BitLocker Zero-Day Lets Attackers Bypass Encryption via USB

Key Takeaways

- Two zero-day vulnerabilities in BitLocker allow attackers with physical access to bypass encryption on Windows 11
- The exploit code is publicly available on GitHub, making immediate mitigation essential
- Enable a BitLocker PIN, strong password, and BIOS/UEFI admin password until Microsoft patches
What the Exploit Does
A cybersecurity researcher using the handle Chaotic Eclipse (also known as Nightmare Eclipse) has publicly released exploit code targeting two previously unknown BitLocker vulnerabilities. The flaws, nicknamed 'YellowKey' and 'GreenPlasma,' work together to give attackers unrestricted filesystem access on encrypted Windows 11 machines.
The attack requires physical access to the target computer and a USB drive. Once executed, YellowKey bypasses BitLocker's recovery protections, while GreenPlasma escalates privileges to allow direct manipulation of system services and drivers. The result: complete access to every file on the encrypted drive.
The exploit affects Windows 11 and Windows Server 2022 and 2025 editions. Windows 10 systems appear unaffected.

Why the Researcher Went Public
Security researchers typically report vulnerabilities to vendors privately and wait for patches before disclosure. Chaotic Eclipse took a different path. The researcher appears to have a grievance with Microsoft's handling of previous bug reports, stopping just short of accusing the company of intentionally building a backdoor.
“I can't wait when I will be allowed to disclose the full story. I think people will find my crashout very reasonable and it definitely won't be a good look for Microsoft.”
— Chaotic Eclipse, security researcher
The exploit code is currently available on GitHub, which means anyone with basic technical skills can download and compile it. This raises the urgency for Windows 11 users to implement mitigations immediately rather than waiting for Microsoft's patch.
Independent cybersecurity researchers Kevin Beaumont and Will Dormann confirmed the findings on Mastodon, lending credibility to the disclosure.
How the Attack Works
The attack chain exploits Windows Recovery Environment (WinRE) to bypass BitLocker's normal protections. An attacker with physical access copies files to a USB flash drive, then uses WinRE to sidestep the recovery process and open a system command prompt with elevated privileges.
This isn't the first time BitLocker has faced scrutiny. Previous vulnerabilities have demonstrated that full-disk encryption can be bypassed under specific conditions. But the combination of public exploit code and the severity of access gained makes this disclosure particularly concerning for organizations relying on BitLocker to protect sensitive data on laptops and workstations.

What You Should Do Now
Until Microsoft releases a patch, the researcher and security experts recommend several mitigations:
- Enable a BitLocker PIN: This adds pre-boot authentication that the exploit cannot bypass.
- Set a strong BitLocker password: Avoid simple numeric PINs in high-security environments.
- Store recovery keys offline: Keep them on paper or in a secure location disconnected from the network.
- Set a BIOS/UEFI administrator password: This prevents attackers from modifying boot settings to facilitate the exploit.
- Limit physical access: The attack requires hands-on access to the machine. Data center and office security matter.
For organizations with large Windows 11 deployments, the BitLocker PIN requirement can be enforced through Group Policy. This should be a priority for any IT team managing laptops used by traveling employees or executives.
Logicity's Take
The Bigger Picture
BitLocker is the default encryption solution for Windows Pro and Enterprise editions. Many organizations treat it as adequate protection for data at rest. This vulnerability is a reminder that encryption is only as strong as its implementation.
Physical access attacks have always been the hardest to defend against. But an exploit that requires only a USB drive and public instructions significantly lowers the barrier. Corporate security teams should reassess their assumptions about laptop protection, especially for devices that leave the office.
Frequently Asked Questions
Does this vulnerability affect Windows 10?
No. According to the researcher, the exploit only works on Windows 11 and Windows Server 2022/2025 editions.
Can the attack be executed remotely?
No. The attacker needs physical access to the target computer and a USB drive to execute the exploit.
Has Microsoft released a patch?
Not yet. Until a patch is available, users should enable a BitLocker PIN and BIOS/UEFI password as mitigations.
What is the best immediate protection against this exploit?
Enable a BitLocker PIN for pre-boot authentication. This adds a layer the current exploit cannot bypass.
Need Help Implementing This?
Source: MakeUseOf
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
How to Jailbreak Your Kindle: Escape Amazon's Control Before They Brick Your E-Reader
Amazon is cutting off support for older Kindles starting May 2026, but you don't have to buy a new device. Jailbreaking your Kindle lets you install custom software like KOReader, read ePub files natively, and keep your e-reader alive for years to come.

