10,500 Zimbra Servers Remain Vulnerable to Active XSS Attacks

Key Takeaways

- Over 10,500 Zimbra servers remain unpatched against CVE-2025-48700, an actively exploited XSS flaw
- The attack requires no user interaction beyond viewing a malicious email in Zimbra Classic UI
- CISA gave federal agencies just three days to patch, signaling the threat's severity
Over 10,500 Zimbra email servers exposed to the internet remain vulnerable to an actively exploited cross-site scripting flaw, according to nonprofit security organization Shadowserver. CISA added the vulnerability to its Known Exploited Vulnerabilities catalog on Monday, confirming attacks are happening now.
The flaw, tracked as CVE-2025-48700, affects Zimbra Collaboration Suite versions 8.8.15, 9.0, 10.0, and 10.1. Synacor released patches in June 2025. Ten months later, thousands of servers remain exposed.
No Clicks Required: How the Attack Works
What makes CVE-2025-48700 dangerous is its simplicity. The attack requires no user interaction. No malicious attachments. No suspicious links. No macros. The entire attack chain lives inside the HTML body of a single email.
When a user views a maliciously crafted email in the Zimbra Classic UI, arbitrary JavaScript executes within their session. This lets unauthenticated attackers access sensitive information without the victim taking any action beyond opening an email.
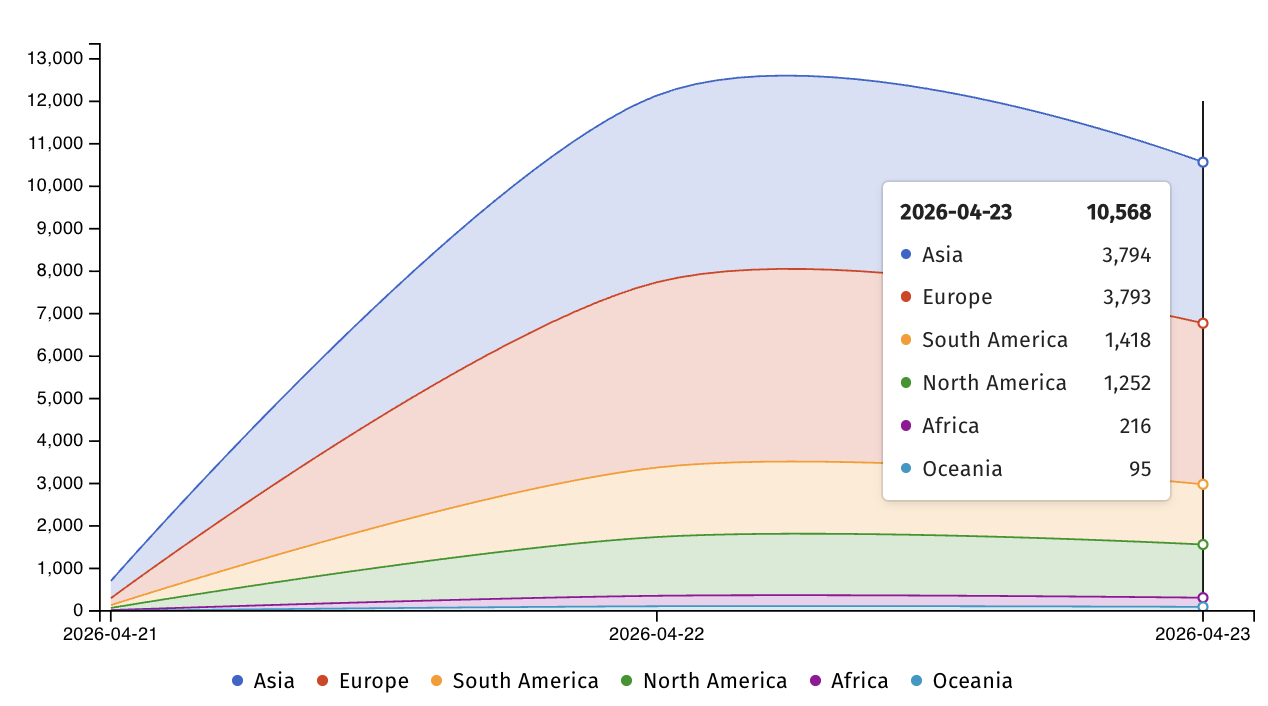
Global Exposure: Asia and Europe Hit Hardest
Shadowserver's scan found unpatched Zimbra servers concentrated in two regions. Asia accounts for 3,794 vulnerable servers. Europe has 3,793. The remaining 2,900+ are scattered across other regions.
Zimbra is popular with government agencies and businesses. Hundreds of millions of people use the email and collaboration suite worldwide. That install base makes unpatched servers attractive targets.
CISA's Three-Day Deadline
CISA ordered Federal Civilian Executive Branch agencies to secure their Zimbra servers by April 23. That gave agencies just three days from the Monday announcement. The tight deadline signals how seriously CISA views active exploitation.
CISA did not share details about who is exploiting CVE-2025-48700 or what targets they are hitting. But a related Zimbra XSS flaw offers clues about who might be interested.
APT28's Zimbra Campaign: A Preview
A separate Zimbra XSS vulnerability, CVE-2025-66376, was patched in early November. Security researchers at Seqrite Labs found that Russian state-backed hackers APT28 (also known as Fancy Bear or Strontium) had been exploiting it since January.
The campaign, codenamed Operation GhostMail, targeted Ukrainian government entities. One target was the Ukrainian State Hydrology Agency, a critical infrastructure entity under the Ministry of Infrastructure that provides navigational, maritime, and hydrographic support.
“The phishing email has no malicious attachments, no suspicious links, no macros. The entire attack chain lives inside the HTML body of a single email, there are no malicious attachments.”
— Seqrite Labs
