Palo Alto Firewalls Hit by Zero-Day Exploit in the Wild

Key Takeaways

- CVE-2026-0300 allows unauthenticated attackers to run code with root privileges on exposed Palo Alto firewalls
- Over 5,800 vulnerable VM-series firewalls are currently internet-facing, mostly in Asia and North America
- No patch is available yet. Palo Alto recommends restricting User-ID Authentication Portal access or disabling it entirely
Palo Alto Networks disclosed a critical zero-day vulnerability in its firewall software on Wednesday, warning customers that attackers are already exploiting it in the wild. The flaw, tracked as CVE-2026-0300, affects the User-ID Authentication Portal in PAN-OS and allows unauthenticated remote code execution with root privileges.
No patch is available. The company is still working on a fix and has labeled the vulnerability as maximum severity.
What the Vulnerability Does
The User-ID Authentication Portal, also called the Captive Portal, handles authentication for users whose identities the firewall cannot automatically map. CVE-2026-0300 stems from a buffer overflow weakness in this component.
An attacker can send specially crafted packets to an internet-exposed PA-Series or VM-Series firewall and execute arbitrary code with root privileges. No authentication is required. No user interaction is needed.
“Limited exploitation has been observed targeting Palo Alto Networks User-ID Authentication Portals that are exposed to untrusted IP addresses and/or the public internet.”
— Palo Alto Networks security advisory
The company noted that organizations following standard security practices, such as restricting sensitive portals to trusted internal networks, face significantly lower risk.
Over 5,800 Firewalls Exposed Online
Internet threat monitoring service Shadowserver is currently tracking more than 5,800 PAN-OS VM-series firewalls exposed to the public internet. Asia leads the exposure count with 2,466 devices, followed by North America with 1,998.
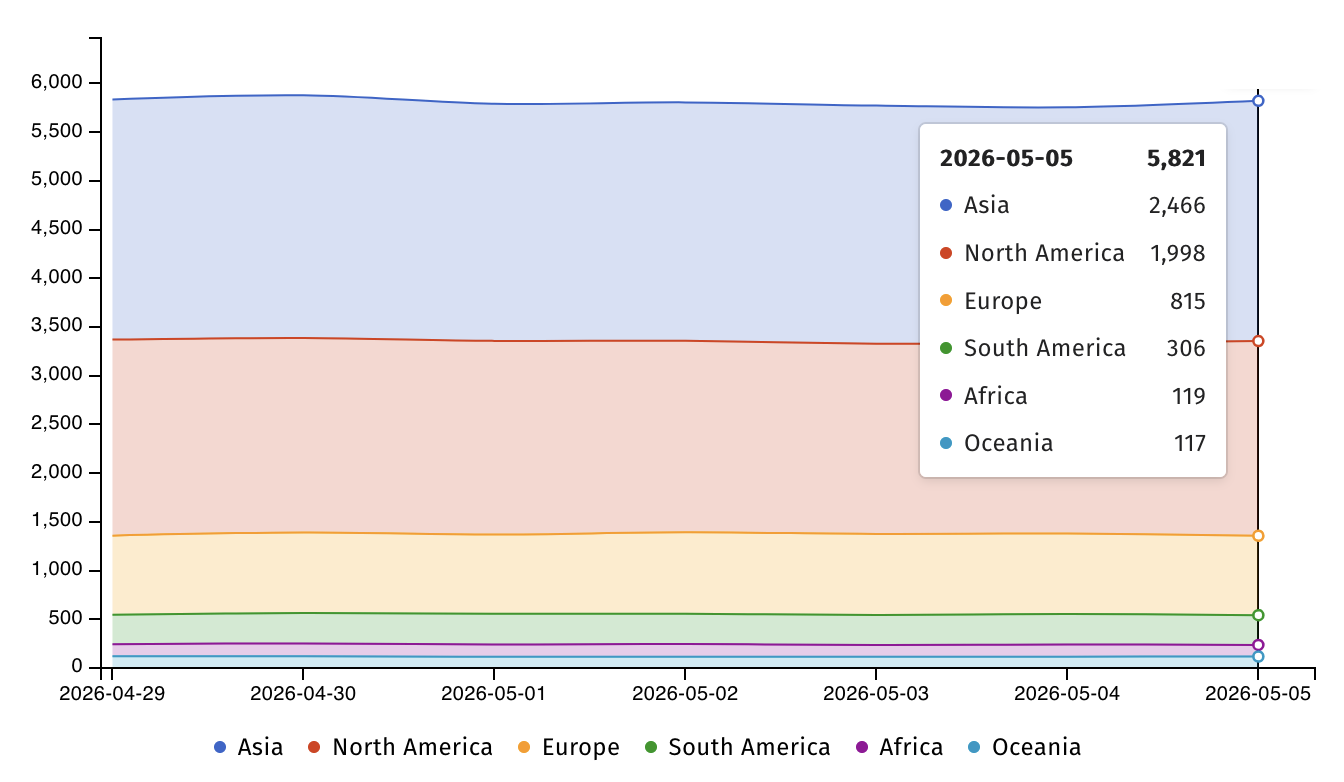
Each of these devices represents a potential entry point for attackers exploiting CVE-2026-0300. Organizations running internet-facing Palo Alto firewalls should check their configurations immediately.
How to Check If You're Affected
Palo Alto Networks has provided instructions for administrators to verify their exposure. To check if your firewall uses the vulnerable service:
- Navigate to Device > User Identification > Authentication Portal Settings
- Look for the "Enable Authentication Portal" option
- If enabled and exposed to the internet, your device is at risk
Mitigations Until a Patch Arrives
With no patch available, Palo Alto Networks "strongly" recommends two mitigation approaches:
- Restrict User-ID Authentication Portal access to trusted zones only
- Disable the portal entirely if restricting access is not feasible
Neither option is ideal for organizations that rely on the Captive Portal for user authentication. But leaving the portal exposed while attackers have a working exploit is worse.
A Pattern of PAN-OS Zero-Days
