OpenAI Launches GPT-5.5-Cyber for Critical Infrastructure Defense
Key Takeaways
- GPT-5.5-Cyber is available in limited preview exclusively for defenders securing critical infrastructure
- Trusted Access for Cyber is an identity-based framework that reduces refusals for verified defenders while blocking malicious requests
- Users must enable Advanced Account Security by June 1, 2026 to access the most capable models
OpenAI released GPT-5.5-Cyber on May 7, a specialized model designed for defenders protecting critical infrastructure. The company is offering it in limited preview, targeting security teams who need deeper capabilities than the standard GPT-5.5 provides.
This launch follows two related announcements. Two weeks ago, OpenAI released GPT-5.5, which the company calls its smartest model to date. Last week, it published "Cybersecurity in the Intelligence Age," an action plan outlining its vision for AI-powered defense. GPT-5.5-Cyber is the specialized implementation of that vision.
How Trusted Access for Cyber Works
Trusted Access for Cyber is an identity and trust-based framework. It verifies who is using the model and what they are doing with it. When defenders pass the vetting process, they get lower classifier-based refusals for legitimate security work.
The approved workflows include vulnerability identification and triage, malware analysis, binary reverse engineering, detection engineering, and patch validation. These are tasks where AI restrictions often get in the way of legitimate defensive research.
The framework continues blocking requests that could enable harm. OpenAI lists credential theft, stealth, persistence, malware deployment, and exploitation of third-party systems as activities that remain restricted even for verified users.
Two Models for Different Needs
OpenAI is positioning GPT-5.5 and GPT-5.5-Cyber as complementary tools serving different parts of the security ecosystem. For most teams, GPT-5.5 with Trusted Access for Cyber provides sufficient capability. The company describes it as the strongest broadly useful model for defensive work.
GPT-5.5-Cyber is more specialized and more permissive. It targets organizations responsible for critical infrastructure, those defending systems where a breach could cause widespread harm. The limited preview suggests OpenAI is being cautious about who gets access.
Security Requirements Tighten in June
Starting June 1, 2026, individual members of Trusted Access for Cyber who want to use the most capable models must enable Advanced Account Security. This means phishing-resistant authentication. Organizations with trusted access have alternative arrangements available, though OpenAI did not detail them in this announcement.
The requirement reflects a straightforward trade-off. More powerful capabilities demand stronger verification. A compromised account with enhanced access could cause significant damage, so OpenAI is raising the bar for authentication.
Who Shaped This Approach
OpenAI says its framework was informed by conversations with cybersecurity and national security leaders across federal and state government and major commercial entities. The company is trying to balance two competing pressures. Defenders need fewer restrictions to do their jobs. But fewer restrictions also create risk if access falls into wrong hands.
The tiered approach, with GPT-5.5 for most teams and GPT-5.5-Cyber for critical infrastructure defenders, attempts to solve this by matching capability to verification level.
Logicity's Take
Frequently Asked Questions
What is the difference between GPT-5.5 and GPT-5.5-Cyber?
GPT-5.5 is OpenAI's general-purpose model with enhanced security capabilities through Trusted Access for Cyber. GPT-5.5-Cyber is a specialized, more permissive model available only to defenders protecting critical infrastructure.
Who can access GPT-5.5-Cyber?
GPT-5.5-Cyber is available in limited preview to organizations responsible for securing critical infrastructure. Access requires vetting through OpenAI's Trusted Access for Cyber program.
What security workflows does Trusted Access for Cyber enable?
Approved workflows include vulnerability identification and triage, malware analysis, binary reverse engineering, detection engineering, and patch validation.
What is the Advanced Account Security requirement?
Starting June 1, 2026, individual Trusted Access for Cyber members using the most capable models must enable phishing-resistant authentication.
Related coverage on AI governance and oversight
Need Help Implementing This?
Source: OpenAI News
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Breaking: OReilly Releases New Books on Large Language Models and ChatGPT
OReilly has just released new books on large language models and ChatGPT, we take a closer look at what this means for the industry, **large language models are becoming more accessible** to developers and researchers.

URGENCY: Master 5 Essential Skills to Become a Prompt Engineer with TechTarget
As AI technology advances, the demand for skilled prompt engineers is on the rise. We explore the top 5 skills required to succeed in this field. From understanding natural language processing to developing creative problem-solving strategies, we dive into the essential skills needed to become a proficient prompt engineer.

SURPRISING TAKE: Prompt Engineering Is Not Just About Writing Better Prompts - Its About Revolutionizing Data Science
Become a better data scientist with these prompt engineering tips and tricks, learn how to leverage AI tools to improve your workflow, and discover the latest trends in data science. According to Gartner, AI will be a key driver of business innovation by 2025. We will explore how prompt engineering can help you stay ahead of the curve.

