5 Security Rules for Remote Workers Using Public Wi-Fi

Key Takeaways

- Public Wi-Fi networks, even password-protected ones, don't guarantee encrypted data transmission
- The NSA warns of 'evil twin' networks that mimic legitimate Wi-Fi to intercept your data
- Mobile hotspots using your cellular signal are more secure than public Wi-Fi
For millions of remote workers, the cafe table has become the corner office. Co-working spaces, hotel lobbies, and airport lounges are now standard workplaces. The pandemic accelerated this shift, and reliable high-speed internet made it permanent.
But working in public comes with real security risks. The convenience of free Wi-Fi can expose sensitive company data to anyone watching. Here's what you need to know to stay protected.
1. Check Your Employer's Remote Work Policy First
Before setting up shop at your favorite coffee spot, review your company's guidelines. Many organizations have specific rules about working in public spaces.
Some companies discourage or outright ban working from crowded public places due to data privacy risks. Others require privacy and confidentiality training before allowing remote work outside the home.
The British government makes its position clear in guidance for staff handling classified documents: "These environments can present additional risks, including being more freely accessible to people without the appropriate clearance and need-to-know."
Some employers also restrict working from certain countries. If you're planning to work while traveling internationally, check those rules before you book.
2. Pick Your Seat Like a Security Professional
Most people in a cafe are minding their own business. But "shoulder surfing" is real. Someone can read your screen, your emails, or your passwords just by glancing over.
Find a secluded spot. Put your back against a wall. This simple positioning makes it much harder for anyone to see what you're working on, even accidentally.
3. Use a Privacy Screen Filter
A privacy screen filter is a thin film with tiny louvres that blocks the view of your screen from angles. Someone sitting next to you sees only a dark screen. You see everything normally.
These cost between $20 and $60 depending on your laptop size. For anyone regularly working in public with sensitive information, it's a simple investment.
4. Avoid Public Wi-Fi Entirely
That free Wi-Fi in the airport lounge? Cybersecurity experts say don't use it.
The National Security Agency warns that any data sent over a public Wi-Fi network without a password is vulnerable to theft or manipulation. But here's what many people don't realize: even password-protected public Wi-Fi doesn't guarantee your data is encrypted.
The 'Evil Twin' Threat
“A malicious actor can set up a fake access point, also known as an evil twin, to mimic the nearby expected public Wi-Fi, resulting in that actor having access to all data sent over the network.”
— National Security Agency cybersecurity tip sheet
5. Use a Mobile Hotspot Instead
The safer alternative is a mobile hotspot. This uses your cellphone's signal to create a private Wi-Fi network. Only you can connect to it, and the data travels over your cellular connection rather than a shared public network.