This disclosure continues a troubling pattern for Palo Alto Networks. PAN-OS firewalls have been targeted repeatedly over the past 18 months:
The scale of Palo Alto's customer base makes these vulnerabilities particularly concerning. The company says its products are used by more than 70,000 customers worldwide, including 90% of Fortune 10 companies and most major U.S. banks.
Logicity's Take
What Security Teams Should Do Now
The immediate priority is clear: audit your Palo Alto firewall configurations today. Check which devices have the User-ID Authentication Portal enabled. Verify whether those devices are reachable from untrusted networks.
If you cannot restrict or disable the portal, monitor for signs of compromise. Look for unexpected administrative actions, unusual outbound connections, or changes to firewall rules. Document your exposure for your incident response plan.
When Palo Alto releases a patch, apply it immediately. Given the confirmed exploitation, this is not a "wait and see" situation.
Frequently Asked Questions
What is CVE-2026-0300?
CVE-2026-0300 is a critical buffer overflow vulnerability in the PAN-OS User-ID Authentication Portal. It allows unauthenticated attackers to execute code with root privileges on affected Palo Alto firewalls.
Which Palo Alto firewall models are affected?
PA-Series and VM-Series firewalls running PAN-OS with the User-ID Authentication Portal enabled are vulnerable if exposed to untrusted networks.
Is there a patch available for CVE-2026-0300?
No. Palo Alto Networks is still developing a patch. In the meantime, the company recommends restricting portal access to trusted zones or disabling it entirely.
How do I check if my firewall is vulnerable?
Go to Device > User Identification > Authentication Portal Settings in your firewall's management interface. If "Enable Authentication Portal" is active and the device is internet-facing, it's at risk.
Are attackers actively exploiting this vulnerability?
Yes. Palo Alto Networks confirmed limited exploitation is already occurring against portals exposed to the public internet.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Why DVD Recorders Failed Despite Being Better Than VHS
DVD recorders offered superior quality, instant chapter access, and no tape degradation. Yet they never replaced VHS recorders in most homes. The reasons reveal a classic pattern of technology adoption failure that still applies today.

Sony Xperia 1 VIII Leaks at €1,869 via Amazon Listing
An accidental Amazon listing in Germany and the UK has revealed the Sony Xperia 1 VIII's pricing, specs, and June 26 release date. The flagship phone appears to cost €1,868.99 in Germany and £1,728 in the UK, though the price includes bundled Sony WH1000XM6 headphones.
7 Windows Apps That PowerToys Now Replaces
Microsoft's PowerToys has quietly absorbed the functionality of several popular third-party Windows utilities. From monitor brightness controls to quick launchers, the free tool bundle now handles tasks that once required separate downloads.