Why Most Businesses Are Already Behind on AI Prompt Engineering (And How to Catch Up Fast)
As AI continues to transform the business landscape, the role of prompt engineers is becoming increasingly crucial. We'll explore the 5 essential skills required to succeed in this field. From understanding natural language processing to designing effective prompts, we'll dive into the key skills needed to stay ahead of the curve.
Also Read

DJI Mini 4K Drone Drops to $209 in Limited Amazon Sale
The beginner-friendly DJI Mini 4K quadcopter is 30% off at Amazon, with the base model at $209 and the Fly More Combo at $309. The sub-249g drone requires no FAA registration and offers 31 minutes of flight time with 4K video stabilization.

Pentagon Releases 161 Declassified UFO Files With 30 Videos
The Pentagon published its first batch of declassified UAP files on May 8, responding to President Trump's February directive. The release includes 161 files with nearly 30 videos showing unidentified objects captured by military sensors, plus eyewitness accounts from Apollo astronauts.
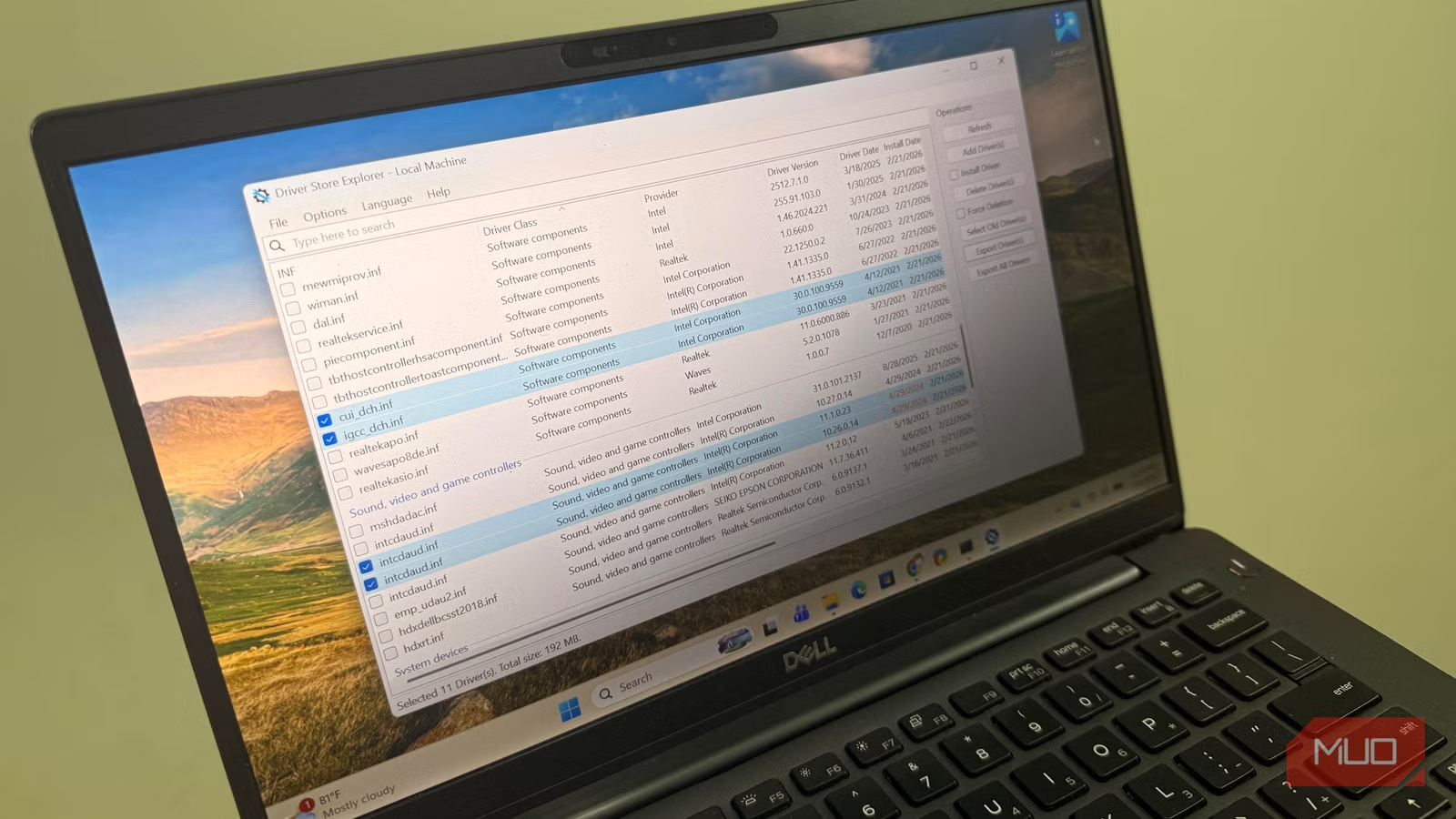
How to Clear Old Windows Drivers Wasting Your SSD Space
Windows stores every driver you've ever installed but never cleans up old versions. This hidden folder can grow to 30GB on gaming PCs. Here's how to safely reclaim that space.