NVIDIA Confirms GeForce NOW Breach Hit Armenian Users
Key Takeaways
- NVIDIA's core network was not compromised. The breach affected only systems run by GFN.am, the Armenian regional partner.
- Exposed data includes full names, email addresses, phone numbers, dates of birth, and usernames. No passwords were leaked.
- A threat actor using the ShinyHunters nickname offered the stolen database for $100,000 in Bitcoin or Monero.
What Happened
NVIDIA has confirmed that user data from its GeForce NOW cloud gaming service was exposed in a breach. The company told BleepingComputer that the incident was limited to Armenia and caused by a compromise at GFN.am, a regional partner that operates the service there.
"Our investigation found no impact on NVIDIA-operated services. The issue is limited to systems run by a third-party GeForce NOW Alliance partner based in Armenia," NVIDIA said in its statement. "We are working closely with the partner to support their investigation and resolution. Impacted users will be notified by GFN.am."
The breach occurred between March 20 and 26, according to GFN.am. Users who registered after March 9 are not affected.
What Data Was Exposed
GFN.am confirmed that the following information was compromised:
- Full name (for users with linked Google accounts)
- Email address
- Phone number (for users who registered via mobile operator)
- Date of birth
- Username
No account passwords were exposed in the incident. However, the threat actor's original post claimed the stolen data also included membership status and 2FA/TOTP status, which could reveal which accounts have weaker security configurations.
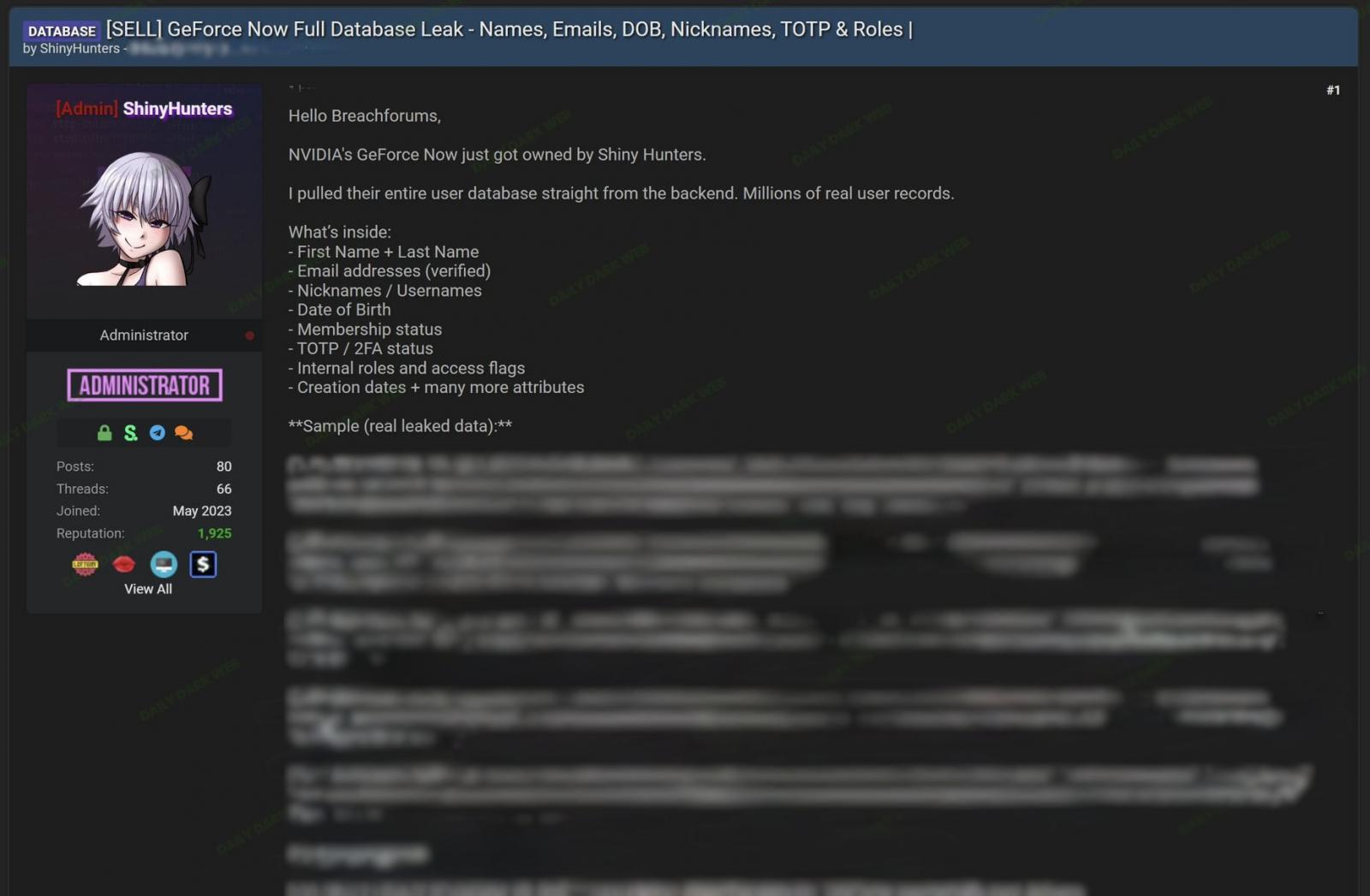
The Threat Actor's Claims
Last week, a threat actor using the nickname ShinyHunters posted on a hacker forum claiming to have breached GeForce NOW and stolen millions of user records. The actor offered the full database for $100,000, payable in Bitcoin or Monero, and posted samples of the stolen data as proof.
BleepingComputer found that the threat actor's post has since been removed from the forum. It's unclear whether the database was sold or if the post was deleted by the seller or forum administrators.
How the Alliance Partner Model Works
NVIDIA uses a "GeForce NOW Alliance" model to reduce latency in specific regions. Regional partners like GFN.am operate independent infrastructure, including their own authentication systems, customer databases, and billing platforms. This means their data is separate from NVIDIA's global network.
