cPanel Flaw Exploited in Mass 'Sorry' Ransomware Attacks

Key Takeaways

- A critical cPanel flaw (CVE-2026-41940) has been exploited to compromise at least 44,000 servers
- The Sorry ransomware uses ChaCha20 encryption with RSA-2048 key protection, making decryption without the private key impossible
- All cPanel and WHM users must install emergency security updates immediately
A newly disclosed cPanel vulnerability is being mass-exploited to breach web servers and deploy ransomware. The flaw, tracked as CVE-2026-41940, allows attackers to bypass authentication and gain access to hosting control panels. From there, they encrypt website data and demand ransom payments.
cPanel and WHM released an emergency patch this week. But the damage has already spread. Internet security watchdog Shadowserver reports that at least 44,000 IP addresses running cPanel have been compromised in ongoing attacks.
How the Attack Works
WHM and cPanel are Linux-based web hosting control panels used for server and website management. WHM provides server-level control. cPanel gives administrators access to website backends, webmail, and databases. Together, they power a significant chunk of the web hosting industry.
The authentication bypass flaw lets attackers access these control panels without valid credentials. Once inside, they have the keys to the kingdom. They can access files, databases, and email systems. In this campaign, they're using that access to deploy ransomware.
According to BleepingComputer, exploitation began as a zero-day. Attackers were hitting servers as early as late February. That's months before the flaw was publicly disclosed and patched.
The Sorry Ransomware
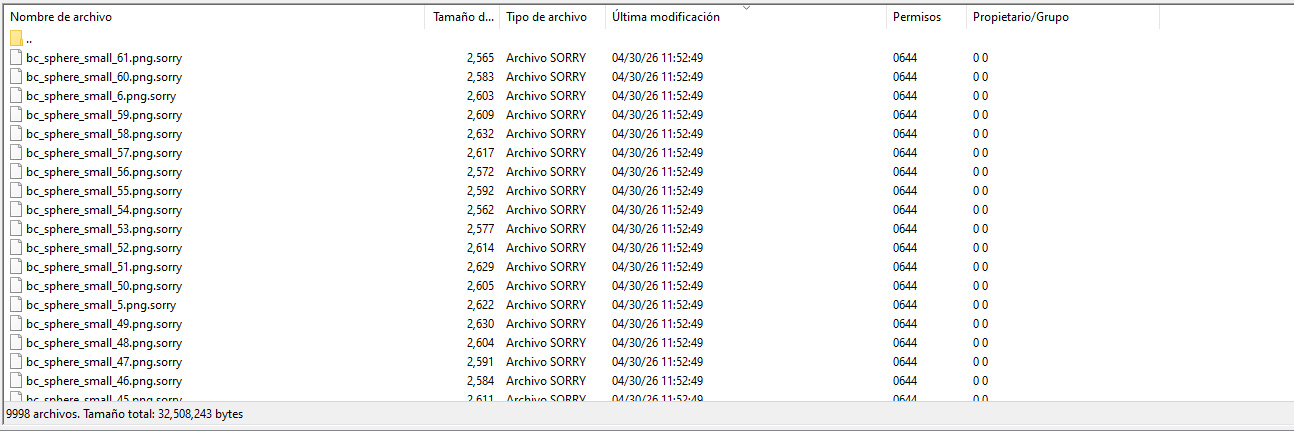
The attackers are deploying a Go-based Linux encryptor for the "Sorry" ransomware. The malware appends the ".sorry" extension to all encrypted files.
The encryption is serious. Sorry ransomware uses the ChaCha20 stream cipher to lock files. The encryption key itself is protected using an embedded RSA-2048 public key. Without the corresponding private key, decryption is impossible.
“Decryption is impossible without an RSA-2048 private key.”
— Rivitna, ransomware expert, on BleepingComputer forums
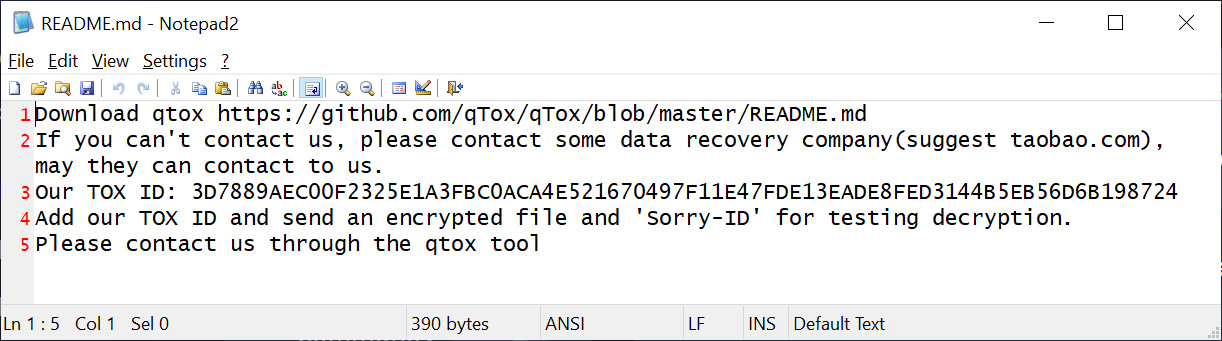
In each folder, the malware drops a ransom note named README.md. The note instructs victims to contact the threat actor via Tox, an encrypted messaging platform, to negotiate payment. The same Tox ID appears in all ransom notes, confirming this is a coordinated campaign rather than isolated attacks.
Scale of the Attack
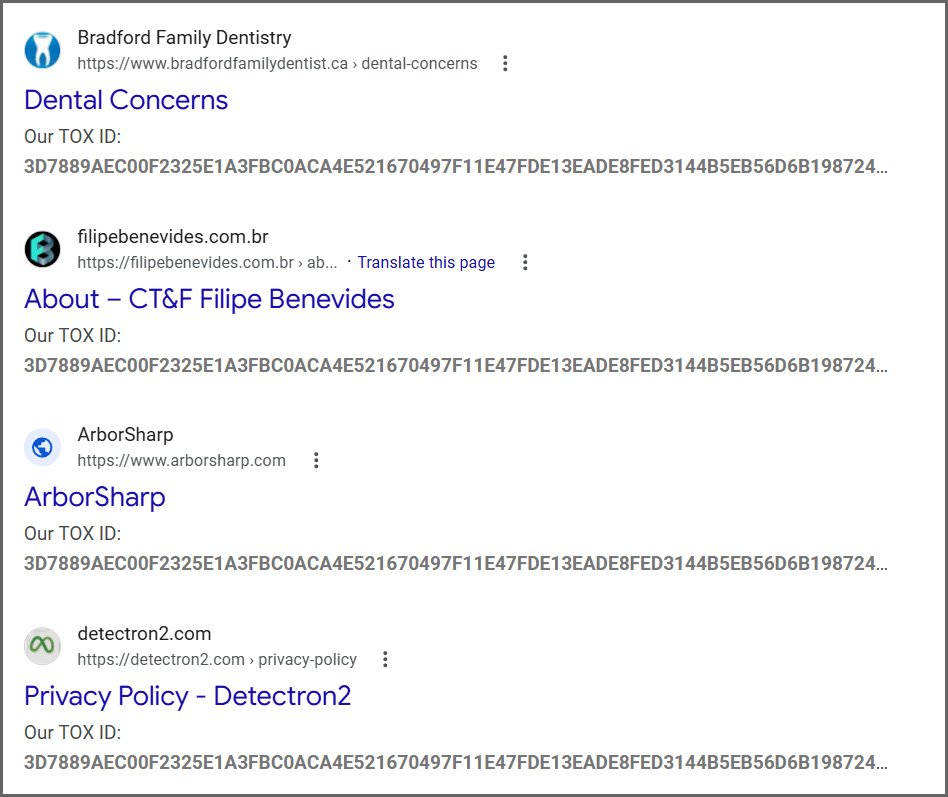
The damage is already visible. Hundreds of compromised websites are indexed in Google search results, their pages replaced with ransom notes or error messages.
Reports have flooded forums like BleepingComputer, with victims sharing encrypted file samples and ransom note contents. The attacks started Thursday and have continued since.
Not the First 'Sorry' Ransomware
