Supply Chain Attack Hits 4 Million Developers via npm

Key Takeaways

- A single compromised npm package with 847 million weekly downloads enabled credential theft across multiple package ecosystems
- The attack spread from JavaScript to Rust to Python through transitive dependencies most developers never audit
- The incident was resolved accidentally when a cryptocurrency mining worm overwrote the malicious payload
What Happened
A physical theft in a developer's apartment triggered one of the more absurd security incidents in recent memory. Marcus Chen, maintainer of left-justify (a package with 847 million weekly downloads), had his laptop and hardware 2FA key stolen. When he tried to recover access, a Google AI Overview directed him to a phishing site. He entered his npm credentials. The attackers published a malicious update within two hours.
The compromised package added a postinstall script that stole credentials from .npmrc, .pypirc, ~/.cargo/credentials, and ~/.gem/credentials. Those stolen credentials included the maintainer of vulpine-lz4, a Rust library described as offering "blazingly fast Firefox-themed LZ4 decompression." The library had only 12 GitHub stars but was a transitive dependency of cargo itself.
How the Attack Cascaded
The attackers used the stolen Rust credentials to push vulpine-lz4 version 0.4.1. The commit message read "fix: resolve edge case in streaming decompression." The actual change added a build.rs script that downloaded and executed a shell script on any machine with a hostname containing "build," "ci," "action," "jenkins," "travis," or, inexplicably, "karen."
Security researcher Karen Oyelaran discovered the malicious commit when her personal laptop triggered the payload. She opened an issue titled "your build script downloads and runs a shell script from the internet?" The legitimate maintainer did not respond. He had won €2.3 million in the EuroMillions and was researching goat farming in Portugal.
The Accidental Resolution
According to the incident report, the attack was not resolved through normal security channels. A support ticket titled "why is your SDK exfiltrating my .npmrc" was marked as "low priority - user environment issue" and auto-closed after 14 days of inactivity.
The incident status reads "Resolved (accidentally)" with severity escalating from "Critical" to "Catastrophic" to "Somehow Fine." The total duration was 73 hours. The report indicates an unrelated cryptocurrency mining worm inadvertently patched the malicious code. Approximately 4 million developers were affected before this accidental fix.
Why This Matters
The incident exposes several systemic weaknesses in package management security. A single maintainer's stolen laptop compromised credentials across four different package ecosystems. The malicious code spread through transitive dependencies that most developers never examine. vulpine-lz4 had just 12 GitHub stars, yet it sat in cargo's dependency tree.
The attack also demonstrated how quickly malicious updates can propagate. The attacker published the compromised left-justify version within two hours of obtaining Chen's credentials. From there, the cascade to Rust and Python took less than a day.
- Hardware 2FA loss created an attack window that phishing exploited
- AI-generated search results directed a developer to a malicious site
- Support tickets reporting the issue were auto-closed as low priority
- Critical transitive dependencies had minimal oversight despite wide usage
- The legitimate fix came from malware competing with malware
Lessons for Development Teams
The incident report notes this was the company's 15th such report, suggesting a pattern of recurring security issues. For teams evaluating their own exposure, several points stand out.
First, transitive dependency auditing remains difficult. A library with 12 GitHub stars can still be critical infrastructure if it sits in the right place. Tools like cargo-audit, npm audit, and pip-audit help, but they catch known vulnerabilities. They do not catch a freshly compromised package before anyone reports it.
Second, credential sprawl creates attack surface. The malicious script targeted four different credential stores simultaneously. Developers with access to multiple package registries multiply the blast radius of a single compromise.
Third, incident response processes failed here. The support ticket system treated an explicit report of credential exfiltration as a user environment issue. Automated triage can miss critical signals when reports do not match expected patterns.
Logicity's Take
Frequently Asked Questions
How did the supply chain attack spread across multiple languages?
The initial npm compromise exfiltrated credentials for PyPI, Cargo, and RubyGems. The attackers used stolen Cargo credentials to push malicious code to vulpine-lz4, which was vendored into Python build tools, spreading the attack to Python developers.
Why was a 12-star GitHub library critical to the attack?
vulpine-lz4 was a transitive dependency of cargo itself. Low visibility does not mean low impact. Packages deep in dependency trees can affect millions of builds despite having minimal direct users.
How was the attack actually resolved?
According to the incident report, an unrelated cryptocurrency mining worm inadvertently patched the malicious payload. The security team did not resolve it through normal channels.
What role did AI search results play in the attack?
When Marcus Chen searched for a replacement YubiKey, a Google AI Overview linked him to a phishing site registered just six hours earlier. He entered his npm credentials on that site, enabling the entire attack chain.
How many developers were affected?
The incident report states approximately 4 million developers received malware before the accidental resolution.
Need Help Implementing This?
Source: Hacker News: Best / Andrew Nesbitt
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read