GFN.am manages GeForce NOW operations not just in Armenia but also in Azerbaijan, Georgia, Kazakhstan, Moldova, Ukraine, and Uzbekistan. NVIDIA has not confirmed any impact on users in those countries.
The Security Trade-Off
The Alliance model lets NVIDIA expand into regions where building its own data centers would be impractical. But it creates a security trade-off. Each partner runs different infrastructure with different security practices. A breach at one partner doesn't compromise NVIDIA's core, but it still affects users under NVIDIA's brand.
This incident highlights a common challenge for companies that rely on third-party partners for regional operations. The weakest link in the chain can still damage the brand and expose customer data, even if the main company's systems remain secure.
What Affected Users Should Do
If you used GeForce NOW through GFN.am before March 9, watch for phishing attempts. Attackers now have your name, email, and potentially your phone number. They could craft convincing messages pretending to be from NVIDIA or GFN.am.
- Be suspicious of emails or texts asking you to "verify" your account or reset your password
- Enable 2FA on any accounts that share the same email address
- Monitor your email for unusual login attempts or password reset requests
Logicity's Take
Frequently Asked Questions
Was NVIDIA's main network breached?
No. NVIDIA confirmed its own systems were not affected. The breach was limited to infrastructure operated by GFN.am, a third-party regional partner in Armenia.
What information was stolen in the GeForce NOW breach?
The exposed data includes full names, email addresses, phone numbers, dates of birth, and usernames. Account passwords were not compromised.
How much did the hacker want for the stolen data?
The threat actor, using the ShinyHunters nickname, asked for $100,000 payable in Bitcoin or Monero.
Are GeForce NOW users outside Armenia affected?
GFN.am also manages services in Azerbaijan, Georgia, Kazakhstan, Moldova, Ukraine, and Uzbekistan, but NVIDIA has not confirmed any impact on users in those countries.
When did the breach occur?
The cybersecurity incident took place between March 20 and 26. Users who registered after March 9 are not affected.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Pentagon Releases 161 Declassified UFO Files With 30 Videos
The Pentagon published its first batch of declassified UAP files on May 8, responding to President Trump's February directive. The release includes 161 files with nearly 30 videos showing unidentified objects captured by military sensors, plus eyewitness accounts from Apollo astronauts.
