which systems, what data was accessed, or how the breach occurred. They've engaged external incident response experts and notified law enforcement.
Vercel states they've identified a "limited subset" of impacted customers and are contacting them directly. Their services remain operational. But here's the problem with "limited subset": if you're a Vercel customer and you haven't heard from them, you still can't assume you're safe.
Why Should CTOs Care About This Vercel Incident?
Vercel isn't a niche tool. It's infrastructure. Thousands of companies from startups to enterprises deploy their Next.js applications, serverless functions, and edge computing workloads through Vercel. When their internal systems are compromised, your environment variables, API keys, database credentials, and deployment configurations are potentially exposed.
Think about what lives in your Vercel environment variables right now: Stripe API keys, database connection strings, third-party service credentials, internal API tokens. A breach at Vercel isn't just about Vercel. It's about every system those credentials can access.
The Real Risk
Environment variables often contain credentials with broad permissions. A single leaked database connection string could expose customer data, financial records, or proprietary business logic. The blast radius extends far beyond the hosting platform.
Immediate Actions for Vercel Customers
Vercel recommends three immediate steps. I'd add a few more based on what we've seen from similar incidents at companies we've worked with.
- Audit your activity logs: Check your Vercel account and all environments for suspicious activity. Look for unexpected deployments, configuration changes, or access from unfamiliar IP addresses.
- Rotate all environment variables: Yes, all of them. Treat every secret stored in Vercel as potentially compromised. This includes API keys, database credentials, OAuth secrets, and webhook tokens.
- Enable sensitive environment variables: Vercel offers a feature that prevents environment variables from being exposed in build logs. If you're not using it, enable it now.
- Audit downstream systems: Any system that your Vercel-stored credentials can access needs a security review. Check access logs for your databases, third-party APIs, and internal services.
- Review team access: Check who has access to your Vercel account. Remove any users who shouldn't be there. Consider implementing SSO if you haven't already.
How Much Does a Security Incident Like This Cost?
The direct costs of responding to a vendor security incident are substantial, but the indirect costs are what really hurt. Let's break it down.
| Cost Category | Small Startup | Mid-Size Company | Enterprise |
|---|---|---|---|
| Engineering time for credential rotation | 8-16 hours | 40-80 hours | 200+ hours |
| Security audit and assessment | $2,000-5,000 | $10,000-25,000 | $50,000+ |
| Potential downtime during rotation | 2-4 hours | 4-8 hours | Variable |
| Customer notification (if required) | $500-1,000 | $5,000-10,000 | $25,000+ |
| Legal and compliance review | $1,000-3,000 | $10,000-20,000 | $50,000+ |
These numbers assume no actual data breach on your end. If compromised credentials were used to access your systems, costs escalate dramatically. The average cost of a data breach in 2025 was $4.88 million according to IBM's annual report.
Vendor Security Risk: The Blind Spot in Your Stack
This Vercel incident highlights a problem most companies ignore: vendor security is your security. When you store credentials in a third-party platform, you're trusting their security practices. When they fail, you inherit the consequences.
Most companies do extensive due diligence before signing enterprise contracts. They check SOC 2 reports, review security questionnaires, and negotiate data processing agreements. But how many revisit that assessment annually? How many monitor their vendors for security incidents?
- Create a vendor inventory: List every third-party service that stores your credentials or data
- Establish monitoring: Set up alerts for security disclosures from your critical vendors
- Define response playbooks: Know exactly what you'll do when a vendor reports a breach
- Implement secrets management: Consider tools like HashiCorp Vault or AWS Secrets Manager to centralize credential storage
- Practice credential rotation: If rotating secrets is painful, you'll delay it during an incident
Understanding how AI companies handle security at scale matters for vendor assessment
Should You Leave Vercel After This Breach?
Let's be realistic: every major cloud provider has experienced security incidents. AWS, Google Cloud, Azure, GitHub, CircleCI. The question isn't whether your vendors will ever have a security incident. It's how they respond when it happens.
✅ Pros
- • Vercel disclosed promptly and engaged external experts
- • Services remain operational during investigation
- • They're directly contacting affected customers
- • Clear guidance on protective actions
❌ Cons
- • Limited detail on scope and nature of breach
- • No timeline for full disclosure
- • Unknown what systems were accessed
- • Customers must assume worst case for now
Switching platforms based on a single incident is usually an overreaction. What matters more: does this change your risk assessment of Vercel? Do they have a pattern of security issues? How does their response compare to industry standards?