The payload was an obfuscated JavaScript that executed when recipients opened malicious emails in vulnerable Zimbra webmail sessions. This attack pattern matches what CVE-2025-48700 enables.
Zimbra's Recurring Security Problems
Zimbra flaws are frequently exploited. The platform has a history of being targeted by sophisticated actors.
In February 2023, Russian Winter Vivern cyberespies used a reflected XSS exploit to breach Zimbra webmail portals. They stole emails from NATO-aligned organizations and individuals, including military personnel, government officials, and diplomats.
Organizations running Zimbra should treat any XSS vulnerability as high priority. The pattern is clear: state-backed attackers actively hunt for unpatched Zimbra servers.
What to Do Now
- Check your Zimbra version. CVE-2025-48700 affects ZCS 8.8.15, 9.0, 10.0, and 10.1.
- Apply Synacor's June 2025 patches immediately if you have not already.
- Audit logs for suspicious email activity, particularly in the Zimbra Classic UI.
- Consider whether the Zimbra Classic UI is necessary. If not, disable it.
- Monitor Shadowserver and CISA feeds for updates on this and related vulnerabilities.
Logicity's Take
Frequently Asked Questions
What is CVE-2025-48700?
It is a cross-site scripting (XSS) vulnerability in Zimbra Collaboration Suite that allows attackers to execute arbitrary JavaScript when a user views a malicious email in the Zimbra Classic UI. No user interaction beyond opening the email is required.
Which Zimbra versions are affected?
ZCS versions 8.8.15, 9.0, 10.0, and 10.1 are all vulnerable. Synacor released patches in June 2025.
Is CVE-2025-48700 being actively exploited?
Yes. CISA added it to the Known Exploited Vulnerabilities catalog on April 21, 2026, confirming active exploitation in the wild.
How many Zimbra servers are still vulnerable?
Shadowserver found over 10,500 unpatched Zimbra servers exposed online, with the highest concentrations in Asia (3,794) and Europe (3,793).
Who is exploiting Zimbra vulnerabilities?
A related Zimbra XSS flaw was exploited by APT28 (Fancy Bear), a Russian state-backed hacking group, in phishing campaigns against Ukrainian government entities. Winter Vivern, another Russian-linked group, targeted NATO-aligned organizations through Zimbra exploits in 2023.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

KTC H27P3 Review: 5K Pixel Density for $300 Less Than Asus
KTC's H27P3 delivers 218 ppi pixel density and factory-perfect color accuracy at $550, undercutting the competition by $300. The dual-mode monitor switches between 5K at 60Hz and QHD at 120Hz, making it ideal for productivity users who dabble in casual gaming.

7 ESP32 Weekend Projects for Hands-On Makers
The ESP32 microcontroller has become the go-to platform for DIY electronics enthusiasts. This weekend roundup covers seven interactive projects you can build at home, from retro gaming handhelds to virtual pets.
Tolaria: Open-Source macOS App for Markdown Knowledge Bases
A new open-source macOS app called Tolaria offers a files-first approach to managing markdown knowledge bases. Built by a developer who manages 10,000+ personal notes, it emphasizes git integration, offline functionality, and zero vendor lock-in.