Canvas Owner Pays Hackers After 275M Student Data Breach
Key Takeaways
- Instructure has reached an 'agreement' with ShinyHunters, almost certainly paying a ransom to prevent 3.65TB of student data from being leaked
- The breach affected approximately 9,000 educational institutions and 275 million individuals worldwide
- Security experts warn that paying ransoms funds future attacks and offers no guarantee hackers will keep their word
What Instructure Isn't Saying
Instructure, the company behind Canvas, has reached an 'agreement' with the hackers who stole 3.65 terabytes of student data last week. The company's statement stops short of admitting payment, but the language leaves little room for interpretation.
"We reached an agreement with the unauthorized actor involved in this incident," said Steve Daly, CEO of Instructure. "The data was returned to us. We received digital confirmation of data destruction."
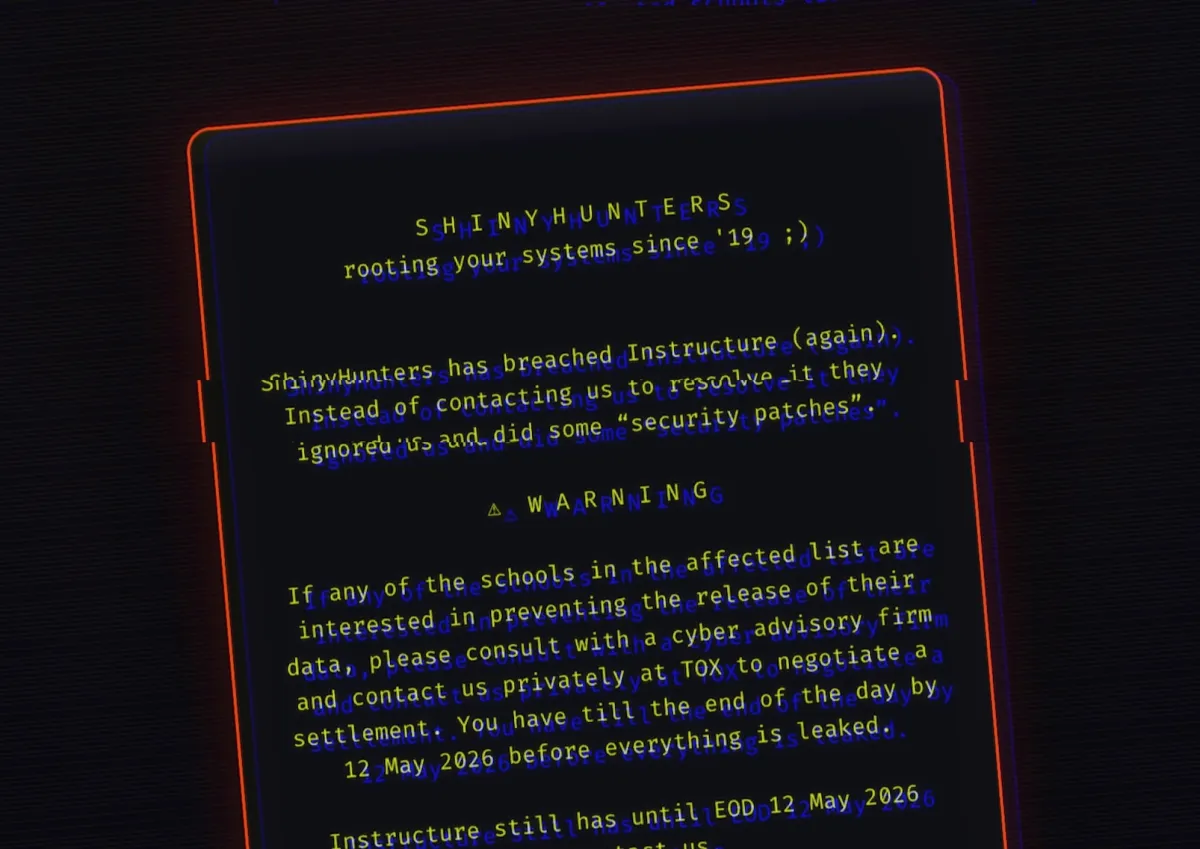
The ShinyHunters hacking group claimed responsibility for the attack and threatened to publish the stolen data if ransom demands weren't met. Now Instructure says no customers will be extorted as a result of the breach. The company has promised to share more details in a webinar scheduled for tomorrow.
