Russian Hackers Targeted 13,500 Signal Users in Phishing Campaign

Key Takeaways

- Russian government hackers targeted over 13,500 Signal users with account-hijacking phishing messages
- The attack impersonates Signal support and tricks users into linking accounts to attacker devices
- CISA, UK cybersecurity agencies, and Dutch intelligence have all attributed similar campaigns to Russian state actors
The Spyware Hunter Becomes the Target
Donncha Ó Cearbhaill has spent years investigating spyware attacks for Amnesty International's Security Lab. Earlier this year, he found himself on the other side.
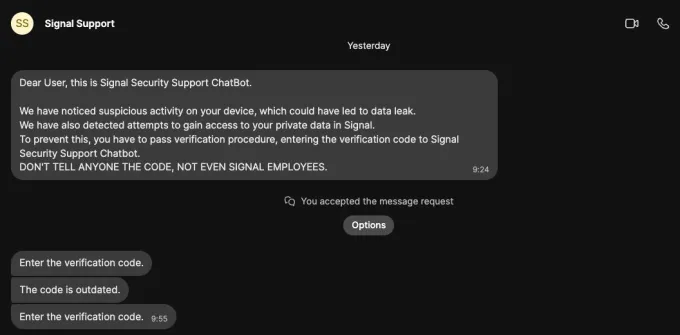
A message arrived on his Signal account claiming to be from "Signal Security Support ChatBot." It warned of suspicious activity and a potential data leak. The message asked him to enter a verification code. Then came the red flag: "DON'T TELL ANYONE THE CODE, NOT EVEN SIGNAL EMPLOYEES."
Ó Cearbhaill immediately recognized the attempt for what it was. But instead of deleting it, he saw an opportunity.
“Having the attack land in my inbox, and the chance to turn the tables on the attackers and understand more about the campaign was too good to pass up.”
— Donncha Ó Cearbhaill, Amnesty International Security Lab
He told TechCrunch he had "never knowingly" been targeted with a one-click cyberattack or phishing attempt before.
A Campaign Spanning 13,500 Targets
Ó Cearbhaill's investigation revealed that the attack on him was part of something much larger. He traced the campaign to over 13,500 targets.
The hackers' playbook was straightforward: impersonate Signal, warn of fake security threats, then trick users into giving access to their accounts. The goal was to link victims' accounts to devices controlled by the attackers.
These techniques match a wider campaign that multiple government agencies have warned about. The U.S. Cybersecurity and Infrastructure Security Agency (CISA), the UK's cybersecurity agency, and Dutch intelligence have all attributed similar attacks to Russian government spies. Signal itself has issued warnings about phishing attacks targeting its users.
The Snowball Effect
Ó Cearbhaill declined to reveal his exact investigation methods. He didn't want to tip off the hackers. But he shared what he learned about the target list.
Among the targets: journalists he had worked with and at least one colleague. This pattern suggested what he called a "snowball hypothesis." The hackers compromise one target, then use that access to identify new potential victims in their contacts.
Ó Cearbhaill believes he became a target because he appeared in the contact lists or conversations of people the hackers had already compromised.
German news magazine Der Spiegel reported that Russian hackers successfully compromised several people inside Germany, including high-profile politicians.
How the Attack Works
Signal's device-linking feature lets users access their account on multiple devices. It's convenient. It's also an attack vector.
The phishing campaign exploits this by posing as Signal support. Victims receive urgent warnings about account security. They're asked to "verify" by entering a code. That code is actually a device-linking authorization. Enter it, and the attacker gains persistent access to your Signal messages.
- The message claims to be from Signal Security Support
- It warns of "suspicious activity" or "data leaks"
- It requests a verification code
- The code actually links the victim's account to an attacker-controlled device
How to Protect Yourself
Signal will never message you through the app asking for verification codes. If you receive such a message, it's a scam.
- Check your linked devices regularly in Signal Settings > Linked Devices
- Remove any devices you don't recognize
- Never share verification codes with anyone, even if they claim to be Signal support
- Enable registration lock in Signal to add a PIN requirement
If you suspect your account has been compromised, unlink all devices and consider re-registering your Signal account.
Logicity's Take
This campaign shows how state-sponsored hackers adapt to encryption. They can't break Signal's cryptography, so they target the human layer. The "snowball" method is clever: each compromised account leads to new targets through contact lists. For anyone handling sensitive communications, regular linked-device audits should be routine.
Frequently Asked Questions
Can Russian hackers read my Signal messages?
Only if you fall for phishing attacks that link your account to their devices. Signal's encryption remains secure. The attack targets human behavior, not the cryptography.
How do I check if my Signal account has been compromised?
Go to Signal Settings > Linked Devices. If you see any devices you don't recognize, remove them immediately.
Will Signal warn me about security threats through the app?
No. Signal does not send security alerts or verification requests through in-app messages. Any such message is a phishing attempt.
Why are Russian hackers targeting Signal users?
Signal is popular among journalists, activists, and officials who communicate sensitive information. Compromising these accounts can yield valuable intelligence.
Another recent campaign showing how attackers exploit trusted communication platforms
Need Help Implementing This?
If your organization needs to secure communications against state-sponsored threats, or you want help auditing your team's messaging security practices, reach out to the Logicity team. We can connect you with experts who specialize in operational security for high-risk environments.
Source: TechCrunch / Lorenzo Franceschi-Bicchierai
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read
Composio vs Zapier: Which AI Agent Platform Wins?
Zapier and Composio both solve the critical problem of keeping API credentials away from AI agents. But they serve different audiences. Zapier offers 9,000+ app integrations with no-code tools, while Composio targets developers building custom AI products.
Why Your Smart Home Gadgets Are Killing Your Wi-Fi Speed
That 100-device smart home might be the reason you never hit the speeds your ISP promised. The 2.4GHz band your smart lights and thermostats depend on is likely congested, dragging down performance for phones, laptops, and streaming devices that share the same frequency.
4 Things That Will Frustrate You When Switching to Linux
Linux offers freedom from ads, better privacy, and more control over your system. But if you're coming from Windows, a few friction points can derail your switch before you settle in. Here's what to expect and how to prepare.