For most companies, the right response is to implement the immediate protective actions, monitor for updates, and use this as an opportunity to strengthen your overall vendor security posture.
Building better research workflows helps with ongoing vendor security monitoring
The Long-Term Play: Building Resilient Infrastructure
This incident is a good excuse to audit your entire deployment architecture. Here are the questions your engineering team should be able to answer:
- Can we rotate all production credentials within 4 hours?
- Do we have automated detection for compromised credentials?
- Are our secrets stored with proper encryption and access controls?
- Do we have a tested incident response plan for vendor breaches?
- Can we deploy to an alternative platform if needed?
If the answer to any of these is "no" or "I don't know," that's your next engineering priority. The Vercel incident might not have affected you directly. The next vendor breach might.
Logicity's Take
We've deployed dozens of production applications on Vercel for our clients, and this incident hits close to home. Our immediate response: we rotated credentials for every active Vercel project within hours of the disclosure. That was possible because we'd already implemented centralized secrets management through environment variable templates and documented rotation procedures. Here's what we've learned from shipping Next.js apps on Vercel: the platform's developer experience is exceptional, but that convenience can make teams complacent about security fundamentals. Many teams store long-lived credentials with excessive permissions because it's easy. This incident is a reminder that "easy" has hidden costs. For our Indian startup clients especially, we're now recommending a quarterly vendor security review. The Indian tech ecosystem relies heavily on US-based cloud platforms. When those platforms have incidents, the notification comes in the middle of the night IST, and response times suffer. Building in redundancy and maintaining rotation-ready credentials isn't paranoia. It's operational maturity.
Frequently Asked Questions
Frequently Asked Questions
Was my Vercel account affected by the April 2026 breach?
Vercel states they're directly contacting affected customers. If you haven't heard from them, you may not be in the identified subset. However, the investigation is ongoing, and Vercel recommends all customers rotate credentials as a precaution. Don't assume you're safe just because you haven't been contacted.
How long does it take to rotate all Vercel environment variables?
For a small project with 5-10 environment variables, expect 1-2 hours including testing. For larger applications with multiple environments and dozens of secrets, budget 4-8 hours. Enterprise deployments with complex CI/CD pipelines may take longer. The key is having a documented process before you need it.
Should I migrate away from Vercel after this security incident?
Probably not based on this single incident. All major cloud providers have experienced security events. What matters is how they respond and whether this represents a pattern. Evaluate Vercel's transparency, response time, and remediation efforts. Use this as an opportunity to build platform-agnostic deployment capabilities regardless of your decision.
What's the business cost of not responding to this Vercel breach?
If your credentials were compromised and used to access customer data, you're looking at potential regulatory fines (GDPR penalties can reach 4% of global revenue), customer notification costs, legal liability, and reputation damage. Even without a data breach, unrotated credentials remain a persistent risk. The cost of rotating credentials is measured in hours. The cost of a breach is measured in millions.
How do I prevent this type of vendor risk in the future?
Implement a vendor security program: maintain an inventory of all third-party services with access to your credentials or data, monitor for security disclosures, use centralized secrets management, practice credential rotation regularly, and have documented incident response playbooks. No approach eliminates vendor risk entirely, but you can significantly reduce your exposure and response time.
What Happens Next
Vercel has committed to updating their security bulletin as the investigation progresses. Expect more detail on the scope of the breach, root cause analysis, and longer-term remediation steps. For now, treat this as a fire drill that might be a real fire.
The companies that handle this incident well will have rotated credentials, audited access logs, and improved their vendor security posture before the investigation concludes. The companies that handle it poorly will still be talking about it in their next security incident.
If you're setting up secure development environments, hardware choices matter
Need Help Implementing This?
Logicity helps companies build secure, scalable web applications on modern platforms. If you need help with credential rotation, security audits, or building more resilient deployment infrastructure, reach out at logicity.in. We've been through vendor security incidents with our clients before, and we know how to respond fast.
Source: Hacker News: Best
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read

I Swapped MacBook Neo Parts in Four Colors. Keys Broke.
Apple's $599 MacBook Neo is its easiest laptop to repair in years, so we bought one and swapped in official parts — a blush trackpad, citrus keycaps, and more. The trackpad and ports were simple. The keycaps were not. Here's what $165 in spare parts got us, and what snapped along the way.

