Canvas LMS Breach: ShinyHunters Stole 3.6TB from 8,800 Schools

Key Takeaways

- ShinyHunters exploited XSS vulnerabilities in Canvas to steal 3.6 terabytes of data from 8,809 educational institutions
- The same vulnerability was used twice: first for data theft, then to deface login portals with ransom demands
- Stolen data likely includes usernames, emails, course names, enrollment info, and messages from schools and universities
Instructure, the company behind Canvas LMS, has confirmed that hackers exploited security flaws to breach its network, steal over 3.6 terabytes of data, and then deface login portals at schools across the country. The attacker, known as ShinyHunters, used the same cross-site scripting vulnerabilities in both attacks.
Canvas is one of the most widely used learning management systems in education. Schools and universities rely on it for assignments, coursework, grading, and student communication. According to ShinyHunters, this breach affects 8,809 educational organizations, including schools, universities, colleges, and online platforms.
How the Attack Unfolded
Instructure discovered the initial breach on April 29. The company says it "immediately revoked the unauthorized party's access, started an investigation, and engaged outside forensic experts." A few days later, Instructure confirmed that data had been stolen.
ShinyHunters then published Instructure on their data leak site, claiming they had exfiltrated more than 3.6 terabytes of uncompressed data. The stolen information likely includes usernames, email addresses, course names, enrollment information, and messages exchanged within the platform.
The Second Attack: Portal Defacement
On May 7, ShinyHunters struck again. This time, they used the same XSS vulnerability to deface Canvas login portals with an extortion message. The goal was clear: pressure Instructure into paying a ransom by making the breach visible to students and educators.
BleepingComputer reports that ShinyHunters injected malicious JavaScript through XSS bugs in user-generated content features. This gave them access to authenticated admin sessions, allowing them to perform privileged actions on the platform.
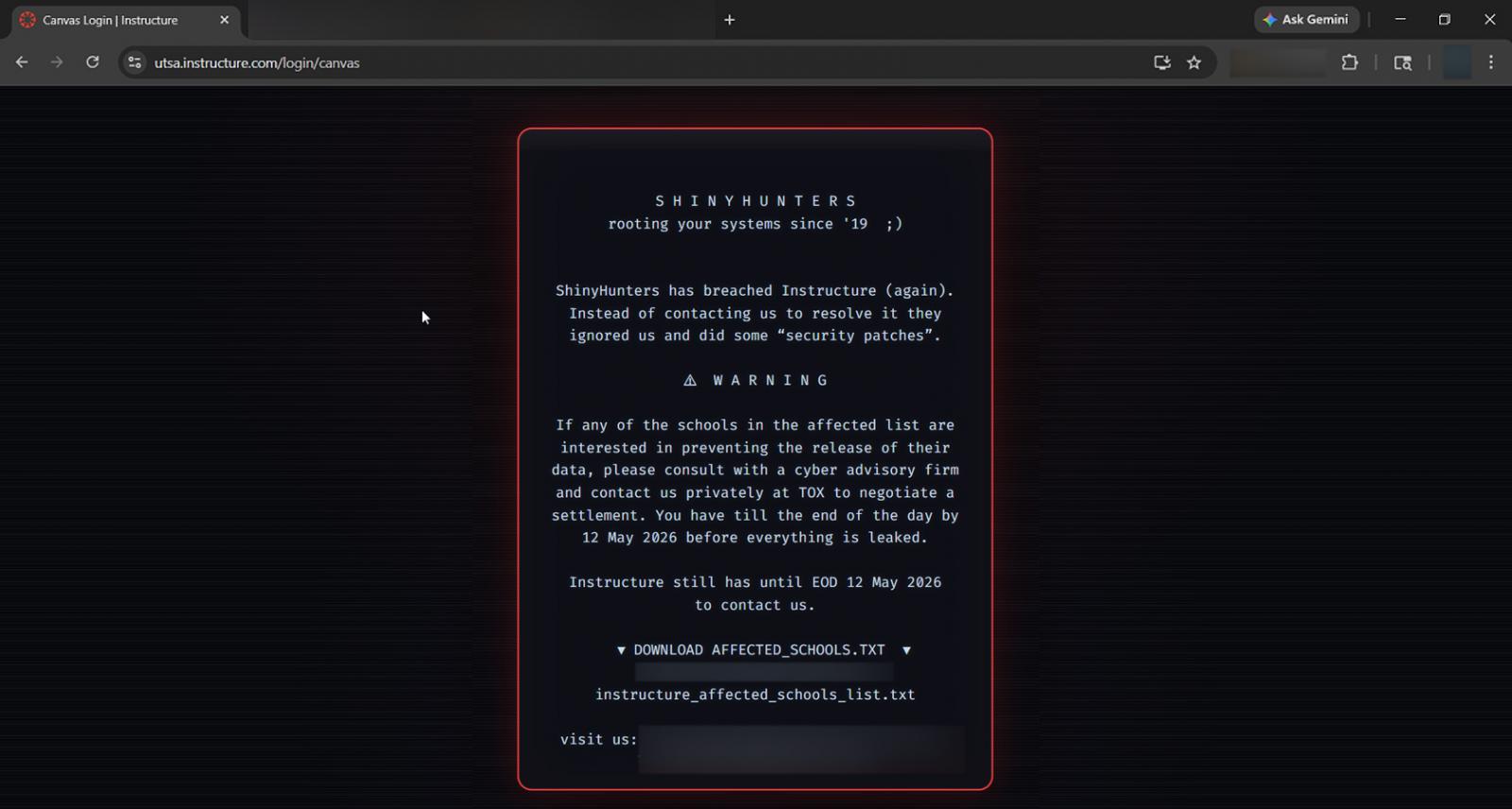
The message warned that Instructure and affected schools had until May 12 to reach out and negotiate. Screenshots show the defacement appeared on the University of Texas San Antonio's Canvas login page, among others.
“The unauthorized actor made changes to the pages that appeared when some students and teachers were logged in through Canvas.”
— Instructure spokesperson
The Vulnerability: Free-for-Teacher Edition
In an email to BleepingComputer, Instructure confirmed that the exploited security issue affected the Free-for-Teacher environment. This is a limited, free version of Canvas LMS designed for individual educators.
Cross-site scripting vulnerabilities allow attackers to inject malicious code into web pages viewed by other users. When successful, attackers can hijack user sessions, steal credentials, or perform actions as if they were the logged-in user. In this case, ShinyHunters gained access to admin sessions, giving them control over portal content.
Instructure has shut down Free-for-Teacher accounts until the issues are resolved. The main Canvas platform was restored and available for use as of May 9. The company says no additional data was compromised during the portal defacement, though the damage from the initial breach remains.
Who Is ShinyHunters?
ShinyHunters is a prolific hacking group that has targeted companies across sectors. They typically steal data and sell it on dark web forums or use it as leverage for ransom demands. Past victims include Microsoft, AT&T Wireless, and Tokopedia. The group operates opportunistically, hunting for vulnerabilities in web applications and APIs.