A 2018 ransomware campaign also used the .sorry file extension. That attack used a HiddenTear-based encryptor. This current campaign is unrelated. It uses a completely different, more sophisticated encryptor built in Go.
What You Should Do Now
If you run cPanel or WHM, install the emergency security update immediately. The patch addresses CVE-2026-41940 and closes the authentication bypass.
- Check your cPanel/WHM version and apply all available security updates
- Review server logs for suspicious access patterns, especially from late February onward
- Verify backup integrity. If backups are clean and stored offline, recovery is possible without paying ransom
- Monitor for .sorry file extensions or README.md ransom notes appearing in directories
- Consider restricting cPanel access to specific IP addresses or VPN connections
For servers already compromised, isolate them from the network to prevent lateral movement. Contact a security professional before attempting recovery.
Related security topic on default configuration risks
Logicity's Take
Frequently Asked Questions
What is CVE-2026-41940?
CVE-2026-41940 is a critical authentication bypass vulnerability in cPanel and WHM that allows attackers to access hosting control panels without valid credentials. An emergency patch was released this week.
Can files encrypted by Sorry ransomware be decrypted?
No, not without the attacker's private RSA-2048 key. The ransomware uses ChaCha20 encryption with RSA-2048 key protection, making brute-force decryption impossible with current technology.
How do I know if my cPanel server is compromised?
Look for files with the .sorry extension and README.md ransom notes in your directories. Review access logs for unauthorized logins, especially since late February when exploitation began.
Is this related to the 2018 Sorry ransomware?
No. The 2018 campaign used a HiddenTear-based encryptor. This current campaign uses a different Go-based Linux encryptor and is unrelated despite sharing the same file extension.
How many servers have been affected?
Shadowserver reports at least 44,000 IP addresses running cPanel have been compromised. Hundreds of affected websites are already visible in Google search results.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

5 Smartphone Deals Worth Checking Before Mother's Day
With Mother's Day on Sunday, major retailers are discounting flagship phones from Nothing, Samsung, and Google. The Nothing Phone (3) leads with a $200 price cut, while Pixel 10 and Galaxy S26 models also see solid discounts.

Projectivy Launcher Ditches Google TV Bloat for Speed
Google TV's home screen comes loaded with trailers, recommendations, and background processes that slow things down. A free launcher replacement called Projectivy strips all that away, delivering a faster, cleaner interface without requiring advanced technical skills.

3 Android Security Features Disabled by Default
Android ships with powerful theft protection and privacy tools that most users never discover. Google buries Theft Detection Lock, Private Space, and other genuinely useful features in settings menus, leaving phones less secure than they could be.