X-Sense Smoke and CO Detectors at Home Depot: UL-Certified Alarms You Can Actually Trust
X-Sense just made their UL-certified smoke and carbon monoxide detectors available at Home Depot stores nationwide. The lineup includes wireless interconnected models that can link up to 24 units, 10-year sealed batteries, and smart features designed to cut down on those annoying false alarms that make people disable their detectors entirely.
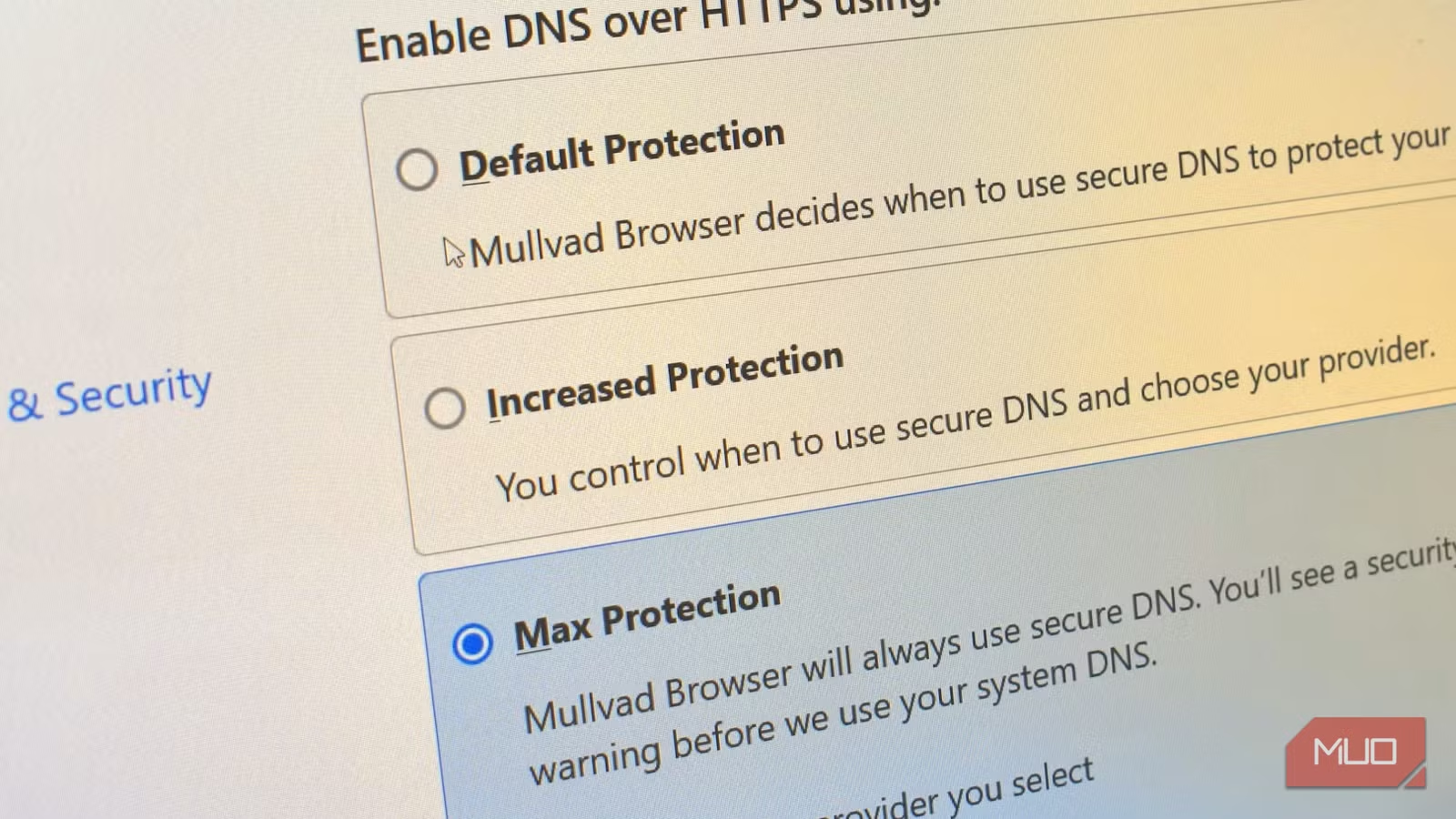
How to Change Your Browser's DNS Settings for Faster, Private Browsing in 2026
Your browser's default DNS settings are probably slowing you down and leaking your browsing history to your ISP. Here's why changing this one setting should be the first thing you do on any new device, and how to pick the right DNS provider for your needs.
Raspberry Pi at 15: Why the King of Single-Board Computers Is Losing Its Crown
After 15 years of dominating the hobbyist computing scene, the Raspberry Pi faces serious competition from cheaper alternatives, supply chain headaches, and a market that's evolved past its original mission. Here's what's happening and what it means for your next project.
Also Read

Edge Copilot Now Reads All Your Open Tabs at Once
Microsoft is rolling out a major Edge update that lets Copilot pull information from every tab you have open. The browser will also turn articles into AI podcasts, generate quizzes, and remember your conversations over time.

West Pharma Cyberattack Encrypts Systems, Steals Data
West Pharmaceutical Services, an S&P 500 company with $3 billion in annual revenue, disclosed a cyberattack that encrypted systems and exfiltrated data. The company detected the intrusion on May 4 and took global systems offline. Manufacturing has partially restarted, but full restoration remains incomplete.

Iranian Hackers Spent Week Inside Korean Electronics Firm
The MuddyWater hacking group infiltrated a major South Korean electronics manufacturer for seven days in February 2026, stealing credentials and establishing persistent access. Symantec researchers say the campaign marks a shift toward global targets and sophisticated evasion techniques.