The Scale of the Breach
The numbers are staggering. According to threat analysts, approximately 9,000 educational institutions worldwide were affected. The stolen data included billions of private messages between students and teachers.
“The hacking group posted online that nearly 9,000 schools worldwide were affected, with billions of private messages and other records accessed.”
— Luke Connolly, Threat Analyst at Emsisoft
Canvas holds 41% of the North American higher education LMS market. That concentration made it a massive single point of failure. When ShinyHunters exploited vulnerabilities in Canvas's Free-For-Teacher accounts, they gained access to an enormous trove of sensitive educational data.
The timing was deliberate. The attack hit during U.S. university finals week, maximizing chaos and pressure on Instructure to pay quickly. Students across the country found themselves locked out of their learning platforms mid-exam.
Full coverage of the Canvas breach timeline and impact
Why Paying Ransoms Is a Problem
Instructure's decision to negotiate with ShinyHunters follows a familiar playbook in corporate ransomware response. Companies facing massive data leaks often calculate that paying is cheaper than the reputational and legal costs of exposure. But security experts consistently warn against this approach.
“Paying a ransom offers no guarantee that stolen data will be protected... it only reinforces the attackers' confidence.”
— Mohiuddin Ahmed, Associate Professor in Cybersecurity at Adelaide University
Ransom payments directly fund future attacks. Every successful extortion validates the business model and finances the tools, infrastructure, and personnel for the next target. The ransomware business is booming even as law enforcement shuts down some major players.
There's also the trust problem. Instructure says it received "digital confirmation of data destruction" and that stolen data was "returned." But how do you return data that was copied? Shred logs can be faked. Criminal organizations have no legal obligation to honor agreements. The company is taking ShinyHunters at their word, which is a significant gamble with 275 million people's personal information.
How the Attack Happened
The breach exploited a vulnerability in Canvas's Free-For-Teacher tier. These accounts, designed to give individual educators access to the platform without institutional contracts, apparently lacked the security audits applied to enterprise deployments.
Instructure has not announced when Free-For-Teacher accounts will be restored. The company temporarily shut down the feature as part of its incident response. Most other Canvas systems have since come back online.
The attack highlights a recurring problem in software-as-a-service products: security tiers. Free and low-cost accounts often receive less scrutiny, but they share infrastructure with enterprise customers. A weakness in one tier can compromise the entire platform.
What Happens Next
Instructure says it's working with "expert vendors" to conduct forensic analysis and harden its environment. The company plans to share more information in tomorrow's webinar, though it's unclear how much detail will be provided about the nature of the agreement or the ransom amount.
For the 9,000 affected institutions, the immediate crisis may be over, but longer-term questions remain. Was student data actually destroyed? Will it surface on dark web marketplaces in six months? How will institutions verify that their specific data is secure?
Instructure's statement tries to reassure: "While there is never complete certainty when dealing with cyber criminals, we believe it was important to take every step within our control to give customers additional peace of mind." That's honest about the limitations, but it's cold comfort for students whose private messages may still be in criminal hands.
Logicity's Take
Frequently Asked Questions
Frequently Asked Questions
Did Instructure pay a ransom to the Canvas hackers?
Instructure hasn't explicitly confirmed payment, but the company's statement about reaching an 'agreement' with ShinyHunters strongly implies a ransom was paid. The company says stolen data has been 'returned' and destroyed.
How many people were affected by the Canvas data breach?
Approximately 275 million individuals had data compromised, across roughly 9,000 educational institutions worldwide. The stolen data totaled 3.65 terabytes, including billions of private student-teacher messages.
