Instructure Pays Hackers After Two Breaches Hit 275M Students
Key Takeaways
- ShinyHunters breached Instructure twice, stealing data on 275 million students and staff across 9,000 schools
- Instructure paid an undisclosed ransom for hackers to delete stolen data, despite government guidance against such payments
- Similar ransom payments by PowerSchool in 2024 failed to prevent further extortion of its customers
Instructure, the company behind the widely used Canvas learning management system, announced Tuesday it has reached an agreement with the hackers who breached its systems twice in two weeks. The deal comes after the cybercrime group ShinyHunters stole personal information on 275 million students and staff.
The company said hackers provided evidence that stolen data was destroyed. Instructure also stated that Canvas customers would not be extorted going forward. But the announcement raises serious questions about whether paying ransoms actually protects anyone.
What happened
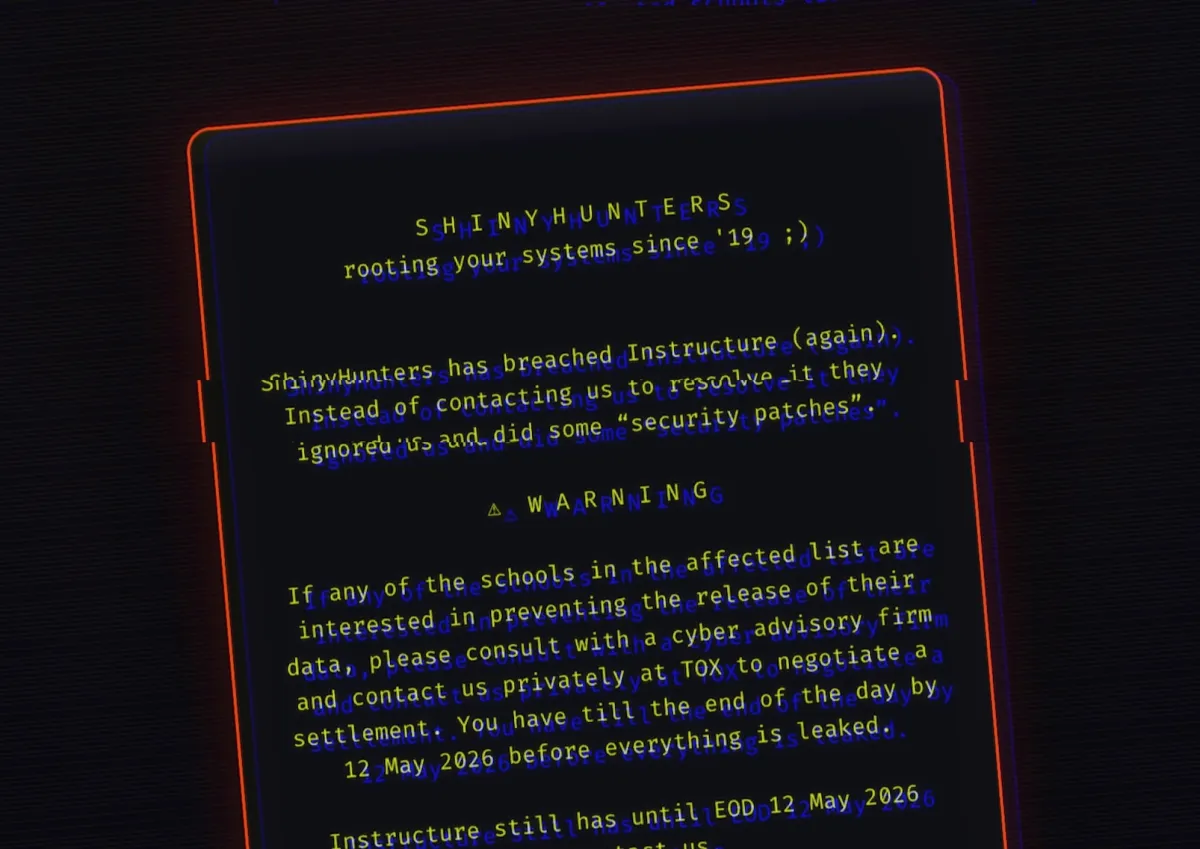
ShinyHunters, a financially motivated cybercrime group, claimed responsibility for the April 29 data breach. The group said it compromised Canvas, which nearly 9,000 schools use to manage student data and coursework. The stolen information included personal details on students and staff.
