KelpDAO Hack: $290M Crypto Heist Hits DeFi Protocols

Key Takeaways

- State-sponsored hackers stole $290 million by exploiting cross-chain verification weaknesses
- Major DeFi protocols including Aave froze operations, impacting institutional liquidity
- Attack methodology reveals systemic risks in multi-chain DeFi infrastructure
Read in Short
KelpDAO lost $290 million in a sophisticated attack attributed to North Korea's Lazarus Group. Hackers compromised cross-chain verification nodes to authorize fake transactions. Major lending protocols froze operations. If your organization holds DeFi positions or evaluates blockchain infrastructure, this incident exposes critical vendor risk considerations.
According to [BleepingComputer](https://www.bleepingcomputer.com/news/security/kelpdao-suffers-290-million-heist-tied-to-lazarus-hackers/), state-sponsored North Korean hackers are likely behind the $290 million crypto heist that impacted the KelpDAO DeFi project on Saturday, with preliminary indicators pointing to the infamous Lazarus Group.
This isn't just another crypto theft headline. For CFOs and treasury teams exploring DeFi yield strategies, for CTOs building on multi-chain infrastructure, and for risk officers assessing emerging technology exposure, this incident is a case study in how sophisticated nation-state actors are targeting the financial plumbing of Web3.
What Happened in the KelpDAO Hack?
KelpDAO operates in the liquid restaking sector. Users deposit ETH, receive rsETH tokens representing their staked position, and can use those tokens across DeFi protocols while still earning yield. Think of it as a way to have your cake and eat it too. Your assets work in multiple places simultaneously.
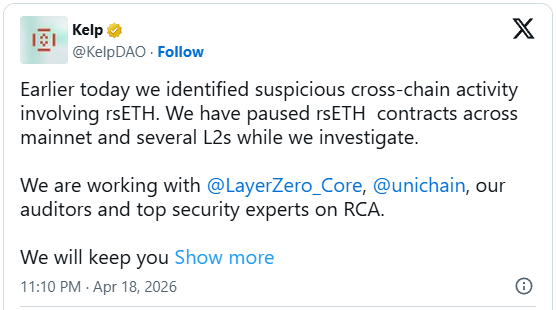
On April 18, KelpDAO detected suspicious cross-chain activity involving rsETH. The project immediately paused contracts across Ethereum mainnet and Layer 2 networks. Blockchain analysis showed approximately 116,500 rsETH tokens were stolen and laundered through Tornado Cash, a crypto mixing service.
The attack wasn't a simple smart contract exploit. According to LayerZero, which provides the cross-chain communication layer KelpDAO uses, hackers targeted the verification infrastructure itself. They compromised RPC nodes that validate cross-chain messages while simultaneously DDoS-ing healthy nodes. This forced the system to rely on compromised "poisoned" nodes.
How the Attack Worked
1. Attackers compromised RPC nodes used by verification systems 2. Simultaneously launched DDoS attacks on legitimate nodes 3. Fed falsified blockchain data through compromised nodes 4. System accepted fake cross-chain messages as valid 5. Unauthorized transactions moved rsETH to attacker wallets 6. Funds laundered through Tornado Cash within hours
Why Should Business Leaders Care About DeFi Security?
If your organization has no crypto exposure, you might scroll past this story. That would be a mistake. Here's why this matters beyond the crypto-native audience.
First, DeFi protocols are increasingly connected to traditional finance. Major institutions custody digital assets. Treasury operations experiment with yield strategies. Payment processors settle in stablecoins. The blast radius of DeFi failures keeps expanding into conventional business operations.
Second, this attack methodology applies beyond crypto. The technique of compromising verification nodes while DDoS-ing legitimate infrastructure translates to any distributed system. Supply chain attacks, API security, multi-cloud architectures. The playbook is transferable.
The Lazarus Group Connection Raises the Stakes
LayerZero's preliminary attribution points to Lazarus Group, specifically the TraderTraitor sub-unit. This is North Korea's elite cyber theft operation that has stolen billions in cryptocurrency to fund the regime's weapons programs.
The Lazarus connection matters for several reasons. These aren't opportunistic criminals. They're funded, patient, and sophisticated. The recent Drift Protocol attack involved six months of preparation, including malicious actors attending conferences and making million-dollar deposits to establish credibility.
For business leaders, this represents a different threat model. You're not defending against script kiddies or ransomware gangs. State-sponsored actors bring intelligence resources, long planning horizons, and technical capabilities that dwarf typical criminal operations.
| Factor | Criminal Hackers | State-Sponsored (Lazarus) |
|---|---|---|
| Planning Horizon | Days to weeks | 6+ months |
| Initial Investment | Minimal | Millions in setup costs |
| Human Intelligence | Limited social engineering | Conference attendance, insider cultivation |
| Technical Resources | Known exploits, purchased tools | Zero-days, custom infrastructure |
| Target Selection | Opportunistic | Strategic value assessment |
Ripple Effects Across DeFi Protocols
The KelpDAO hack didn't stay contained. Because rsETH was used as collateral across multiple lending protocols, the attack forced immediate responses from major DeFi platforms.
