GitHub RCE Flaw: 88% of Enterprise Servers Still Vulnerable

Key Takeaways

- Any authenticated GitHub user could execute arbitrary commands on backend servers with a single git push command
- GitHub Enterprise Server admins must upgrade to version 3.19.3 or later immediately
- This is one of the first critical vulnerabilities discovered in closed-source binaries using AI tools
A single git push command. That's all it took to compromise GitHub's internal infrastructure.
Wiz Research discovered CVE-2026-3854, a critical vulnerability in GitHub's internal git protocol that affected both GitHub.com and GitHub Enterprise Server. The flaw allowed any authenticated user to execute arbitrary commands on GitHub's backend servers using nothing but a standard git client.
GitHub patched the vulnerability on GitHub.com within 6 hours of Wiz's report. However, the situation for self-hosted GitHub Enterprise Server installations is far more concerning. According to Wiz's data, 88% of instances are still running vulnerable versions.
How the Exploit Works
The vulnerability stems from an injection flaw in GitHub's internal protocol. Despite the complexity of the underlying system, exploiting it is remarkably simple. An attacker with any authenticated GitHub account could craft a malicious git push that would execute commands on GitHub's servers.
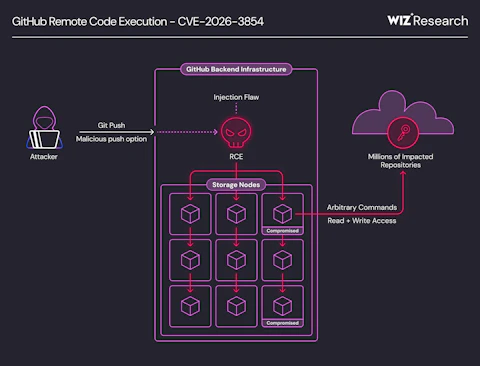
On GitHub.com, the vulnerability enabled remote code execution on shared storage nodes. Wiz confirmed that millions of public and private repositories belonging to other users and organizations were accessible on the affected nodes. This means an attacker could potentially access code from any repository stored on the same node.
The impact on GitHub Enterprise Server is even worse. The same vulnerability grants full server compromise, including access to all hosted repositories and internal secrets. For organizations running their own GHES installations, this represents a complete security failure.
AI-Assisted Discovery
This vulnerability marks a significant shift in security research methodology. According to Wiz, CVE-2026-3854 is one of the first critical vulnerabilities discovered in closed-source binaries using AI. This suggests AI tools are becoming practical aids for finding flaws that would be difficult to identify through traditional reverse engineering.
“A finding of this caliber and severity is rare, earning one of the highest rewards available in our Bug Bounty program, and serves as a reminder that the most impactful security research comes from skilled researchers who know how to ask the right questions.”
— Alexis Wales, GitHub CISO
What You Need to Do
If you use GitHub.com, you're already protected. GitHub mitigated the issue on their hosted platform within 6 hours of receiving Wiz's report. No action is required.
If you run GitHub Enterprise Server, you need to act now. The vulnerability affects all GHES versions up to and including 3.19.1.
Patched Versions
- 3.14.24
- 3.15.19
- 3.16.15
- 3.17.12
- 3.18.6
- 3.19.3
Upgrade to version 3.19.3 or the latest patch for your major version. Given that 88% of instances remain vulnerable, most GHES administrators have not yet applied this fix.

Wiz customers can identify vulnerable instances using a pre-built query in the Wiz Threat Center. The query locates all GHES installations running affected versions.
Why This Matters
GitHub Enterprise Server is popular among organizations that need to keep source code on their own infrastructure. Banks, defense contractors, healthcare companies, and regulated industries often choose GHES specifically because they don't want code on third-party servers.
The irony is stark. Organizations chose self-hosted GitHub to maintain control over their security posture. Now those same organizations face a vulnerability that grants attackers complete access to everything. All hosted repositories. All internal secrets. Full server compromise.
The 88% unpatched figure is alarming but not surprising. Enterprise infrastructure teams often lag behind security patches due to change management processes, testing requirements, and maintenance windows. This vulnerability should jump to the front of every queue.
Logicity's Take
Frequently Asked Questions
Is GitHub.com still vulnerable to CVE-2026-3854?
No. GitHub patched the vulnerability on GitHub.com within 6 hours of receiving the report from Wiz Research. No user action is required for the hosted platform.
Which GitHub Enterprise Server versions are affected?
All versions up to and including 3.19.1 are vulnerable. Patched versions are 3.14.24, 3.15.19, 3.16.15, 3.17.12, 3.18.6, and 3.19.3.
What can an attacker do with this vulnerability?
On GitHub.com, attackers could access millions of public and private repositories on shared storage nodes. On GitHub Enterprise Server, they gain full server compromise with access to all repositories and internal secrets.
How difficult is CVE-2026-3854 to exploit?
Very easy. Any authenticated user can exploit it using a standard git client with a single git push command. No special tools or deep technical knowledge required.
How was this vulnerability discovered?
Wiz Research found it using AI-assisted analysis of closed-source binaries. GitHub's CISO noted this is one of the first critical vulnerabilities discovered this way.
Another critical security vulnerability requiring immediate attention
Related coverage of infrastructure security incidents
Need Help Implementing This?
Source: Hacker News: Best
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
Robotaxi Companies Are Hiding How Often Humans Take the Wheel
Autonomous vehicle firms like Waymo and Tesla are under scrutiny for refusing to disclose how often remote operators step in to control their self-driving cars. A Senate investigation reveals major gaps in transparency, raising safety and accountability concerns.

Wisconsin Governor Throws a Wrench in Age Verification Plans
Wisconsin Governor Tony Evers has vetoed a bill that would have required residents to verify their age before accessing adult content online, citing concerns over privacy and data security. This move comes as several other states have already implemented similar age check requirements. The veto has significant implications for the future of online age verification.

Apple's App Store Empire Under Siege: The Battle for the Future of Tech
The long-running feud between Apple and Epic Games has reached a boiling point, with Apple preparing to take its case to the Supreme Court. The tech giant is fighting to maintain control over its App Store, while Epic Games is pushing for more freedom for developers. The outcome could have far-reaching implications for the entire tech industry.

Tesla's Remote Parking Feature: The Investigation That Didn't Quite Park Itself
The US auto safety regulators have closed their investigation into Tesla's remote parking feature, but what does this mean for the future of autonomous driving? We dive into the details of the investigation and what it reveals about the technology. The National Highway Traffic Safety Administration found that crashes were rare and minor, but the investigation's closure doesn't necessarily mean the feature is completely safe.
Also Read

iPhone Ultra vs Huawei Pura X Max: Dummy Unit Shows Size Parity
A hands-on comparison of an iPhone Ultra dummy unit against the Huawei Pura X Max reveals the two foldables share nearly identical dimensions. With Samsung's Galaxy Z Fold Wide also incoming, 2025 is shaping up as the year large foldables go mainstream.
Roku's Free Channels Replaced My Cable. Here's How.
A veteran tech writer shares his experience ditching cable for Roku's free streaming options. With over 500 FAST channels and a growing content library, the platform now captures 3% of all U.S. TV viewership.
4 Ways to Automate Jasper AI With Zapier Workflows
Zapier has published new integration templates connecting Jasper AI to common marketing tools. The automations handle blog draft generation, product descriptions, content summarization, and personalized outreach. Marketing teams can trigger Jasper to write directly from spreadsheets, ecommerce platforms, and CRMs.