One week later, the hackers breached Instructure again. This time they defaced Canvas login pages on school websites. The move was designed to pressure the company into paying their ransom demand.
On its incident page late Monday, Instructure acknowledged there is "never complete certainty" when negotiating with cybercriminals. The company noted that customers should not have to engage with hackers directly.
Financial terms of the agreement were not disclosed. Instructure spokesperson Brian Watkins did not respond to requests for comment or answer questions about the deal.
Hackers claim data destroyed
Before the agreement, ShinyHunters threatened to publish the stolen data on its leak site if Instructure did not pay. As of Tuesday, that listing had been removed. This suggests a ransom was paid.
“The data is deleted, gone. The company and it's [sic] customers will not further be targeted or contacted for payment by us.”
— ShinyHunters representative to TechCrunch
The FBI said last week it was "aware" of the system disruption affecting schools and educational institutions around the United States.
Why paying ransoms is risky
The U.S. government has long urged cybercrime victims not to pay ransoms. These payments help criminals profit from attacks and fund future operations.
Security researchers argue victims cannot trust malicious hackers to keep their word. Some cybercriminals have held onto stolen data despite claiming they deleted it. They then continue extorting victims or sell the data to other groups.
The Instructure situation echoes a 2024 cyberattack on PowerSchool. That company, which also makes school information software, suffered a massive breach affecting 70 million students and staff. PowerSchool paid hackers to return stolen data. But several of its customers were later extorted by another crime group that possessed data from the breach. The data had not been destroyed.
The education sector's growing vulnerability
Schools and educational technology companies have become prime targets for cybercriminals. These organizations hold vast amounts of sensitive data. Personal information on minors is particularly valuable on dark web marketplaces.
Canvas serves nearly 9,000 schools. A single breach at Instructure can expose students and staff across thousands of institutions. These organizations often lack the security resources of large enterprises but hold equally sensitive data.
The PowerSchool and Instructure breaches both demonstrate a troubling pattern. EdTech companies that consolidate student data become single points of failure. When they get breached, the impact cascades across the entire education system.
Logicity's Take
What schools should do now
Schools that use Canvas should assume their data was compromised. Instructure has not disclosed which specific institutions were affected or what data was taken.
- Monitor student and staff accounts for signs of identity theft
- Review data sharing agreements with EdTech vendors
- Consider credit monitoring services for affected individuals
- Document the incident for potential regulatory reporting
- Evaluate vendor security practices before renewing contracts
The breach also highlights the need for schools to understand exactly what data they share with third-party platforms. Many institutions have limited visibility into how vendors store and protect sensitive information.
Frequently Asked Questions
How many people were affected by the Instructure Canvas breach?
ShinyHunters claimed to have stolen personal information on 275 million students and staff across nearly 9,000 schools that use Canvas.
Did Instructure pay a ransom to the hackers?
Instructure did not disclose financial terms, but the removal of stolen data from ShinyHunters' leak site and the hackers' statement suggest a payment was made.
Is the stolen student data actually destroyed?
ShinyHunters claims the data is deleted, and Instructure says hackers provided evidence of destruction. However, security experts warn that cybercriminals often retain copies despite such claims. The 2024 PowerSchool breach showed that paying ransoms does not guarantee data deletion.
What should schools using Canvas do now?
Schools should assume their data was compromised, monitor for identity theft, review vendor security agreements, and consider credit monitoring for affected students and staff.
Why do cybercriminals target schools?
Educational institutions hold large amounts of sensitive personal data, including information on minors. This data is valuable on dark web marketplaces, and schools often have fewer security resources than large corporations.
Need Help Implementing This?