Aave froze rsETH operations, blocking new deposits and borrowing using the token as collateral. Compound and Euler were also reportedly impacted. When one protocol's token becomes compromised, every platform that integrated it faces potential contagion.
This interconnectedness is a feature during normal operations. It's a systemic risk during attacks. For enterprises evaluating DeFi exposure, the question isn't just whether a specific protocol is secure. It's whether the protocols it connects to are secure. And the protocols those connect to. The dependency graph matters.
Cross-Chain Verification: The Weak Link
The attack targeted LayerZero's Decentralized Verifier Network (DVN), the system that validates cross-chain messages. This is the trust layer that lets tokens move between blockchains. Compromise the verifiers, and you control what the system believes is true.
LayerZero emphasized that the incident was isolated to rsETH with no broader contagion across other apps or assets. But the attack methodology raises questions about verification architecture across the industry.
For technical leaders evaluating blockchain infrastructure, the lesson is clear. Cross-chain bridges and verification layers are high-value targets. The security of your application depends on the security of every infrastructure layer beneath it. And those layers often involve third-party dependencies with their own attack surfaces.
What This Means for Enterprise Blockchain Strategy
If you're building on or investing in blockchain infrastructure, the KelpDAO incident offers concrete lessons for risk management.
- Audit the entire dependency chain, not just smart contracts. RPC nodes, verification layers, and oracle systems are attack vectors.
- Assume cross-chain operations carry elevated risk. Multi-chain flexibility comes with multi-point failure modes.
- Monitor for sophisticated social engineering. State actors invest months in relationship building before technical exploitation.
- Build circuit breakers. KelpDAO's ability to pause contracts quickly limited damage. Can your integrations be frozen rapidly?
- Map contagion risk. If one protocol you depend on is compromised, what's the blast radius for your operations?
AI security tools are increasingly critical for detecting sophisticated attack patterns
The Bigger Picture: DeFi's Institutional Readiness
Every major DeFi hack sets back institutional adoption timelines. Insurance premiums rise. Compliance teams get more conservative. Boards ask harder questions about crypto treasury exposure.
The $290 million KelpDAO loss, combined with the $280 million Drift Protocol theft, means Lazarus Group has extracted over half a billion dollars from DeFi in 2026 alone. That's not noise. That's a pattern that shapes how CFOs evaluate emerging financial technology.
For enterprises genuinely exploring DeFi opportunities, the path forward involves accepting that security incidents will continue while building operational frameworks that contain exposure. Small experimental allocations. Strict protocol selection criteria. Real-time monitoring. And exit strategies that don't depend on protocol availability.
Logicity's Take
At Logicity, we build AI agents and automation systems for startups across India and the Gulf region. While we don't build DeFi protocols, we see direct parallels to infrastructure security in our client work. The KelpDAO attack exploited a classic distributed systems vulnerability: when verification nodes can be isolated and poisoned, the entire trust model collapses. We've implemented similar circuit-breaker patterns in n8n workflows and API integrations. The lesson for any business building on distributed infrastructure is this: you inherit the security posture of every dependency. That includes cloud providers, third-party APIs, and verification layers. For Indian startups exploring Web3 or handling sensitive financial data, this incident is a reminder that security architecture decisions made today determine your exposure to sophisticated attacks tomorrow. State-sponsored actors aren't just targeting crypto anymore. They're targeting any system where the payoff justifies the investment.
KelpDAO Hack FAQ: Questions Business Leaders Ask
Frequently Asked Questions
Can KelpDAO users recover their stolen funds?
Recovery is unlikely for most stolen funds. While blockchain forensics can trace transactions, the use of Tornado Cash mixing makes recovery extremely difficult. Some protocols maintain insurance funds for such events, but $290 million typically exceeds available coverage. Affected users should monitor KelpDAO's official communications for any compensation plans.
How does this affect other DeFi protocols we might use?
The immediate impact is contained to rsETH and protocols that accepted it as collateral. However, this attack methodology could target other cross-chain verification systems. Review your exposure to any protocol using LayerZero or similar cross-chain bridges. Major lending protocols like Aave responded appropriately by freezing affected assets quickly.
What due diligence should we perform before DeFi exposure?
Evaluate three layers: smart contract audits (necessary but insufficient), infrastructure security (RPC nodes, oracles, verification layers), and operational security (team background, incident response capabilities). Also assess contagion risk. Which other protocols accept the token as collateral? How quickly can operations be paused?
Is Lazarus Group targeting non-crypto companies too?
Yes. While crypto offers high-value, liquid targets, Lazarus Group has historically targeted banks, entertainment companies, and defense contractors. Any organization with significant digital assets or valuable intellectual property should assume state-sponsored actors are a relevant threat model.
What insurance options exist for DeFi-related losses?
Specialty crypto insurance exists but remains expensive and limited in coverage. Providers like Nexus Mutual offer on-chain coverage, while traditional insurers are slowly entering the market. Expect premiums to rise following incidents like this. Self-insurance through position sizing may be more practical for most organizations.
Enterprise hardware security considerations extend beyond traditional IT infrastructure
Need Help With Security Architecture?
