Apache ActiveMQ Vulnerability: 6,400 Servers at Risk

Key Takeaways

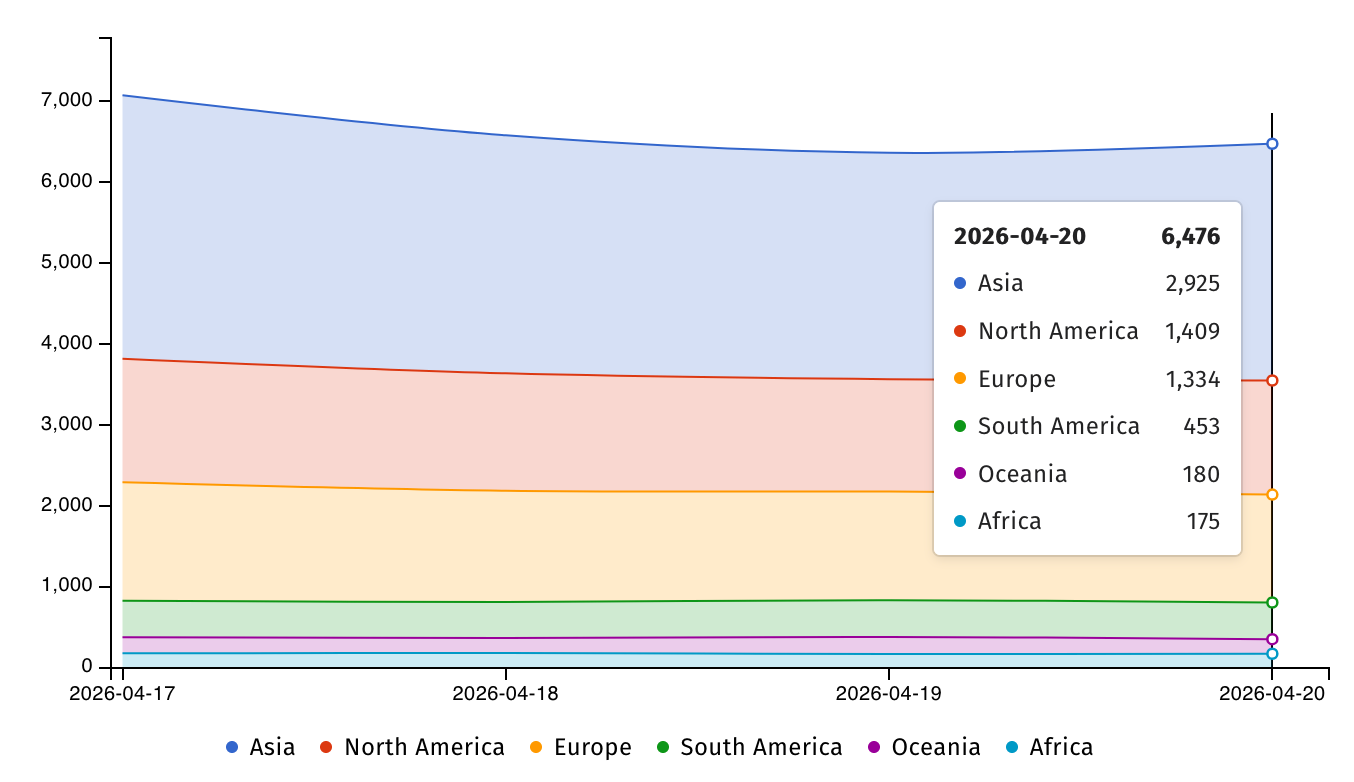
- Over 6,400 servers are exposed and actively being targeted by attackers
- The vulnerability remained undetected for 13 years before AI-assisted discovery
- CISA has mandated federal agencies patch by April 30, 2026
Read in Short
Apache ActiveMQ, the backbone of enterprise Java messaging, has a 13-year-old critical vulnerability now under active attack. 6,400+ servers are exposed globally. If your company uses ActiveMQ for application communication, your security team needs to patch to version 6.2.3 or 5.19.4 immediately. CISA considers this threat serious enough to mandate federal compliance by April 30.
According to [BleepingComputer](https://www.bleepingcomputer.com/news/security/actively-exploited-apache-activemq-flaw-impacts-6-400-servers/), over 6,400 Apache ActiveMQ servers exposed online are vulnerable to ongoing attacks exploiting a high-severity code injection vulnerability that remained undetected for 13 years. This isn't a theoretical risk. Attackers are actively exploiting this flaw right now, and the U.S. government considers it serious enough to issue emergency directives.
