Marimo RCE Vulnerability CVE-2026-39987: Hackers Exploited Critical Flaw Within 10 Hours of Disclosure

Key Takeaways

- CVE-2026-39987 has a 9.3 critical severity score and affects Marimo versions 0.20.4 and earlier
- Attackers exploited the flaw within 10 hours of disclosure, stealing .env files and cloud credentials
- 125 IP addresses began scanning for vulnerable instances within the first 12 hours
- The vulnerability exposes an unauthenticated WebSocket terminal endpoint
- Users running Marimo in edit mode with --host 0.0.0.0 are at highest risk
Read in Short
A critical flaw in Marimo, the popular Python notebook platform, lets anyone execute code on your machine without logging in. Hackers started exploiting it less than 10 hours after the vulnerability went public, and they're going straight for your cloud credentials and SSH keys. If you're running Marimo in edit mode, stop reading and update to version 0.23.0 right now.
Look, we've seen fast turnarounds on exploits before. But this one? Ten hours from disclosure to active attacks. That's not a proof-of-concept sitting on GitHub. That's someone reading a security advisory over their morning coffee and launching credential theft operations before lunch.
The target is Marimo, an open-source reactive Python notebook that's become pretty popular with data scientists, ML engineers, and anyone building data apps. With 20,000 GitHub stars and 1,000 forks, it's not some obscure tool. Plenty of folks are running this thing, and a scary number of them probably have it exposed to the internet in ways they shouldn't.
What Makes CVE-2026-39987 So Dangerous
Here's the thing about this vulnerability. It's almost embarrassingly simple. The WebSocket endpoint at /terminal/ws gives you an interactive terminal session. No password. No authentication token. No nothing. Just connect and you've got shell access with whatever privileges Marimo is running under.
GitHub slapped it with a 9.3 out of 10 severity score, which tracks. Pre-authentication RCE is about as bad as it gets. You don't need to phish anyone, crack any passwords, or chain together multiple exploits. You just... connect.
Who's Actually Affected?
Not everyone running Marimo is vulnerable. The flaw specifically impacts users who: (1) deployed Marimo as an editable notebook, AND (2) exposed it to a shared network using the --host 0.0.0.0 flag while in edit mode. If you're running it locally without network exposure, you're probably fine. Probably.
The vulnerable versions are 0.20.4 and earlier. Marimo disclosed the issue on April 8th and pushed out version 0.23.0 yesterday to fix it. That's a reasonable response time from the developers. The problem is what happened in between.
The Attack Timeline: From Advisory to Exploitation
Sysdig's researchers have been tracking this one closely, and their timeline is genuinely alarming. The speed here isn't just impressive from a technical standpoint. It shows how sophisticated threat actors have become at weaponizing vulnerability disclosures.
So attackers had at least a three-day window where the vulnerability was public knowledge but no patch existed. That's not ideal. And given the simplicity of the exploit, you didn't need to be a genius to weaponize it.
Inside the Attack: How Hackers Are Stealing Your Credentials
What's interesting about the attacks Sysdig observed is that they weren't automated spray-and-pray operations. This was someone sitting at a keyboard, manually poking around, making decisions in real-time. The researchers described them as a "methodical operator" with a hands-on approach.
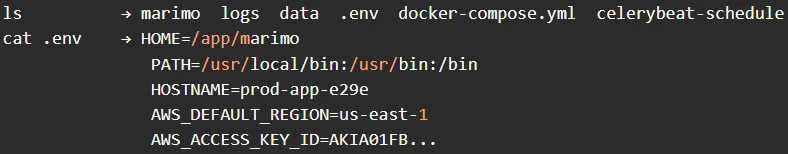
The attack sequence went something like this. First, the attacker connected to the vulnerable WebSocket endpoint and ran a quick test to confirm they had code execution. Then they disconnected. Classic validation step, takes just seconds.
- Connect to /terminal/ws endpoint and verify RCE works
- Disconnect, then reconnect for the actual operation
- Run basic recon commands: pwd, whoami, ls
- Navigate directories and hunt for SSH-related locations
- Immediately target the .env file for credentials
- Extract environment variables including cloud secrets
- Probe for additional sensitive files and SSH keys
The entire credential harvesting phase? Under three minutes. That's how fast your AWS keys, database passwords, and API tokens can walk out the door. And about an hour later, the same attacker came back for a second round using the identical exploit chain.
If you're building data apps with tools like Marimo, you might also be interested in how voice-controlled AI agents handle command execution and the security implications involved.
Why This Matters Beyond Marimo
