Microsoft Fixes BitLocker Recovery Bug, But Only for Windows 11

Key Takeaways

- Microsoft fixed the BitLocker recovery bug only for Windows 11 25H2 systems via the KB5089549 update
- Windows 10 and Windows Server users must wait for a future patch and apply Group Policy workarounds
- The bug affects enterprise systems with specific TPM validation settings, not typical personal devices
Microsoft has patched a bug that forced some Windows 11 systems into BitLocker recovery mode after installing the April 2026 security updates. The fix, however, only covers Windows 11 version 25H2. Windows 10 and Windows Server users are still waiting.
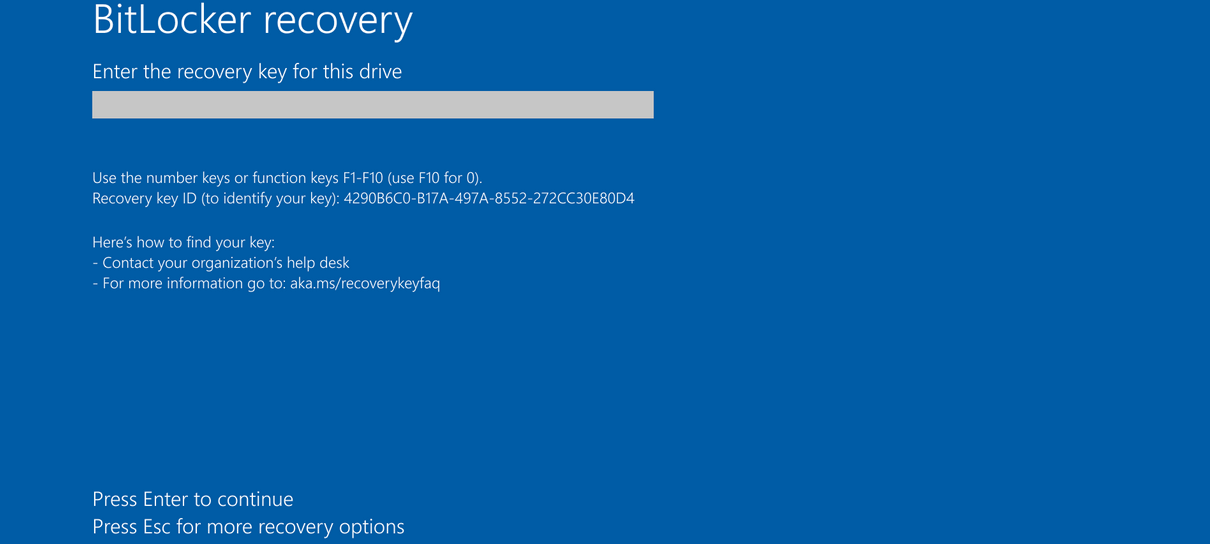
The problem surfaced after the April 2026 security update (KB5083769) rolled out. Systems with certain Trusted Platform Module (TPM) validation settings, including invalid PCR7 configurations, began prompting users for their BitLocker recovery key on first reboot. For enterprise IT teams managing fleets of encrypted devices, this meant scrambling to retrieve recovery keys or roll back updates.
What Caused the BitLocker Recovery Prompt
BitLocker encrypts storage drives to protect data if a device is lost or stolen. It relies on TPM to verify that boot files haven't been tampered with. When the April update modified boot files on systems with specific Group Policy configurations, BitLocker interpreted the change as a potential security threat and locked users out.
Microsoft acknowledged the issue on April 14, noting it affects devices with an "unrecommended" BitLocker Group Policy configuration. The company clarified that personal devices are unlikely to be impacted since the affected settings are typically found only on enterprise systems managed by IT teams.
“Some devices with an unrecommended BitLocker Group Policy configuration might be required to enter their BitLocker recovery key on the first restart after installing this update.”
— Microsoft
The Fix: Windows 11 25H2 Only
On May 13, Microsoft announced that the KB5089549 cumulative update resolves the issue for Windows 11 25H2. The update addresses the problem where devices enter BitLocker Recovery after updating boot files on systems with certain TPM validation settings.
Windows 10 and Windows Server users are not as fortunate. Microsoft says a permanent resolution for these platforms is "planned for a future update," with no specific timeline provided.
Workaround for Windows 10 and Server Admins
Until Microsoft releases patches for Windows 10 and Windows Server, IT administrators have a workaround. Microsoft recommends two steps before deploying the April 2026 updates:
- Remove the "Configure TPM platform validation profile for native UEFI firmware configurations" Group Policy setting
- Ensure BitLocker bindings use the PCR7 profile by following Microsoft's documentation
For organizations that have already deployed the update and are seeing recovery prompts, the recovery key stored in Active Directory or Azure AD will be required to unlock affected devices.
A Recurring Problem
This is not the first time Windows updates have triggered unexpected BitLocker recovery prompts. Microsoft has dealt with similar issues repeatedly over the past several years.
The pattern suggests a tension between security updates that modify boot components and BitLocker's verification mechanisms. Each incident affects enterprise environments most heavily, since consumer devices rarely use the Group Policy configurations that trigger these bugs.
May 2026 Patch Tuesday Context
The BitLocker fix arrived alongside Microsoft's May 2026 Patch Tuesday release, which addresses 120 vulnerabilities. Seventeen of those are rated "critical." IT teams juggling the BitLocker workaround still need to prioritize these security patches, creating a challenging update cycle for enterprises running mixed Windows environments.
Logicity's Take
Related BitLocker security coverage
Recent Microsoft security news
Frequently Asked Questions
Which Windows versions are affected by the BitLocker recovery bug?
The bug affects Windows 10, Windows 11, and Windows Server devices with specific TPM validation Group Policy settings. However, personal devices are unlikely to be impacted since these configurations are typically used only in enterprise environments.
How do I fix the BitLocker recovery prompt after the April 2026 update?
If you're on Windows 11 25H2, install the KB5089549 update. For Windows 10 and Windows Server, you'll need to enter your BitLocker recovery key and apply the Group Policy workaround until Microsoft releases a permanent fix.
Where can I find my BitLocker recovery key?
For enterprise devices, the recovery key is typically stored in Active Directory or Azure AD. Personal users can find it in their Microsoft account at account.microsoft.com/devices/recoverykey.
When will Microsoft fix this for Windows 10?
Microsoft has not provided a specific date. The company says a permanent resolution for Windows 10 and Windows Server is planned for a future update.
Can I prevent this issue before installing updates?
Yes. Microsoft recommends removing the "Configure TPM platform validation profile for native UEFI firmware configurations" Group Policy setting before deploying the April 2026 updates.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Sony A7R VI Hits 66.8 Megapixels with $4,500 Price Tag
Sony's new flagship high-resolution camera brings a fully stacked sensor, 8K video, and 30fps burst shooting. The A7R VI arrives in June at $4,499.99, a $600 increase over its predecessor, and introduces a new battery system that breaks compatibility with existing Sony Alpha batteries.

Why I Recommend Samsung Phones But Won't Buy One
A longtime tech writer explains the paradox of consistently recommending Samsung devices to others while refusing to own one himself. The reason comes down to One UI's software choices and the appeal of alternatives that prioritize clean Android experiences.

Hackers Hijack Microsoft Teams to Deploy Hidden Malware
A new attack uses compromised Microsoft Teams accounts to impersonate IT helpdesks. Victims are tricked into running a fake diagnostic tool that installs malware capable of evading major antivirus products.