ADT Data Breach Exposes 5.5 Million Customers' Personal Info

Key Takeaways

- 5.5 million ADT customers had names, addresses, phone numbers, and partial SSNs exposed
- ShinyHunters gained access through a voice phishing attack on an employee's Okta SSO account
- No payment information or customer security systems were compromised
What Happened
The ShinyHunters extortion group stole personal information from 5.5 million people after breaching home security giant ADT earlier this month. Data breach notification service Have I Been Pwned confirmed the figure after analyzing the stolen data.
ADT detected the breach on April 20, 2026. The company told BleepingComputer that while the intrusion was limited, attackers accessed names, phone numbers, and addresses. A smaller subset of victims also had dates of birth and the last four digits of Social Security numbers or Tax IDs exposed.
ADT emphasized that no payment information was accessed. Bank accounts, credit cards, and customer security systems remained uncompromised.
How ShinyHunters Got In
The extortion group told BleepingComputer they compromised an ADT employee's Okta single sign-on account using voice phishing, also called vishing. The attackers called the employee and tricked them into handing over credentials or authentication codes.
Once inside the SSO account, ShinyHunters accessed ADT's Salesforce instance and extracted customer data. This attack method has become ShinyHunters' signature. The group runs widespread vishing campaigns targeting employees and business process outsourcing agents who use Microsoft Entra, Okta, and Google SSO.
After breaching corporate SSO accounts, they steal data from connected SaaS applications. Their targets include Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, and Dropbox.
The Leaked Data
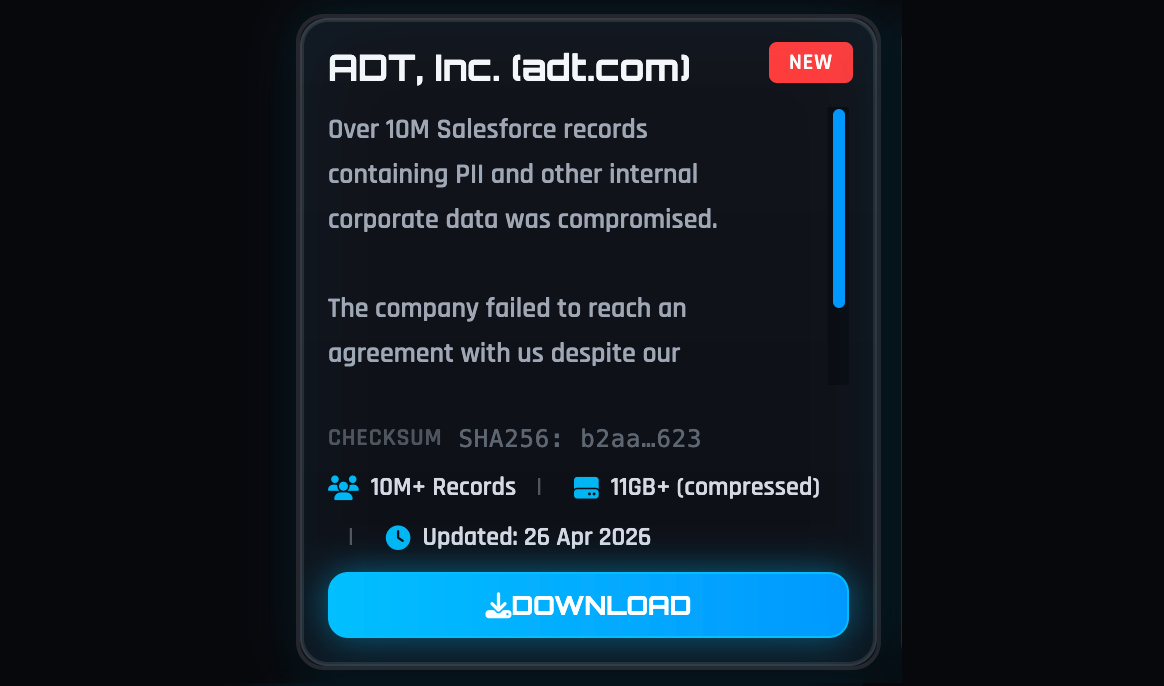
ShinyHunters initially claimed they had stolen over 10 million records containing personally identifiable information and ADT corporate data. When ADT refused to pay, the group leaked an 11GB archive on their dark web site.
Have I Been Pwned's analysis of the leaked data found it contained unique email addresses, names, dates of birth, phone numbers, physical addresses, and partial government-issued IDs for 5.5 million people. ADT has not publicly confirmed this number.
ADT's Breach History
This is ADT's third disclosed data breach in less than a year. The company reported breaches in August 2024 and October 2024 that exposed employee and customer information.
ADT was founded in 1874 as American District Telegraph, making it the oldest home security company in the United States. It's also the largest, providing monitored security and smart home solutions to over 6 million residential and small-business customers.
ShinyHunters' Recent Activity
ADT is not the only major company ShinyHunters has hit recently. Last week, the group also claimed to have stolen more than 9 million records from Medtronic, the world's largest medical device maker by revenue.
ShinyHunters' parallel attack on another major company
The group's vishing campaigns targeting corporate SSO accounts began last year and have proven effective against companies that rely on cloud-based identity management. The pattern is consistent: compromise one employee's SSO credentials, then pivot to connected SaaS applications where customer data lives.
What ADT Customers Should Do
- Watch for phishing attempts using your name, address, or phone number
- Be suspicious of calls claiming to be from ADT or related services
- Monitor credit reports if your partial SSN was exposed
- Consider a credit freeze if concerned about identity theft
ADT has not announced whether it will provide credit monitoring services to affected customers. The company has also not disclosed when or how it will notify the 5.5 million people whose data was exposed.
Logicity's Take
Frequently Asked Questions
Was my ADT account password stolen?
ADT has not reported any credential theft. The stolen data included names, addresses, phone numbers, and in some cases partial SSNs, but not login credentials or passwords.
Is my home security system still secure?
Yes. ADT confirmed that customer security systems were not affected or compromised. The breach was limited to customer personal information stored in corporate systems.
Was my credit card information stolen?
No. ADT stated that no payment information, including bank accounts or credit cards, was accessed in this breach.
How do I know if my data was in this breach?
You can check Have I Been Pwned (haveibeenpwned.com) using your email address. The service analyzed the leaked data and can tell you if your information was included.
What is voice phishing (vishing)?
Vishing is a social engineering attack where criminals call employees and trick them into revealing login credentials or authentication codes. ShinyHunters used this method to compromise an ADT employee's Okta account.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Accenture Deploys Copilot to 743,000 Staff in Record AI Deal
Microsoft's largest enterprise Copilot deal puts the AI assistant on every Accenture employee's desktop. The consulting giant reports staff completing routine tasks up to 15 times faster, though industry-wide AI productivity gains remain disputed.

