Checkmarx KICS Supply Chain Breach Steals Dev Credentials

Key Takeaways

- Docker images and VS Code extensions for KICS were compromised to steal cloud credentials and tokens
- The dangerous Docker Hub window was April 22, 14:17:59 to 15:41:31 UTC
- Affected developers should rotate all secrets and rebuild environments immediately
What Happened
Attackers compromised the official Docker images, VS Code extensions, and Open VSX extensions for Checkmarx KICS. The goal: harvest credentials from developer machines running the popular infrastructure-as-code security scanner.
KICS (Keeping Infrastructure as Code Secure) is a free, open-source tool that scans source code, dependencies, and configuration files for security vulnerabilities. Developers typically run it locally through CLI or Docker. The tool processes sensitive infrastructure configs that often contain credentials, tokens, and internal architecture details. That makes it a perfect target.
Dependency security firm Socket investigated after Docker alerted them to malicious images pushed to the official checkmarx/kics Docker Hub repository. The compromise ran deeper than just Docker. The VS Code and Open VSX extensions had been modified to download a hidden "MCP addon" feature that fetched credential-stealing malware.
How the Attack Worked
Socket found that the MCP addon feature downloaded from a hardcoded GitHub URL what they described as "a multi-stage credential theft and propagation component" named mcpAddon.js.
The malware targeted exactly the data that KICS processes:
- GitHub tokens
- AWS, Azure, and Google Cloud credentials
- npm tokens
- SSH keys
- Claude configs
- Environment variables
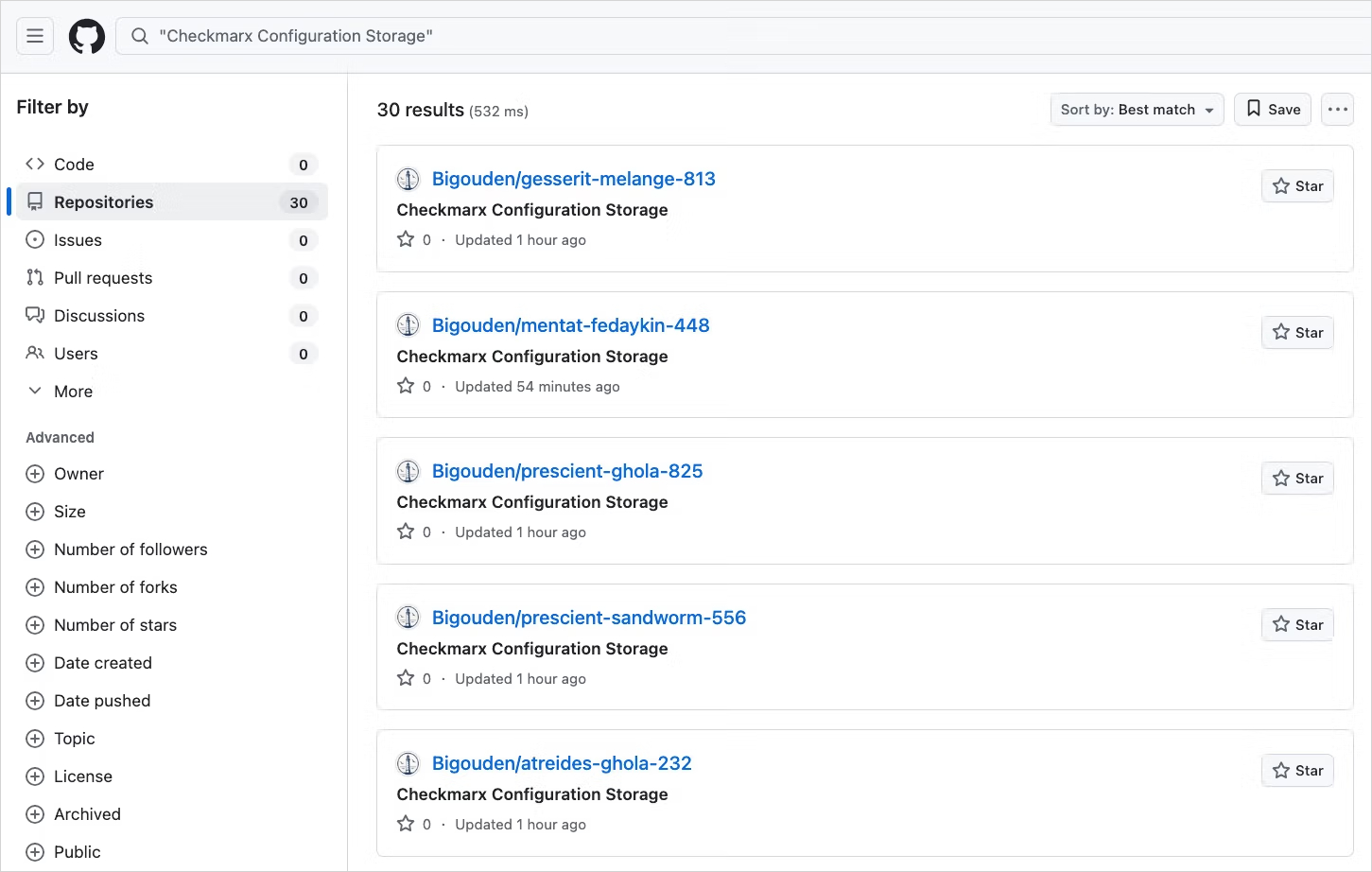
After collection, the malware encrypted the stolen data and sent it to audit.checkmarx[.]cx. That domain was designed to look like legitimate Checkmarx infrastructure. The attackers also automatically created public GitHub repositories for data exfiltration.
The Attack Window
Docker tags were temporarily repointed to a malicious digest. The dangerous timeframe for the Docker Hub KICS image was narrow but damaging: April 22, 2026, from 14:17:59 UTC to 15:41:31 UTC. That's about 83 minutes.
Affected tags have been restored to their legitimate image digests. The fake v2.1.21 tag was deleted entirely.
Who's Behind It
A group called TeamPCP publicly claimed responsibility for the attack. This same group was behind the recent massive Trivy and LiteLLM supply-chain compromise. However, Socket's researchers could not find sufficient evidence beyond pattern-based correlations to confidently attribute it.
Related coverage on security measures in developer tooling
What Checkmarx Says
Checkmarx published a security bulletin about the incident. The company says all malicious artifacts have been removed and their exposed credentials were revoked and rotated. The firm is investigating with help from external experts and has promised to provide more information as it becomes available.
BleepingComputer reached out to Checkmarx for comment, but the company had not responded at publication time.
What You Should Do Now
If you pulled the KICS Docker image or installed the VS Code/Open VSX extensions during the affected window, consider your secrets compromised. Here's your action list:
- Rotate all credentials that may have been exposed: GitHub tokens, cloud provider credentials (AWS, Azure, GCP), npm tokens, SSH keys