What Is the Apache ActiveMQ Vulnerability CVE-2026-34197?
Apache ActiveMQ is the most popular open-source message broker for enterprise Java applications. Think of it as the postal service for your internal systems. When your e-commerce platform needs to talk to your inventory system, or when your payment processor needs to communicate with your fulfillment center, ActiveMQ handles those messages. It's infrastructure that's invisible when it works and catastrophic when it fails.
The vulnerability, tracked as CVE-2026-34197, was discovered by Horizon3 researcher Naveen Sunkavally using Claude AI. The flaw stems from improper input validation, which allows authenticated attackers to execute arbitrary code on unpatched systems. In plain business terms: if someone gains even basic access to your ActiveMQ server, they can run whatever code they want. That means data theft, ransomware deployment, or using your systems as a launchpad for attacks on your partners and customers.
Why Should CEOs Care About This Security Flaw?
This isn't just another security advisory to file away. Here's why this vulnerability demands executive attention.
First, the attack surface is massive. Over 6,400 servers are exposed globally, with the highest concentrations in Asia (2,925), North America (1,409), and Europe (1,334). If your company operates in these regions and uses Java-based enterprise applications, there's a real chance you're running ActiveMQ somewhere in your stack.
Second, this follows a pattern. CISA has tagged two other ActiveMQ vulnerabilities as exploited in the wild in recent years. One of them, CVE-2023-46604, was targeted by the TellYouThePass ransomware gang as a zero-day. Attackers know ActiveMQ well. They have established playbooks for exploiting it and monetizing that access through ransomware.
Third, the regulatory pressure is real. CISA has ordered all Federal Civilian Executive Branch agencies to secure their servers by April 30. If you do business with the federal government, your security posture is now under scrutiny. Even if you don't, this directive signals the severity that regulators assign to this vulnerability.
How Much Could an ActiveMQ Breach Cost Your Business?
Let's talk numbers. The average cost of a data breach in 2025 exceeded $4.5 million globally, according to IBM's annual report. For enterprises with exposed message brokers handling sensitive transaction data, the costs compound quickly.
| Cost Category | Typical Range | ActiveMQ-Specific Risk |
|---|---|---|
| Incident Response | $50K - $500K | High complexity due to integration depth |
| Business Interruption | $100K - $2M per day | Message broker downtime stops all dependent systems |
| Regulatory Fines | $50K - $20M+ | GDPR, HIPAA, PCI-DSS all apply to transaction data |
| Reputation Damage | 5-15% customer churn | Supply chain attacks erode partner trust |
| Ransomware Payment | $200K - $5M | TellYouThePass gang has targeted ActiveMQ before |
The real danger isn't just the direct costs. ActiveMQ often sits at the heart of transaction processing. A compromised message broker can poison data flowing between systems, creating errors that cascade through your operations for weeks before anyone notices the source.