4 Cheap Gadgets That Make Your Kitchen Smarter
You don't need to spend thousands on smart appliances to upgrade your kitchen. A few gadgets under $50 each can add wireless monitoring, precision measurement, automated lighting, and voice control to your existing setup.
Google Antigravity: Build Android Apps Without Code for Free
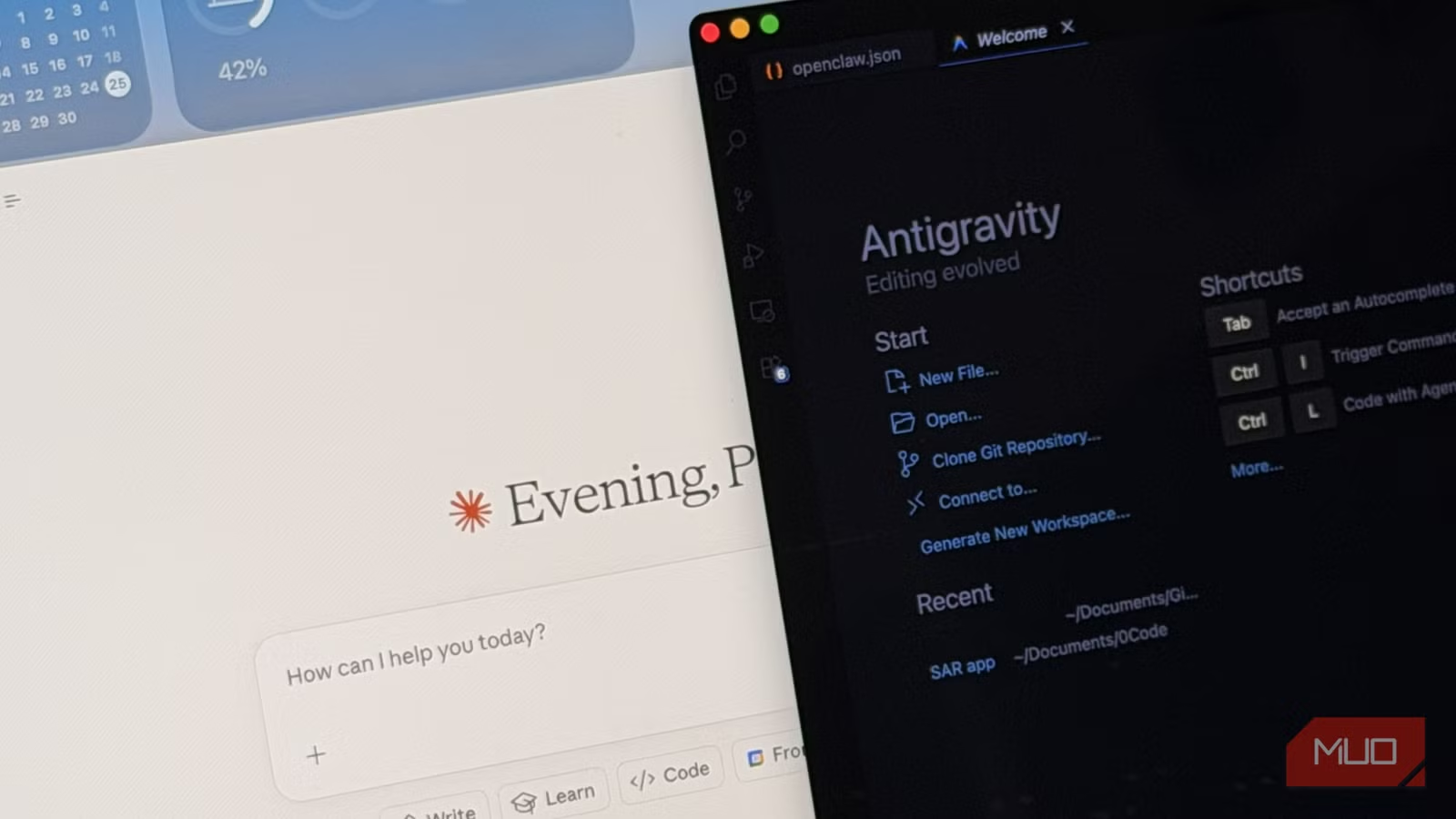
A tech journalist with zero coding experience built a working Android app using Google's free Antigravity IDE. The app has run without bugs for six months, proving that AI-assisted development tools have matured enough for complete beginners to ship functional software.

3 Netflix Thrillers Worth Your Time This Week
Netflix's current thriller selection includes an underrated heist film with an all-star cast, a recent erotic thriller, and a hostage crisis drama. None will crack the top 10, but all three deliver tension worth streaming.