Russian Hackers Upgrade Kazuar Backdoor Into P2P Botnet
Key Takeaways
- Secret Blizzard has upgraded Kazuar from a simple backdoor into a modular P2P botnet with three distinct components
- The new architecture elects a 'leader' system to communicate with command servers while other infected machines stay silent
- Kazuar's code lineage traces back to 2005 and has targeted European governments and Ukrainian organizations
Russian state-backed hackers have rebuilt a nearly two-decade-old espionage tool into something far more dangerous. The group known as Secret Blizzard has transformed its Kazuar backdoor into a modular peer-to-peer botnet. The upgrade makes the malware harder to detect and capable of persisting in target networks for extended periods.
Microsoft researchers published their analysis of the new Kazuar variant on May 16, 2026. They found that what was once a straightforward backdoor now operates as a sophisticated three-module system. The architecture is designed for one purpose: long-term, quiet espionage.
Who Is Secret Blizzard?
Secret Blizzard overlaps with groups tracked as Turla, Uroburos, and Venomous Bear. Security researchers have tied the group to Russia's Federal Security Service (FSB). Their targets include government and diplomatic organizations, defense contractors, and critical infrastructure across Europe, Asia, and Ukraine.
Kazuar itself has a long history. Researchers first documented the malware in 2017, but its code lineage reaches back to 2005. In 2020, attackers deployed it against European government organizations. Three years later, it appeared in campaigns targeting Ukraine.
Three Modules, One Goal
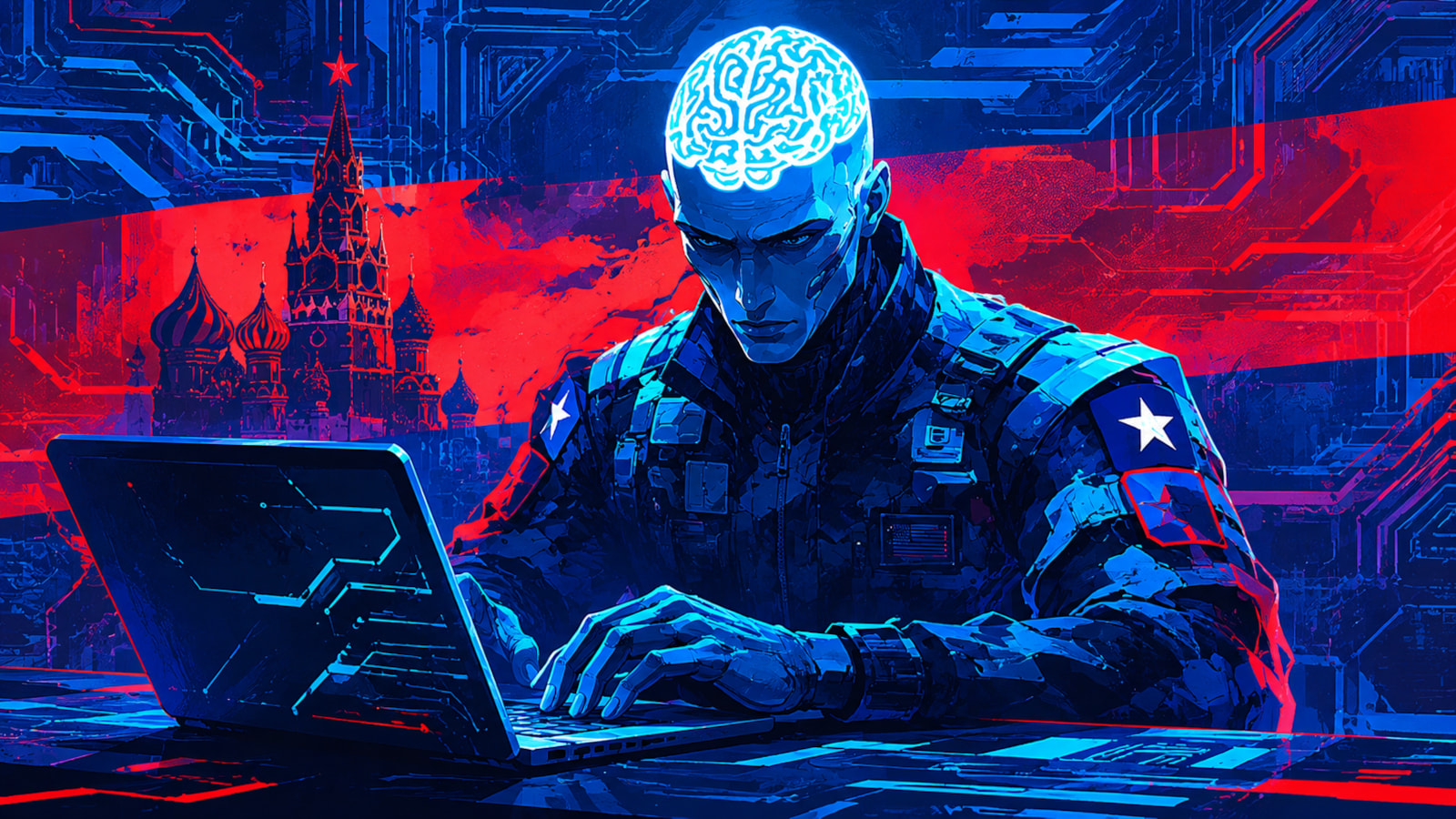
The new Kazuar variant runs on three distinct modules: Kernel, Bridge, and Worker. Each handles a specific function within the botnet.
