Breeze Cache Plugin Bug Under Active Attack: Update Now

Key Takeaways

- CVE-2026-3844 has a severity score of 9.8/10 and allows remote code execution
- Wordfence has blocked over 170 exploitation attempts so far
- Update to Breeze Cache 2.4.5 or disable the Gravatars add-on immediately
What's Happening
Hackers are actively exploiting a critical vulnerability in Breeze Cache, a popular WordPress caching plugin from Cloudways. The flaw lets attackers upload malicious files to servers without logging in. That can lead to full website takeover.
Security firm Wordfence has already blocked more than 170 exploitation attempts. The vulnerability, tracked as CVE-2026-3844, carries a severity score of 9.8 out of 10. It affects all Breeze Cache versions up to and including 2.4.4.
Why Breeze Cache Matters
Breeze Cache has more than 400,000 active installations. Website owners use it to speed up page loads through caching, file optimization, and database cleanup. It's a standard performance tool for WordPress sites that need faster response times.
That install base makes this vulnerability a big deal. Even if a small percentage of sites remain unpatched, attackers have a large target surface.
How the Exploit Works
Researchers at Defiant, the company behind Wordfence, traced the problem to missing file-type validation. The vulnerable function is called 'fetch_gravatar_from_remote'. Because the plugin doesn't check what type of file is being uploaded, attackers can push executable code to the server.
Once malicious code is on the server, attackers can run it remotely. This gives them full control over the website. They can steal data, inject malware, redirect visitors, or use the site as a launch point for further attacks.
There's one catch. The exploit only works if the "Host Files Locally - Gravatars" add-on is turned on. This setting is off by default. So sites that never enabled it are not vulnerable, even if they run an outdated Breeze Cache version.
The Fix Is Available
Cloudways released version 2.4.5 earlier this week. This version patches the vulnerability. According to WordPress.org stats, the plugin has had about 138,000 downloads since the fix dropped.
That still leaves a gap. With 400,000 active installations, many sites haven't updated yet. And there's no public data on how many have the Gravatars add-on enabled.
What You Should Do Now
- Update Breeze Cache to version 2.4.5 immediately through your WordPress dashboard
- If you can't update right now, disable the "Host Files Locally - Gravatars" add-on
- If you can't do either, consider temporarily deactivating the plugin until you can patch
- Check your server logs for unusual file uploads or unexpected PHP files in the Breeze directory