What's the Patch Timeline for Apache ActiveMQ?
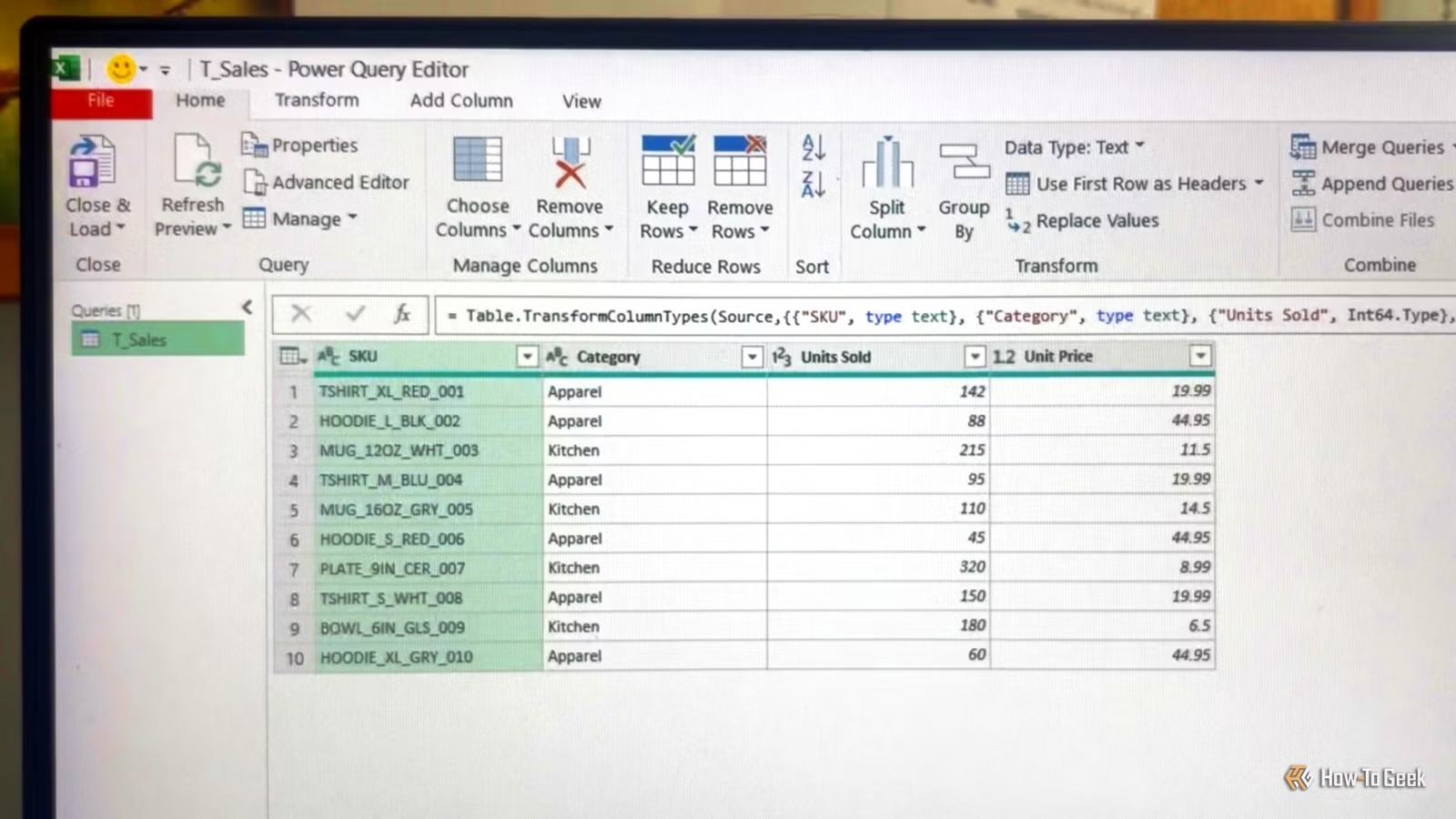
Apache maintainers released patches on March 30, 2026. The fixed versions are ActiveMQ Classic 6.2.3 and 5.19.4. If you're running anything older, you're exposed.
The three-week gap between patch release and active exploitation confirmation is notable. It suggests attackers were either already aware of the vulnerability or moved quickly to reverse-engineer the patch and develop exploits. Either way, the window for safe patching is closing rapidly.
How to Check If Your Company Is Affected
For technical teams, Horizon3 researchers have provided specific detection guidance. Search your ActiveMQ broker logs for suspicious broker connections using the internal transport protocol VM combined with the brokerConfig=xbean:http:// query parameter. These are indicators of exploitation attempts.
Immediate Actions for IT Leadership
1. Identify all ActiveMQ instances in your environment, including shadow IT and partner integrations. 2. Check version numbers against patched releases (6.2.3 or 5.19.4). 3. Review broker logs for exploitation indicators. 4. Prioritize internet-facing instances for immediate patching. 5. If patching isn't possible, CISA recommends discontinuing use of the product.
The challenge for many organizations is that ActiveMQ often runs in legacy systems or vendor-managed environments where patching requires coordination and testing. If your enterprise resource planning system or customer data platform relies on ActiveMQ, you may need to work with vendors to confirm their patch status.
What This AI Discovery Means for Future Security
One detail in this story deserves executive attention: the vulnerability was discovered using Claude AI after remaining hidden for 13 years. This signals a shift in how security research works and what it means for your risk profile.
AI-assisted security research can find bugs that human reviewers missed for over a decade. That's powerful when the good guys use it. It's concerning when you realize attackers have access to the same tools. The implication for business leaders is that vulnerability discovery will accelerate. Legacy codebases that felt stable may harbor similar decades-old flaws waiting to be found.
This discovery also highlights the value of security research partnerships. Horizon3's responsible disclosure gave Apache maintainers time to prepare patches before exploitation began. Companies that contribute to open-source security research, whether through funding, bounty programs, or direct participation, are investing in their own protection.
System recovery skills become critical when responding to security incidents
Ransomware History: Why ActiveMQ Is a Repeated Target
This isn't the first time ActiveMQ has appeared in CISA's Known Exploited Vulnerabilities catalog. Previous entries include CVE-2016-3088 and CVE-2023-46604. The latter was particularly damaging because the TellYouThePass ransomware gang exploited it as a zero-day before patches were available.