The Kernel module acts as central coordinator. It manages tasks, controls the other modules, and orchestrates data flow across infected systems. Most importantly, it runs the leader election process.
The Leader Election System
Here's where the design gets clever. Within a compromised network, Kazuar elects one infected system as the "leader." Only the leader communicates with external command-and-control servers. Every other infected machine enters "silent" mode.
“The Kernel leader is the one elected Kernel module that communicates with the Bridge module on behalf of the other Kernel modules, reducing visibility by avoiding large volumes of external traffic from multiple infected hosts.”
— Microsoft
The election process runs autonomously. Kazuar selects leaders based on uptime, reboot counts, and interruption frequency. Systems that stay online longest and restart least often get promoted. This ensures the most stable infected machine handles the risky external communications.
Bridge: The Communication Proxy
The Bridge module handles all external traffic. It relays communications between the elected Kernel leader and remote command-and-control infrastructure. The module supports multiple protocols: HTTP, WebSockets, and Exchange Web Services (EWS).
Internal communications between infected systems use Windows inter-process communication methods. These include Windows Messaging, Mailslots, and named pipes. The traffic blends in with normal system operations.
Messages are encrypted with AES and serialized using Google Protocol Buffers (Protobuf). The combination makes intercepted traffic difficult to analyze even if defenders capture it.
Worker: The Espionage Engine
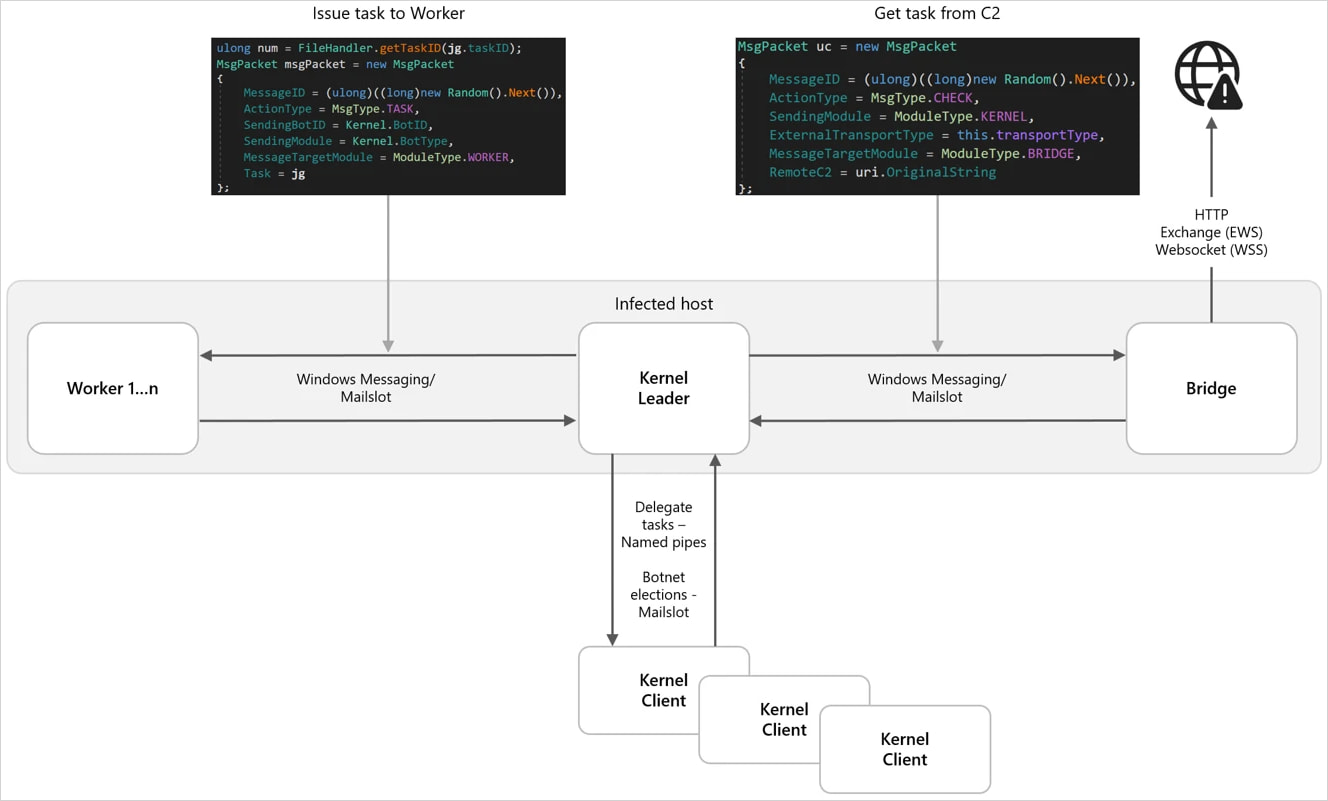
The Worker module does the actual spying. Its capabilities include:
- Keylogging
- Screenshot capture
- Filesystem data harvesting
- System and network reconnaissance
- Email and MAPI data collection, including Outlook downloads
- Window monitoring
- Recent file theft
Collected data gets encrypted and staged locally before exfiltration. The staged approach means data leaves the network in batches rather than continuous streams. This pattern is harder for security tools to flag as suspicious.
Why This Architecture Matters
The P2P design solves a persistent problem for attackers: detection. Traditional malware communicates directly with command servers. Security teams can spot this traffic and block it. When multiple infected machines all reach out to the same external IP, the pattern becomes obvious.
Kazuar's approach is different. Only one machine per network segment talks externally. The rest communicate internally using methods that look like normal Windows activity. Defenders see less suspicious traffic and have fewer indicators to work with.
The modular design also makes updates easier. Attackers can swap out or upgrade individual modules without replacing the entire malware package. If security vendors develop signatures for the Worker module, the attackers can deploy a new version while keeping the Kernel and Bridge intact.