Nintendo Switch 2 LCD Screen Disappoints: A Portable OLED Fix
The Nintendo Switch 2 shipped with a 1080p LCD panel that looks worse than its predecessor's 720p OLED. Critics cite slow response times and weak contrast. Here's why enthusiasts are pairing the console with portable OLED monitors instead.
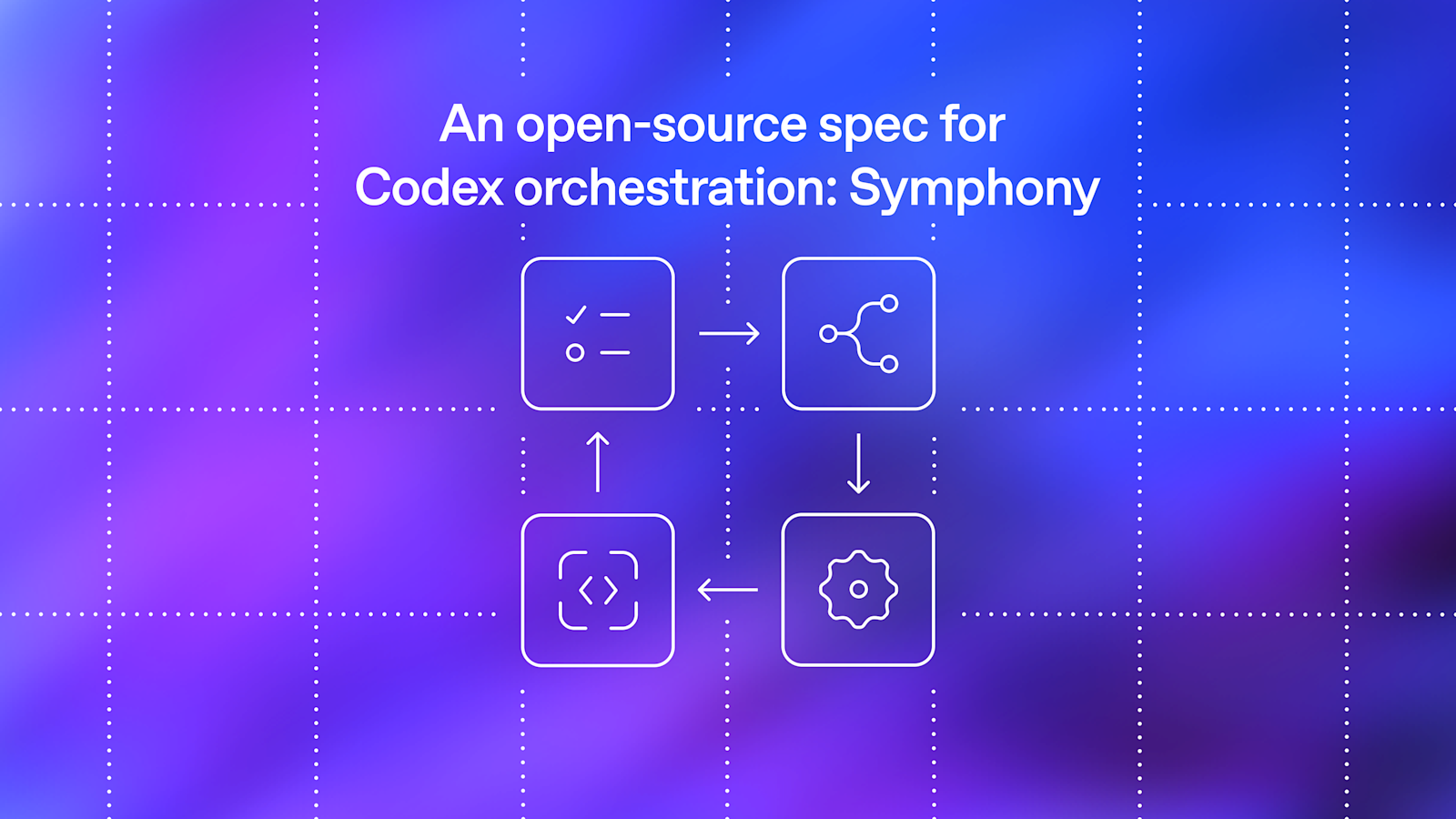
OpenAI Open-Sources Symphony: Agent Orchestration Spec
OpenAI has released Symphony, an open-source specification that turns project management tools like Linear into control planes for coding agents. The system reportedly increased landed pull requests by 500% on some teams by eliminating the context-switching bottleneck that limited engineers to managing three to five agent sessions at once.