Why do attackers keep targeting ActiveMQ? Several factors make it attractive. It's widely deployed in enterprises handling valuable data. It often runs with elevated privileges because it needs to coordinate between multiple systems. Its complexity means many organizations run outdated versions. And successful compromise gives attackers a pivot point into the most sensitive parts of your infrastructure.
For risk managers, this pattern suggests ActiveMQ should be on your high-priority monitoring list. If your security operations center doesn't have specific detection rules for ActiveMQ exploitation attempts, now is the time to add them.
Strategic Recommendations for Business Leaders
✅ Pros
- • Patches are available and tested since March 30
- • Clear detection guidance from security researchers
- • CISA attention means vendor support will be responsive
- • AI-assisted discovery is finding bugs before mass exploitation
❌ Cons
- • Three-week lag means some systems may already be compromised
- • Legacy integrations complicate rapid patching
- • Attackers have established playbooks for ActiveMQ exploitation
- • Message broker compromise affects multiple downstream systems
The business response to this vulnerability should go beyond just patching. This is an opportunity to audit your message broker infrastructure more broadly. How many critical communication channels run through systems you haven't reviewed in years? What's your visibility into the software supply chain of your enterprise integrations?
For organizations evaluating their messaging infrastructure, this incident may accelerate conversations about managed services versus self-hosted solutions. Cloud-native message brokers from major providers offer automatic patching and dedicated security teams. That's a tradeoff worth modeling against the total cost of ownership for self-managed ActiveMQ deployments.
Logicity's Take
As an agency that builds AI agents and web applications for startups, we see this vulnerability through the lens of early-stage companies that often inherit technical decisions without full context. Many startups use ActiveMQ because it was already running in a platform they forked or a tutorial they followed. They don't have dedicated security teams scanning for CVEs. Our recommendation: if you're a seed or Series A company, this is a wake-up call to audit your infrastructure dependencies. You probably don't need a full message broker. For most startup use cases, simpler solutions like Redis pub/sub or managed services like AWS SQS provide the same functionality with less attack surface and automatic patching. For larger clients we work with, we're building lightweight monitoring dashboards that track CVEs against deployed software inventories. The 13-year detection gap here shows that vulnerability scanning needs to be continuous, not annual. If your security posture relies on periodic penetration tests, you're operating on hope rather than data.
Frequently Asked Questions
How quickly should we patch this ActiveMQ vulnerability?
Immediately. CISA has set April 30 as the federal deadline, but active exploitation means every day of delay increases your risk. If you can't patch within 48 hours, consider taking affected systems offline or implementing network segmentation to limit exposure.
How do we know if we've already been compromised?
Review your ActiveMQ broker logs for connections using the VM transport protocol with brokerConfig=xbean:http:// parameters. These indicate exploitation attempts. Also check for unusual outbound network connections or unexpected processes running on ActiveMQ hosts.
What's the cost of upgrading ActiveMQ in a complex enterprise environment?
Typical enterprise patching projects for message brokers run $50K-$200K when accounting for testing, staging, and production deployment across multiple environments. That's a fraction of the $4.5M+ average breach cost, making immediate patching the clear financial choice.
Should we replace ActiveMQ with a different solution?
This depends on your scale and requirements. For smaller deployments, managed services like AWS SQS or Azure Service Bus reduce operational burden. For complex enterprise needs, evaluate whether commercial support contracts for ActiveMQ or alternatives like RabbitMQ better fit your security posture requirements.
Does this vulnerability affect cloud-hosted ActiveMQ instances?
Yes, if you're running ActiveMQ in cloud VMs or containers, you're responsible for patching. Only fully managed messaging services from cloud providers handle patching automatically. Check with your cloud team to confirm your deployment model.
Explores how emerging tech creates new security and regulatory considerations
The Bottom Line for Enterprise Security Teams
This Apache ActiveMQ vulnerability represents a common pattern in enterprise security: critical infrastructure running software with undetected flaws that become urgent crises when attackers find them first. The 13-year window before discovery is a reminder that code review and traditional security testing have limits.
The silver lining is that patches exist, detection guidance is clear, and the security community is actively tracking exploitation attempts. Organizations that respond quickly will weather this incident. Those that delay risk joining the growing list of companies that learned about their ActiveMQ deployment from a ransomware note.
Need Help Implementing This?
Logicity helps startups and growing companies build secure infrastructure from the start. Whether you need help auditing your software dependencies, implementing monitoring dashboards, or migrating away from legacy systems, our team brings hands-on experience with modern security practices. Get in touch at logicity.in to discuss your infrastructure security needs.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer