ADT Confirms Data Breach After ShinyHunters Ransom Threat

Key Takeaways

- ADT detected unauthorized access on April 20 and confirmed theft of customer names, phone numbers, addresses, and some partial Social Security numbers
- ShinyHunters claims to have stolen 10 million records and set an April 27 deadline for ransom payment
- The attackers allegedly used voice phishing to compromise an employee's Okta SSO account, then accessed data through Salesforce
ADT, one of the largest home security companies in the United States, has confirmed a data breach after the ShinyHunters extortion group publicly threatened to leak stolen customer data unless a ransom is paid.
The company said it detected unauthorized access to customer and prospective customer data on April 20, 2026. ADT terminated the intrusion and launched an investigation that confirmed personal information was stolen.
"The investigation confirmed that the information involved was limited to names, phone numbers, and addresses," ADT told BleepingComputer. "In a small percentage of cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were included."
The company emphasized that no payment information, including bank accounts or credit cards, was accessed. Customer security systems were not affected or compromised, according to ADT's statement.
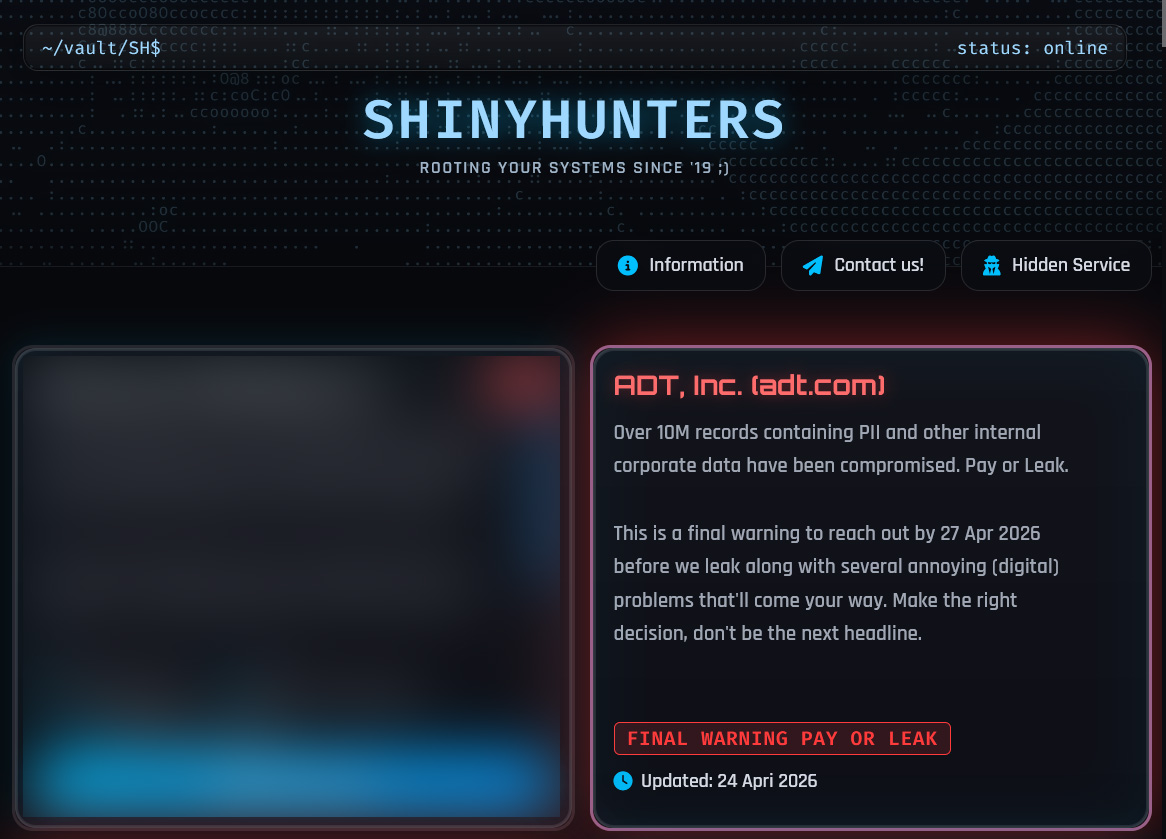
ShinyHunters Claims 10 Million Records Stolen
ADT's confirmation follows a listing on the ShinyHunters data leak site. The attackers claim to have stolen over 10 million records containing customer personal information and internal corporate data.
“Over 10M records containing PII and other internal corporate data have been compromised. Pay or Leak. This is a final warning to reach out by 27 Apr 2026 before we leak along with several annoying (digital) problems that'll come your way.”
— ShinyHunters data leak site listing
ADT did not confirm the volume of data theft claimed by the attackers. The gap between ShinyHunters' 10 million figure and ADT's description of "limited" exposure remains unexplained.
Voice Phishing Used to Compromise Okta Account
ShinyHunters told BleepingComputer they allegedly breached ADT through a voice phishing (vishing) attack. The attack compromised an employee's Okta single sign-on (SSO) account.
Using this account, the threat actors claimed they accessed and stole data from the company's Salesforce instance. This attack method fits a pattern ShinyHunters has used since last year.
The extortion group has been conducting widespread vishing campaigns targeting employees and BPO agents' Microsoft Entra, Okta, and Google SSO accounts. After gaining access to a corporate SSO account, the threat actors steal data from connected SaaS applications.
- Salesforce
- Microsoft 365
- Google Workspace
- SAP
- Slack
- Adobe
- Atlassian
- Zendesk
- Dropbox
The stolen data is then used to extort the company into paying a ransom. If the company refuses, ShinyHunters publishes the data.
ADT's Third Data Breach in Two Years
This is not ADT's first security incident. The company previously disclosed data breaches in August and October 2024 that exposed customer and employee information.
The pattern raises questions about ADT's security posture. A home security company that repeatedly suffers breaches faces an obvious credibility problem. Customers trust ADT to protect their homes. Three breaches in under two years suggests the company has struggled to protect its own systems.
ADT says it has contacted all affected individuals. The company has not disclosed whether it will pay the ransom or what additional security measures it plans to implement.
Logicity's Take
Another example of sophisticated attack techniques bypassing traditional security controls
What Affected Customers Should Do
If you're an ADT customer, assume your name, phone number, and address may have been exposed. In some cases, partial Social Security numbers were also taken.
- Monitor your credit reports for unusual activity
- Be skeptical of phone calls claiming to be from ADT or other companies, as attackers may use stolen data for social engineering
- Consider placing a fraud alert or credit freeze if your partial SSN was exposed
- Watch for phishing emails that reference your ADT account or home address
ADT says it will contact affected individuals directly. If you receive such notification, verify it through ADT's official website rather than clicking links in emails.
Frequently Asked Questions
What data was stolen in the ADT breach?
ADT confirmed that names, phone numbers, and addresses were stolen. In some cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were also exposed. No payment information or security system data was accessed.
Who is ShinyHunters?
ShinyHunters is a data extortion group that has been operating widespread voice phishing campaigns since 2024. They target employee SSO accounts at Okta, Microsoft Entra, and Google to steal data from connected SaaS applications, then demand ransom to prevent publication.
Were ADT home security systems compromised?
No. ADT states that customer security systems were not affected or compromised. The breach targeted customer personal information, not the security hardware or monitoring services.
How did the attackers breach ADT?
ShinyHunters claims they used a voice phishing (vishing) attack to compromise an employee's Okta SSO account, then used that access to steal data from ADT's Salesforce instance.
Has ADT been breached before?
Yes. ADT disclosed data breaches in both August and October 2024 that exposed customer and employee information. This is the company's third known breach in under two years.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Kraken Crypto Exchange Extortion: Hackers Threaten to Leak Internal Videos After Insider Breach
Cryptocurrency exchange Kraken is being extorted by hackers who obtained videos of internal systems through bribed support employees. The company says no funds were compromised and refuses to pay, with only about 2,000 accounts affected. Kraken is working with federal law enforcement to prosecute everyone involved.

Windows 11 KB5083769 and KB5082052: April 2026 Patch Tuesday Brings Smart App Control Changes and Security Fixes
Microsoft's April 2026 Patch Tuesday updates are now live for Windows 11, bringing critical security patches alongside a welcome change to Smart App Control. You can finally toggle SAC on or off without wiping your entire system. The updates cover versions 23H2, 24H2, and 25H2.

Zero Trust Identity Security: 5 Ways This Framework Actually Stops Credential Theft
Stolen credentials caused 22% of breaches in 2025, making them the top attack vector. Zero Trust promises to fix this, but only when it's built around identity as the core principle. Here's how organizations can implement it properly.
Open Source PR Backlogs: Why Your GitHub Contribution Sits Unreviewed for a Year
A developer's Jellyfin pull request has been waiting over a year for merge despite two approvals, exposing a systemic crisis in open source maintenance. Queuing theory explains why backlogs grow exponentially, and 60% of maintainers have quit or considered quitting due to burnout.
Also Read

10 YouTube Music Features That Improve Your Listening
YouTube Music lacks some polish compared to Spotify and Apple Music, but it has unique strengths. These tips help you transfer playlists, upload personal tracks, fine-tune audio quality, and control how the algorithm learns your taste.

iPhone 18 Reportedly Getting 12GB RAM and 2nm Chip
Apple's iPhone 18 may ship with 12GB of RAM, a 50% jump from the current 8GB standard. The device will also use TSMC's 2nm A20 chipset, which promises 15% better performance with no efficiency loss.

Firestarter Malware Survives Cisco Firewall Patches and Reboots
CISA and the UK's NCSC warn that Firestarter, a custom backdoor attributed to the UAT-4356 threat group, persists on Cisco firewall devices even after firmware updates and security patches. Admins must perform full cold boots or device re-imaging to clear the infection.