Educational platforms make attractive targets. They hold large amounts of personal data, from student emails to enrollment records, and often have limited security budgets compared to financial or healthcare organizations.
Understanding why credential-based defenses fail against session hijacking
What This Means for Affected Schools
If ShinyHunters' claims are accurate, nearly 9,000 educational institutions now have student and faculty data in the hands of criminals. The stolen information, including usernames, emails, course names, enrollment data, and messages, could be used for phishing attacks, identity theft, or further breaches.
Schools using Canvas should alert their communities about the breach. Students and staff should watch for phishing emails that reference course names or enrollment details. These personalized details make social engineering attacks more convincing.
- Monitor email for phishing attempts that reference Canvas courses or enrollment
- Change passwords for Canvas and any accounts using the same credentials
- Enable multi-factor authentication where available
- Be suspicious of messages referencing specific course names or assignment details
How threat actors are accelerating vulnerability exploitation
Logicity's Take
Instructure's Response
Instructure took Canvas offline temporarily after the May 7 defacement to prevent the malicious activity from spreading, determine the root cause, and apply additional safeguards. The platform was back online by May 9.
The company has not publicly stated whether it will pay the ransom. Most security experts recommend against paying, as it encourages further attacks and provides no guarantee that stolen data will be deleted or unused. However, the pressure of a public deadline and visible defacement puts Instructure in a difficult position.
Frequently Asked Questions
What data was stolen in the Canvas LMS breach?
ShinyHunters claims to have stolen 3.6 terabytes of data, likely including usernames, email addresses, course names, enrollment information, and messages from 8,809 educational organizations.
Is Canvas LMS safe to use now?
Instructure says Canvas was restored on May 9 and is available for use. The Free-for-Teacher accounts remain shut down until security issues are resolved.
How did hackers breach Canvas?
ShinyHunters exploited cross-site scripting (XSS) vulnerabilities in user-generated content features of the Free-for-Teacher environment to hijack authenticated admin sessions.
What should students do after this breach?
Change your Canvas password and any accounts using the same credentials. Watch for phishing emails that reference your courses or enrollment details. Enable multi-factor authentication where possible.
Did schools lose money in this breach?
The breach involved data theft, not financial fraud. However, affected schools may face costs for breach notification, credit monitoring for affected users, and potential regulatory penalties.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

Windows 11 Low Latency Mode Opens Apps 70% Faster
Microsoft is testing a new Low Latency Profile in Windows 11 that temporarily boosts CPU speed for interactive tasks. Early results show the Start menu opening 70% faster and apps like Edge launching 40% quicker. A Microsoft VP defended the feature against critics who called it a 'bandage' fix.

5 Android Auto Features You Can Use (But Probably Shouldn't)
Android Auto now supports video conferencing apps, arcade games, and AI assistants on your car's dashboard. While Google built in safety locks for most of these features, the mental distraction risk remains real. Here's what each feature actually does and when it crosses from useful to dangerous.
Claude vs ChatGPT in 2026: Which AI Wins for Your Work?
After countless model updates, Claude and ChatGPT have reached essential parity in raw intelligence. The real question now is which tool fits your specific workflow. We break down the 2026 state of this rivalry across creative work, coding, agentic features, and enterprise adoption.