Source: TechCrunch / Zack Whittaker
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read
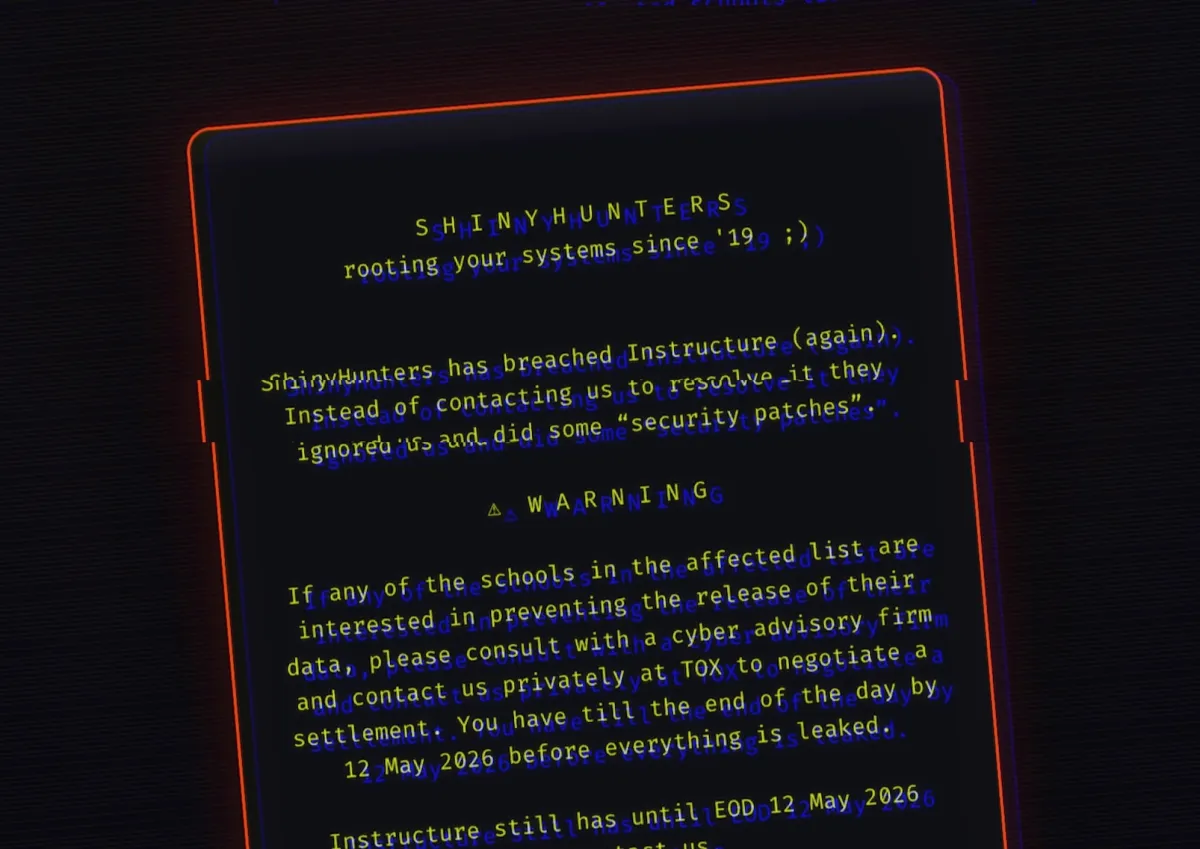
Build a Dynamic Gantt Chart in Excel Without Add-Ins
Project management software costs money. Excel does not. With structured tables, a few formulas, and conditional formatting, you can build a Gantt chart that updates automatically when tasks change. Here's the step-by-step method.

10 Outlook Hacks That Stop Email Tracking and Inbox Chaos
Microsoft Outlook has powerful features that most users never enable. From blocking email tracking pixels to automating inbox cleanup, these 10 hacks can transform how you manage your email.
Canvas Owner Pays Hackers After 275M Student Data Breach
Instructure, the company behind the Canvas learning management system, has reached an undisclosed 'agreement' with the ShinyHunters hacking group following a breach that exposed data from 275 million students. The company claims stolen data has been destroyed, but paying ransoms only funds future attacks.