Most smartphones have this feature built in. Check your cellular plan, as hotspot data may count against your monthly limit or require an add-on.
For frequent travelers, a dedicated mobile hotspot device can provide faster speeds and better battery life than tethering through your phone.
The Bottom Line
Remote work isn't going away. Neither are the security risks of working in public. The precautions are straightforward: know your company's rules, control who can see your screen, and avoid public Wi-Fi networks when handling anything sensitive.
A mobile hotspot and a privacy screen filter cost less than a week of coffee shop purchases. For anyone working with company data outside the office, they're basic equipment.
Related mobile security vulnerability
Frequently Asked Questions
Is it safe to use public Wi-Fi with a VPN?
A VPN adds encryption, but the NSA still recommends avoiding public Wi-Fi entirely. Evil twin networks can intercept your connection before the VPN activates. A mobile hotspot is more secure.
What is an evil twin Wi-Fi attack?
An attacker creates a fake Wi-Fi network with the same name as a legitimate one. When you connect, they can see all your unencrypted data. There's no visual difference between real and fake networks.
Does a password-protected public Wi-Fi keep my data safe?
No. The NSA says a Wi-Fi password doesn't mean your data is encrypted. Other users on the same network may still be able to intercept what you send.
How do I set up a mobile hotspot on my phone?
On iPhone, go to Settings > Personal Hotspot. On Android, go to Settings > Network & Internet > Hotspot & Tethering. Check your cellular plan for data limits.
What industries ban employees from working in public spaces?
Government agencies handling classified documents often restrict public workspace use. Finance, healthcare, and defense contractors frequently have similar policies due to data protection requirements.
Logicity's Take
Need Help Implementing This?
Source: mint
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read
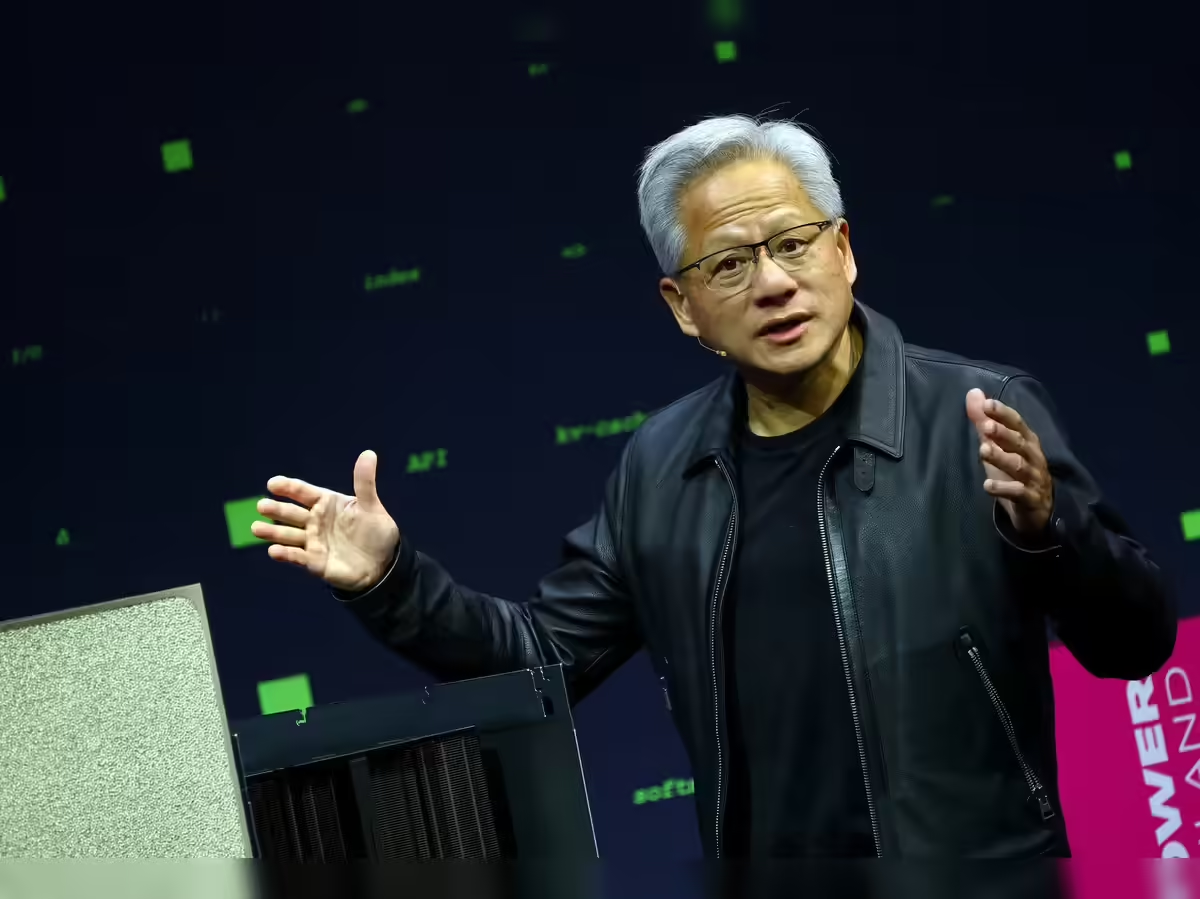
Nvidia CEO: 3D Digital Twins Are Critical for AI Marketing
Jensen Huang told Adobe Summit 2026 that companies need perfect 3D digital twins of their products before generative AI can activate them in creative environments. Adobe also announced CX Enterprise, an agentic AI system for managing customer lifecycles.
Samsung Finder vs Google Search Bar: A Better Way to Search
The Google search bar comes pre-installed on every Samsung Galaxy phone, but Samsung's own Finder tool offers deeper search capabilities. It can look inside apps, find contacts, locate settings, and surface documents. Here's how to make the switch.

Kia Vision Meta Turismo Previews Performance EV Future
Kia has unveiled full details of its Vision Meta Turismo concept car, a sports EV that blends 1960s grand touring aesthetics with gaming-inspired controls and AR entertainment features. The concept showcases the brand's vision for performance electric vehicles that prioritize experience both on the road and while parked.