Security researcher Hung Nguyen (bashu) discovered and reported the flaw. Responsible disclosure gave Cloudways time to build a patch before exploitation ramped up.
Broader WordPress Security Context
This incident fits a pattern. WordPress plugins are frequent targets because they're widely used and often maintained by small teams. When a popular plugin has a critical flaw, attackers move fast. Automated scanners can identify vulnerable sites within hours of a public disclosure.
The 170 blocked attempts Wordfence recorded likely represent a fraction of total attack traffic. Sites without active security monitoring may not know they've been probed or compromised.
Another recent example of software supply chain security risks
Logicity's Take
Frequently Asked Questions
Is my site vulnerable if I use Breeze Cache?
Only if you're running version 2.4.4 or earlier AND have the "Host Files Locally - Gravatars" add-on enabled. The add-on is off by default.
What can attackers do if they exploit this vulnerability?
They can upload and execute arbitrary files on your server. This leads to remote code execution, which means full website takeover, data theft, malware injection, or using your site to attack others.
How do I update Breeze Cache?
Go to your WordPress dashboard, navigate to Plugins, find Breeze, and click Update. You should see version 2.4.5 available.
What if I can't update right away?
Disable the "Host Files Locally - Gravatars" add-on in Breeze settings. This closes the attack path until you can install the patch.
How do I know if my site was already compromised?
Check your server logs for unexpected file uploads. Look for unfamiliar PHP files in the Breeze plugin directory. Consider running a malware scan with a tool like Wordfence.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read
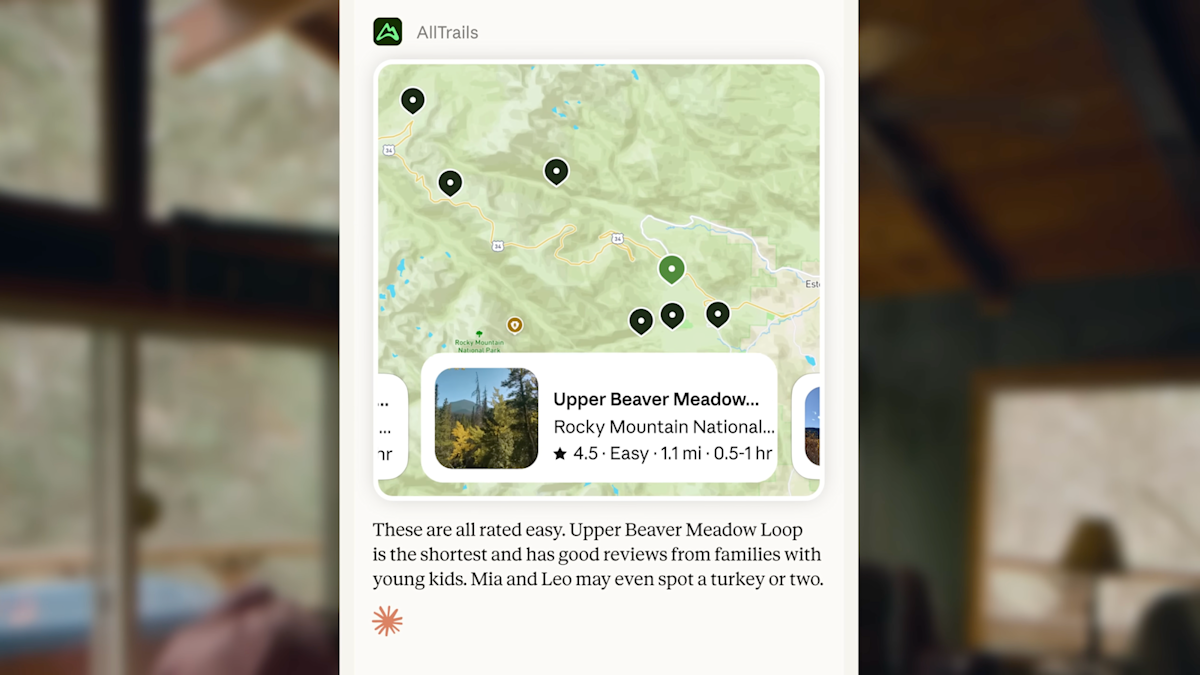
Claude AI Adds 15 Lifestyle Apps Including Spotify and Uber
Anthropic has expanded Claude's third-party integrations beyond professional tools to everyday services. The AI chatbot can now connect to Spotify, Instacart, Uber, AllTrails, and 11 other consumer apps to help users plan activities and make purchases.
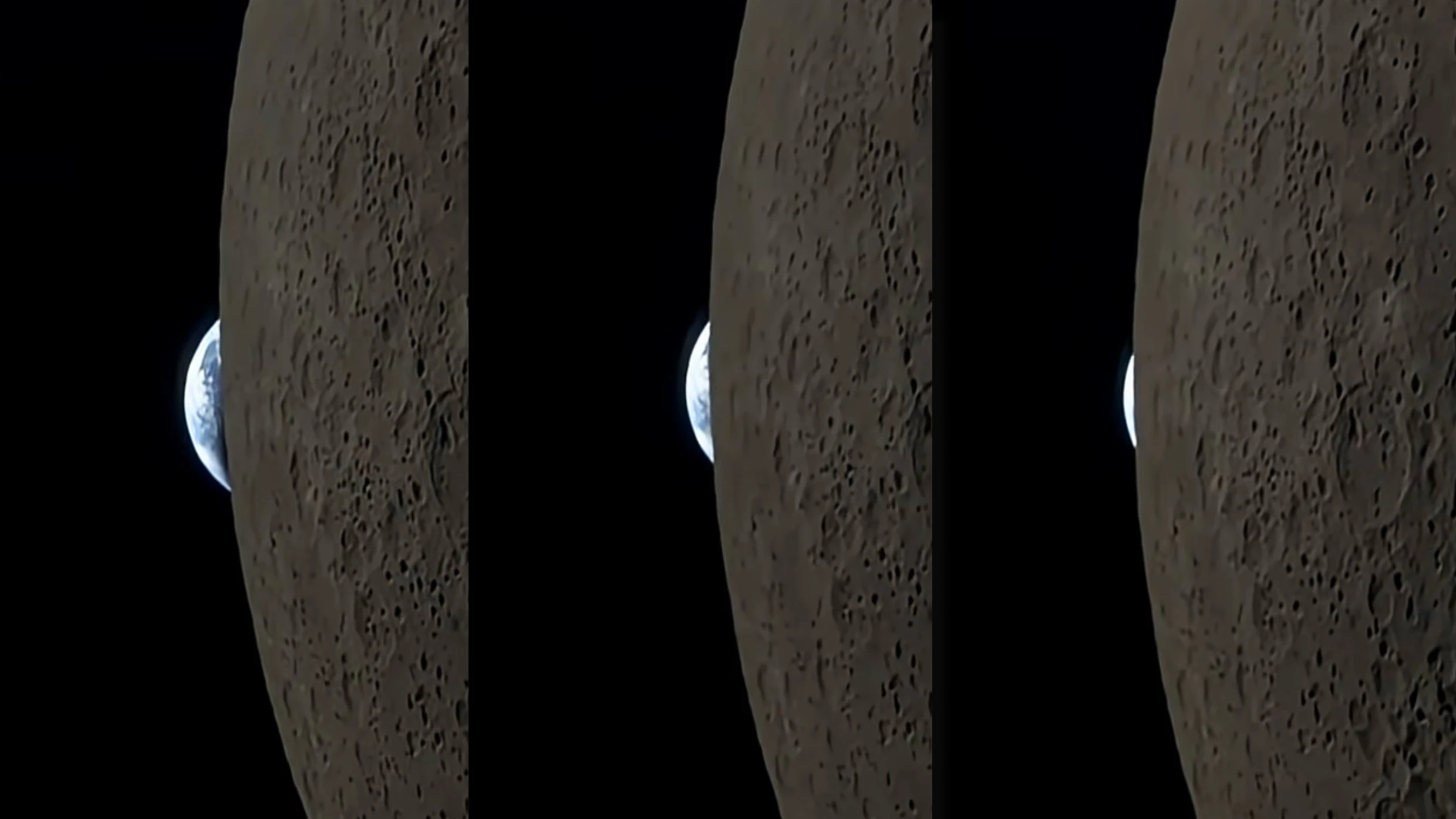
NASA's iPhone Moon Video Becomes Apple's Best Free Ad
Astronaut Reid Wiseman filmed Earth setting behind the moon on an iPhone 17 Pro Max during the Artemis II mission. The viral video showcases how consumer tech now meets space-grade demands, but NASA's public domain rules create an unusual marketing situation for Apple.

How to Enable Tablet Mode on Your Samsung Phone
Samsung phones hide a tablet-like experience behind two settings most users never find. Enabling landscape home screen and adjusting display density transforms how apps display content on larger Galaxy screens.