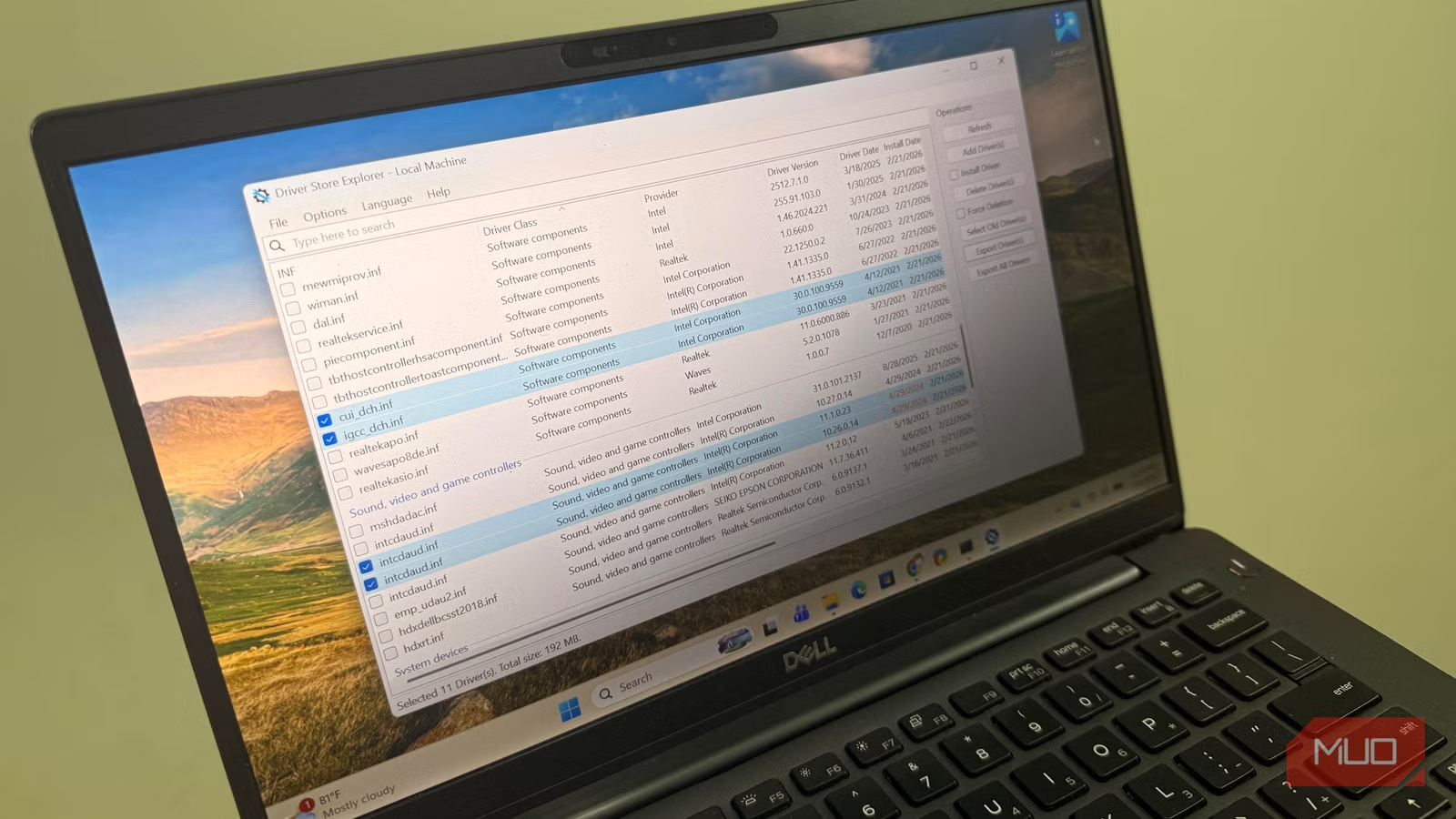
How to Clear Old Windows Drivers Wasting Your SSD Space
Windows stores every driver you've ever installed but never cleans up old versions. This hidden folder can grow to 30GB on gaming PCs. Here's how to safely reclaim that space.

Diablo 4 Gold Bug Gives Players 900% Boost
A Horadric seal item in Diablo 4: Lord of Hatred is giving players a 900% gold bonus. This appears to be a decimal point error. Players are exploiting it to earn billions of gold per hour before Blizzard patches it.