Ultrahuman Breach Exposed User Data, Not Passwords or Payment Info
Ultrahuman CEO Mohit Kumar disclosed a March 27 security breach that gave an unauthorized third party read-only access to contact details, order history, and fitness data. No passwords, credit card numbers, or payment information were compromised. The company took 68 days to notify users.
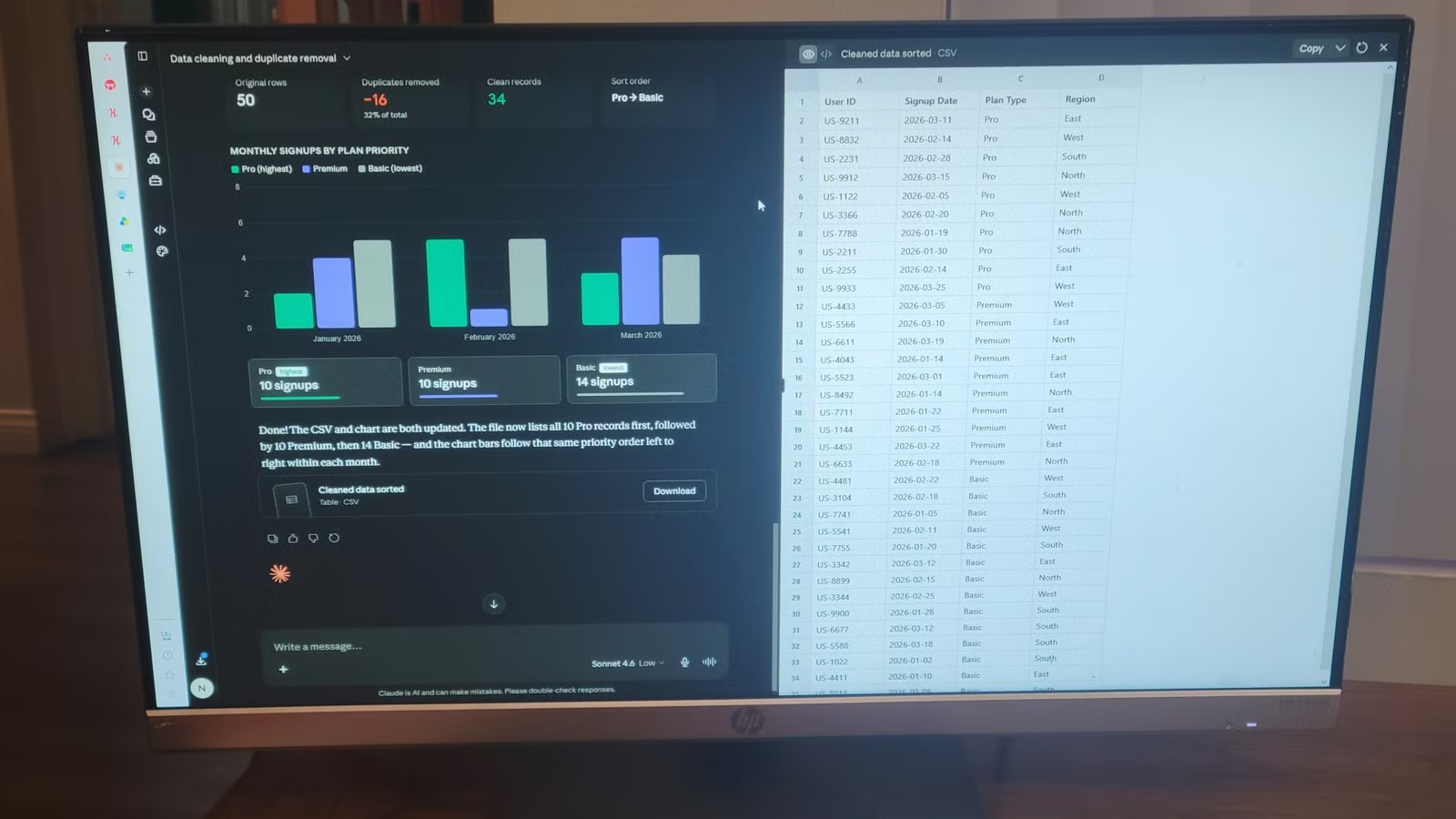
Claude's No-Code Canvas Runs Python Scripts Without Setup
Claude's built-in execution environment lets you describe a data problem in plain English and get working code back in minutes. No Python install, no debugging sessions, no dependency errors. It writes, runs, and fixes code inside the chat window.