Logicity's Take
Who Should Be Concerned
Secret Blizzard's target list hasn't changed much over the years. Government agencies, diplomatic missions, and defense-related organizations remain primary targets. Critical infrastructure operators in Europe, Asia, and Ukraine face elevated risk.
The group's focus on Exchange Web Services as a communication channel deserves attention. Organizations running on-premises Exchange servers should audit for unusual EWS traffic patterns. Cloud email migrations don't eliminate the risk, but they do reduce the attack surface for this specific vector.
Frequently Asked Questions
What is the Kazuar backdoor?
Kazuar is espionage malware linked to Russian FSB-associated hackers. First documented in 2017 but with code dating to 2005, it has been used against European governments and Ukrainian targets. The latest version operates as a modular peer-to-peer botnet.
Who is Secret Blizzard?
Secret Blizzard is a hacking group associated with Russia's Federal Security Service (FSB). The group overlaps with Turla, Uroburos, and Venomous Bear. They target government, diplomatic, and defense organizations.
How does Kazuar's leader election work?
Kazuar automatically selects one infected system as leader based on uptime, reboot counts, and interruptions. Only the leader communicates with external command servers. Other infected machines stay silent to avoid detection.
What data does Kazuar steal?
Kazuar's Worker module captures keystrokes, screenshots, filesystem data, network information, and emails including Outlook downloads. It also monitors windows and steals recent files.
How can organizations detect Kazuar infections?
Traditional perimeter monitoring may miss Kazuar due to its minimal external traffic. Organizations should monitor internal communications for unusual IPC patterns, audit Exchange Web Services traffic, and implement network segmentation.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Galaxy S26 Series Hits $200 Off, Motorola Razr 2026 Up for Pre-Order
Samsung's Galaxy S26 lineup sees its first significant discounts less than three months after launch, with the S26+ dropping to $890. Meanwhile, Motorola's Razr 2026 foldables open for pre-orders ahead of their May 21 ship date.

Microsoft Rejects Azure Vulnerability, Blocks CVE Assignment
A security researcher says Microsoft quietly patched a critical Azure Backup for AKS privilege escalation flaw after rejecting his report. CERT validated the vulnerability, but Microsoft blocked CVE issuance, leaving the researcher without formal recognition.

Claude vs ChatGPT vs Gemini: Which AI Debugs Code Best?
A developer tested all three major AI assistants with the same buggy JavaScript file containing three distinct errors. Only one found the actual root cause. The results reveal clear differences in how these tools approach code debugging.