Is Canvas safe to use now?
Most Canvas systems have been restored, and Instructure says it's working to harden its environment. However, Free-For-Teacher accounts remain suspended, and the company hasn't detailed what specific security changes have been implemented.
Who is ShinyHunters?
ShinyHunters is a known hacking group that has been linked to multiple high-profile data breaches. They specialize in stealing and selling data, and increasingly in ransomware-style extortion.
Will the stolen student data appear online?
Instructure claims ShinyHunters provided proof of data destruction, but there's no way to verify criminals will honor their agreement. Data could still surface on dark web marketplaces despite the 'agreement.'
Need Help Implementing This?
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read
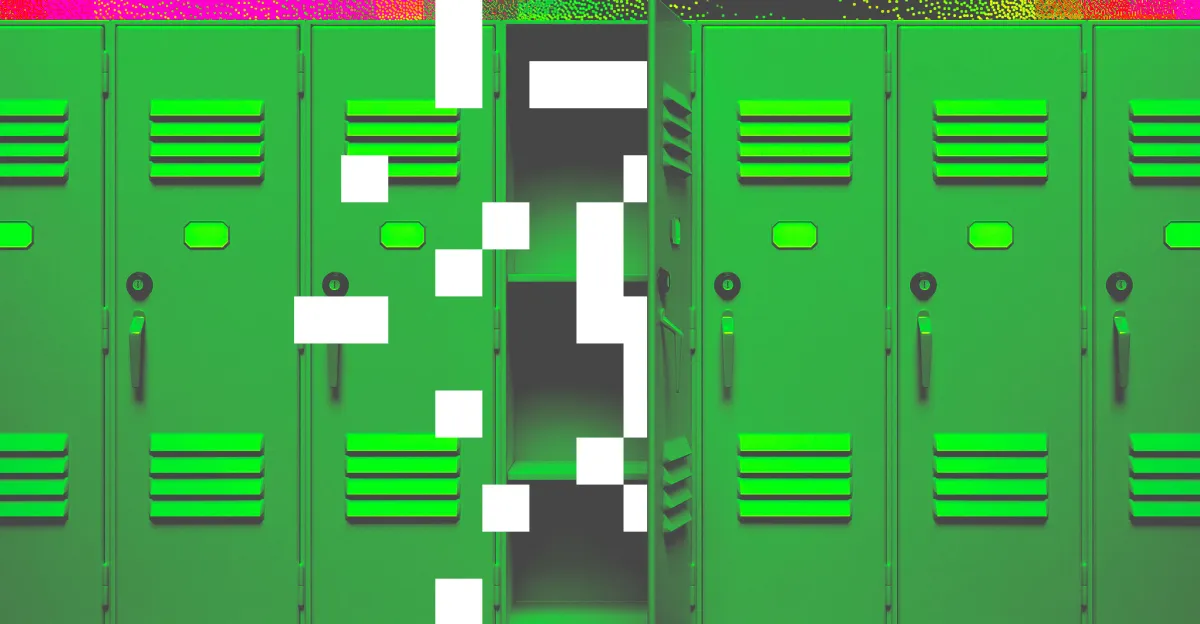
Build a Dynamic Gantt Chart in Excel Without Add-Ins
Project management software costs money. Excel does not. With structured tables, a few formulas, and conditional formatting, you can build a Gantt chart that updates automatically when tasks change. Here's the step-by-step method.

10 Outlook Hacks That Stop Email Tracking and Inbox Chaos
Microsoft Outlook has powerful features that most users never enable. From blocking email tracking pixels to automating inbox cleanup, these 10 hacks can transform how you manage your email.
Instructure Pays Hackers After Two Breaches Hit 275M Students
Canvas maker Instructure reached a deal with ShinyHunters, the cybercrime group that breached its systems twice and stole data on 275 million students and staff. The company says hackers provided evidence the data was destroyed, but security experts warn ransom payments rarely guarantee safety.