Okay, so maybe you don't use Marimo. Why should you care? Because this pattern is becoming disturbingly common.
Development tools, notebooks, and local-first applications often ship with convenience features that assume you're running them in a safe environment. Exposed WebSocket endpoints. Default open ports. No auth on admin interfaces. It's fine when you're testing locally. It's a disaster when you accidentally expose it to the internet or a shared network.
And the time from vulnerability disclosure to exploitation keeps shrinking. We used to talk about days or weeks. Now we're measuring in hours. Security teams can't patch fast enough when attackers are moving this quickly.
“The entire credential access phase was completed in less than three minutes.”
— Sysdig Research Report, April 2026
What You Need to Do Right Now
If you're running Marimo anywhere, here's your action plan. Don't wait until tomorrow.
- Update to Marimo version 0.23.0 immediately if you haven't already
- Check your deployment configuration for --host 0.0.0.0 flags
- Review your .env files and rotate any credentials that might have been exposed
- Check your logs for connections to the /terminal/ws endpoint from unknown IPs
- If you must expose Marimo to a network, put it behind proper authentication
- Consider running notebook environments in isolated containers with limited credentials
Credential Rotation Checklist
If you think you might have been compromised, rotate these immediately: AWS/GCP/Azure access keys, database connection strings, API tokens for third-party services, SSH keys stored on the machine, and any secrets in your .env files. Better paranoid than pwned.
The Bigger Picture on Disclosure Timelines
There's an ongoing debate in security circles about responsible disclosure windows. How long should vendors get to fix issues before details go public? This incident is going to add fuel to that fire.
On one hand, public disclosure pressures vendors to actually ship fixes. On the other hand, when attackers can weaponize advisories in under 10 hours, you're essentially handing them a roadmap to vulnerable systems. There's no perfect answer here.
What's clear is that if you're running any developer tools exposed to a network, you need to be monitoring security advisories like a hawk. And you need a plan for rapid patching that doesn't involve waiting for your normal maintenance window.
The days of "we'll patch it next sprint" are over. When exploits drop this fast, you patch now or you deal with the consequences.
Frequently Asked Questions
Is my local Marimo installation vulnerable?
If you're running Marimo purely locally without the --host 0.0.0.0 flag and not exposing it to any network, you're likely safe. The vulnerability requires network access to the WebSocket endpoint.
How do I know if I've been compromised?
Check your server logs for connections to /terminal/ws from unfamiliar IP addresses. Also review your .env file access times and look for any unauthorized changes to your system.
What version of Marimo fixes this vulnerability?
Version 0.23.0, released on April 11, 2026, patches CVE-2026-39987. Update immediately if you're running any earlier version.
Are other Python notebook tools affected?
This specific vulnerability only affects Marimo. However, the underlying issue of unauthenticated endpoints is common across many development tools, so it's worth auditing your entire stack.
The kicker? This probably won't be the last time we see something like this. Development tools are increasingly powerful, increasingly networked, and increasingly targeted. Stay paranoid, keep your stuff updated, and for the love of all that is holy, don't expose your development environments to the open internet.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read

13 Shrek Merch Items Trending Ahead of the 25th Anniversary
The Shrek franchise turns 25 in 2026, and collectors are snapping up everything from LEGO sets to Swarovski crystals. With Shrek 5 confirmed for 2027, here's what's actually selling right now.
Inc42 AI Summit 2026: India's $126 Bn AI Dream Hits Reality
At the Inc42 AI Summit 2026 in Bengaluru, India's top startup executives confronted an uncomfortable truth: the country's path to a $126 billion AI market by 2030 is blocked by capital, talent, and infrastructure gaps. From Rapido's AI-generated code to PhonePe's distribution thesis, leaders outlined what it will actually take to compete.

2027 Audi RS5: Can a 5,200 lb PHEV Still Be a Driver's Car?
Audi Sport's new RS5 pairs a twin-turbo V6 with plug-in hybrid tech borrowed from its Formula 1 program. The result is 630 hp and 54 miles of electric range. The cost is 1,100 lbs of extra weight.