UK Warns Chinese Hackers Use 260K-Device Botnets to Hide Attacks

Key Takeaways

- Chinese hacking groups have shifted from individual infrastructure to massive botnets of compromised home routers and IoT devices
- The Raptor Train botnet infected over 260,000 devices worldwide before FBI disruption in September 2024
- Traditional defenses based on blocking known malicious IP addresses are becoming ineffective against these rotating proxy networks
The UK's National Cyber Security Centre and ten allied nations have issued a joint warning: Chinese state-linked hackers are hiding their attacks behind massive networks of hijacked consumer devices. Your home router might be helping them do it.
The advisory, co-signed by agencies from the United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden, says most Chinese hacking groups have abandoned individually procured infrastructure. Instead, they now route attacks through botnets made of compromised small office and home office (SOHO) routers, internet-connected cameras, video recorders, and network-attached storage (NAS) equipment.
How the Proxy Networks Work
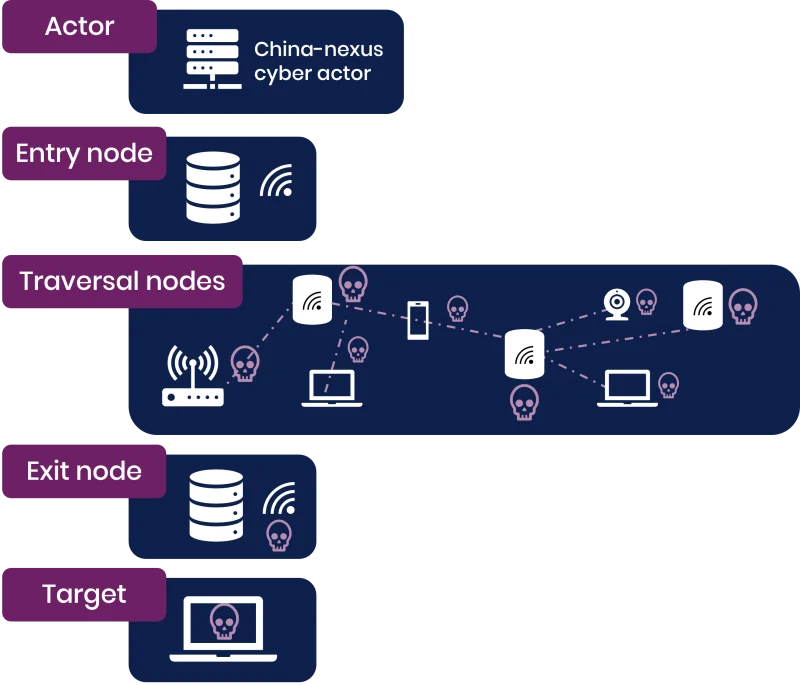
These botnets let attackers route traffic through chains of compromised devices. An attack enters the network at one point, passes through multiple intermediate nodes, and exits near the intended target. This chain-hopping makes geographic detection nearly impossible.
“The NCSC believes that the majority of China-nexus threat actors are using these networks, that multiple covert networks have been created and are being constantly updated, and that a single covert network could be being used by multiple actors.”
— Joint NCSC Advisory
The advisory describes networks built mainly from SOHO routers and IoT devices. These devices often run outdated firmware, lack security patches, and sit on networks with minimal monitoring. Owners rarely know their hardware has been conscripted into a hacking operation.
Raptor Train: A 260,000-Device Botnet
The advisory highlights Raptor Train, a botnet that infected more than 260,000 devices worldwide in 2024. The FBI linked it to Flax Typhoon, a Chinese state-sponsored hacking group, and to Chinese company Integrity Technology Group. The US sanctioned Integrity Technology Group in January 2025.
The FBI disrupted Raptor Train in September 2024 with help from Black Lotus Labs researchers. Before takedown, the botnet targeted entities in the military, government, higher education, telecommunications, defense industrial base, and IT sectors. Most targets were in the US and Taiwan.
Volt Typhoon's Persistent Router Botnet
A separate network, KV-Botnet, was operated by Volt Typhoon. This botnet consisted primarily of vulnerable Cisco and Netgear routers that had reached end-of-life and no longer received security patches.
The FBI wiped malware from infected KV-Botnet routers in January 2024. But Volt Typhoon started rebuilding. After a failed attempt in February 2024, the group began slowly reviving the botnet in November 2024.
Why Traditional Defenses Are Failing
The advisory warns that static IP blocklists are becoming ineffective. When attackers control hundreds of thousands of devices, they can rotate through IP addresses constantly. The moment defenders block one address, attackers switch to another.
“Botnet operations represent a significant threat to the UK by exploiting vulnerabilities in everyday internet-connected devices with the potential to carry out large-scale cyber attacks.”
— Paul Chichester, NCSC-UK Director of Operations
The scale creates a numbers problem. Security teams cannot manually track and block IP addresses when the list changes daily. Behavioral detection and traffic analysis become more important than simple blocklists.
What Makes Consumer Devices Easy Targets
SOHO routers and IoT devices share several vulnerabilities that make them ideal for botnets:
- Default credentials that owners never change
- Firmware that goes months or years without updates
- No active monitoring or logging
- Always-on internet connectivity
- Manufacturers that stop issuing patches after a few years
Once compromised, these devices run silently in the background. Performance impacts are minimal. The average user has no way to detect that their router is routing attack traffic to a government network in Taiwan.
Logicity's Take
Frequently Asked Questions
How do I know if my router is part of a botnet?
Check for unusual network activity, unexplained slowdowns, or connections to unfamiliar IP addresses. Update your firmware, change default passwords, and consider replacing routers that no longer receive security patches.
Which countries signed the joint advisory?
The UK, United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden all co-signed the advisory.
What is Raptor Train?
Raptor Train was a botnet of over 260,000 compromised devices worldwide, linked to Chinese state-sponsored group Flax Typhoon. The FBI disrupted it in September 2024.
Why are IP blocklists becoming ineffective?
When attackers control hundreds of thousands of devices, they can rotate IP addresses constantly. Blocking one address does nothing when attackers immediately switch to another from their pool.
What devices are most commonly compromised?
Small office and home office routers are the primary targets, followed by internet-connected cameras, video recorders, and network-attached storage (NAS) devices.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

4 Tips Remote Workers Need to Protect Data in Public
Working from cafes, airports, and hotel lobbies is standard for remote workers, but public spaces create real security risks. The NSA and government agencies warn about shoulder surfing, rogue Wi-Fi networks, and data theft. Here are four practical steps to stay secure.

What Is AI Orchestration and Why Your Tools Need It
AI orchestration connects your AI tools, agents, and automations so they work together instead of in silos. This guide explains the core components, benefits, and how to get started with orchestrating AI workflows across your business.

US Repeats ChatGPT Policy Mistake with World Models
Stanford researchers warn that US lawmakers are ignoring world models, the next major AI frontier, just as they ignored large language models before ChatGPT launched. China is already pulling ahead in robotics while American policymakers remain unaware of what world models even are.