- Audit your environment variables for anything sensitive
- Rebuild your development environment from a known safe point
- Check your CI/CD pipelines that use KICS for any pulls during the attack window
- Review your AWS CloudTrail, Azure Activity Log, and GCP Audit Logs for suspicious activity
Even if you're not certain you were affected, rotating credentials as a precaution is reasonable given the sensitivity of what KICS typically accesses.
Additional security practices for developers
The Bigger Picture
This attack follows a pattern we've seen increasingly in 2026. Attackers are targeting the tools developers trust to secure their code. The irony is intentional. A tool designed to find security vulnerabilities becomes the vector for compromise.
Supply chain attacks on developer tools are attractive because they offer access to credentials for production systems. A compromised developer laptop often holds keys to cloud infrastructure, source code repositories, and deployment pipelines.
Logicity's Take
Frequently Asked Questions
Was the Checkmarx KICS supply chain attack fixed?
Yes. Checkmarx has restored the affected Docker tags to legitimate image digests, deleted the malicious v2.1.21 tag, and removed malicious VS Code and Open VSX extensions. The company has also revoked and rotated their own exposed credentials.
How do I know if I was affected by the KICS breach?
Check if you pulled the Docker image from checkmarx/kics or installed the VS Code/Open VSX extensions between April 22, 2026, 14:17:59 UTC and 15:41:31 UTC. Also check your CI/CD pipeline logs for automated pulls during that window.
What credentials were stolen in the Checkmarx attack?
The malware targeted GitHub tokens, AWS/Azure/Google Cloud credentials, npm tokens, SSH keys, Claude configs, and environment variables. It specifically harvested the types of secrets that KICS typically processes.
Who was behind the Checkmarx KICS attack?
A group called TeamPCP publicly claimed responsibility. They were also linked to the Trivy and LiteLLM supply chain compromises. However, researchers have not been able to definitively confirm attribution beyond pattern-based correlations.
Should I stop using Checkmarx KICS?
The current versions are clean. This was a supply chain compromise of the distribution channel, not a flaw in KICS itself. Verify you're pulling from restored legitimate sources and continue using the tool.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

First Intel Wildcat Lake Laptop Spotted: MacBook Neo Rival
Intel's new Wildcat Lake reference laptop has surfaced, featuring an aluminum chassis and 11W fanless mode. The device packs 16GB RAM and targets Apple's ultra-thin MacBook Neo, though with a much higher power envelope.

OpenAI Launches Trusted Access Program for Microsoft Cyber Defense
OpenAI will give Microsoft access to its most capable AI models through a new 'Trusted Access for Cyber' program. In exchange, Microsoft commits its entire cybersecurity team to protecting OpenAI's infrastructure and models. The partnership arrives as the industry debates how effective large language models really are at security tasks.
6 CLI Tools That Replace Boring Linux Defaults
The standard Linux terminal utilities are functional but dull. A Linux veteran shares the six command-line replacements he installs on every new system for better readability, faster searches, and syntax highlighting.