Logicity builds secure AI agents and automation systems for startups navigating complex technology decisions. Whether you're evaluating infrastructure dependencies, implementing circuit-breaker patterns, or building monitoring systems for sensitive operations, our team brings practical experience from shipped projects across fintech and enterprise software. Let's discuss your security architecture.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read
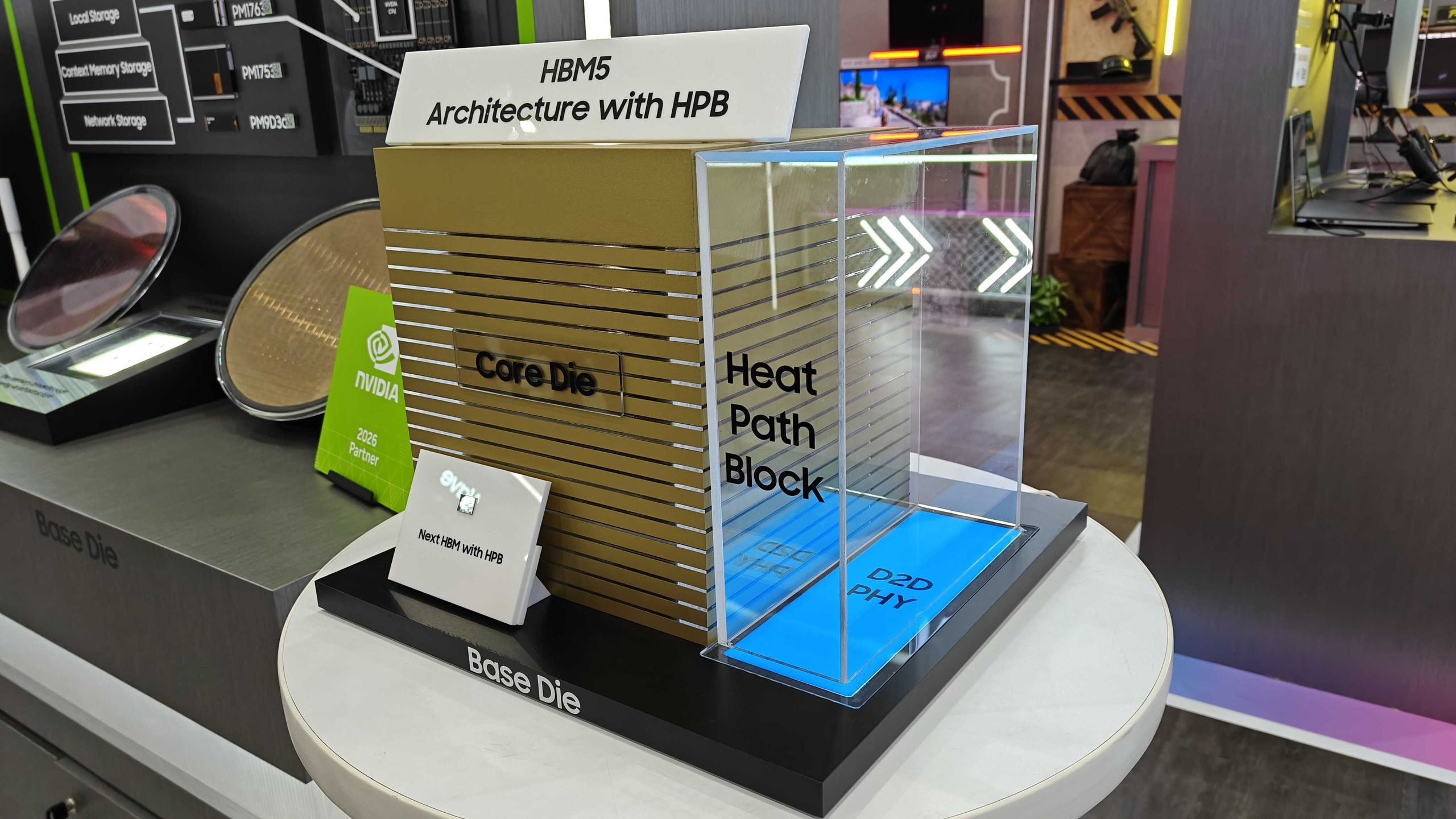
Samsung Shows HBM5 Mockup With Heat Path Block Cooling
Samsung unveiled its first physical HBM5 memory mockup at Computex 2026, featuring a new thermal design called Heat Path Block. The company confirmed it will manufacture HBM5's base die on its 2nm process, setting up a direct thermal engineering competition with SK hynix.

CISA Warns of Active Exploits Targeting Android, Linux Flaws
The U.S. Cybersecurity and Infrastructure Security Agency added two vulnerabilities to its Known Exploited Vulnerabilities catalog. Federal agencies must patch by June 5, 2026. The flaws affect Android 14-16 and multiple Linux kernel versions.

6 Ways to Stay Cool Indoors This Summer Without Breaking the Bank
As summer electricity bills hit a projected 12-year high of $784, homeowners are rethinking indoor cooling strategies. From supercooling techniques to strategic window management, here's how to survive the heat without destroying your budget.