Millions of PC Users Downloaded Malware From the Official CPU-Z Website — Here's What Happened

In a shocking twist, hackers breached the official CPUID website and swapped out legitimate download links for CPU-Z and HWMonitor with trojanized malware. For about six hours on April 9-10, 2026, anyone downloading these wildly popular system monitoring tools got a nasty surprise instead. The attackers exploited a secondary API while the lead developer was conveniently on vacation.
Key Takeaways
- CPUID's official website served malicious downloads for approximately six hours between April 9-10, 2026
- The malware was designed to steal browser credentials, particularly targeting Google Chrome's saved passwords
- The same threat actors previously targeted FileZilla users in March 2026, suggesting a pattern of attacking popular utilities
- Windows Defender and 32 antivirus engines on VirusTotal flagged the malicious files
- CPUID has since fixed the breach and now serves clean software versions
In This Article
- What Exactly Went Down at CPUID?
- This Wasn't Your Average Run-of-the-Mill Malware
- Did You Download CPU-Z or HWMonitor Recently? Here's How to Know If You're at Risk
- The Alarming Rise of Supply Chain Attacks in 2026
- CPUID's Response and What They're Saying
- How to Protect Yourself From Supply Chain Attacks
What Exactly Went Down at CPUID?
If you've ever built a PC or obsessed over your system specs (guilty as charged), you've probably used CPU-Z or HWMonitor. These utilities from CPUID have been go-to tools for millions of enthusiasts and professionals alike. But for a terrifying window of about six hours this week, downloading these tools from the official source meant potentially infecting your system with sophisticated malware.
- Attackers compromised a secondary API on CPUID's infrastructure, allowing them to poison the download links on the legitimate website
- Instead of receiving the expected software files, users downloaded a trojanized installer masquerading as HWiNFO — a completely different monitoring tool from another developer
- The malicious file was named 'HWiNFO_Monitor_Setup' and launched a suspicious Russian-language installer wrapped in Inno Setup
- Importantly, the original signed binaries remained untouched on CPUID's servers — only the distribution links were manipulated
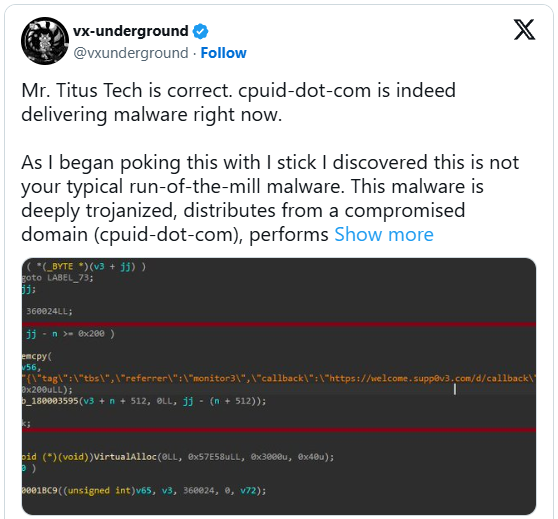
Mr. Titus Tech is correct. cpuid-dot-com is indeed delivering malware right now.
— vx-underground (@vxunderground) April 10, 2026
As I began poking this with I stick I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs… https://t.co/ubkXmG7LKV pic.twitter.com/jPlAMmpijN

This Wasn't Your Average Run-of-the-Mill Malware
Security researchers who dissected the malicious payload were impressed — and not in a good way. This wasn't some amateur script kiddie operation. The malware demonstrated sophisticated evasion techniques that show real expertise in bypassing modern security tools.
- The threat operated almost entirely in system memory, making it harder to detect through traditional file-based scanning
- It employed multi-stage deployment, meaning the initial download was just the first step in a complex infection chain
- The malware proxied NTDLL functions through .NET assemblies to dodge endpoint detection and response (EDR) solutions
- Its primary goal appears to be credential theft, specifically attempting to compromise Google Chrome's IElevation COM interface to extract and decrypt saved passwords
Did You Download CPU-Z or HWMonitor Recently? Here's How to Know If You're at Risk
The good news is that the attack window was relatively short. The bad news is that CPU-Z and HWMonitor are incredibly popular utilities, meaning even six hours of exposure could have impacted thousands of users. Reddit users first raised the alarm when they noticed something fishy about their downloads.
- The breach occurred between April 9-10, 2026, lasting approximately six hours
- Windows Defender actively flagged the malicious installer, providing some protection for users with enabled security features
- VirusTotal showed 32 different security engines detecting the threat, classifying it variously as Tedy Trojan, Artemis Trojan, or infostealer malware
- If you downloaded either tool during this window and bypassed security warnings, you should immediately scan your system and change your browser-saved passwords

The Alarming Rise of Supply Chain Attacks in 2026
This CPUID breach isn't an isolated incident — it's part of a disturbing trend that's been accelerating throughout 2026. Supply chain attacks have become the weapon of choice for sophisticated threat actors because they exploit the trust users place in legitimate software sources. When you download from an official website, you expect safety. Attackers know this.
- The same infrastructure used in the CPUID attack was previously employed against FileZilla users in March 2026, suggesting a organized threat group targeting popular utilities
- Just weeks earlier, the Axios npm package was compromised in an attack attributed to North Korean state actors, affecting a library with over 70 million weekly downloads
- The TeamPCP group systematically compromised security tools including Trivy, KICS, and LiteLLM between February and March 2026
- According to Group-IB's 2026 threat report, cybercriminals have shifted decisively from isolated intrusions toward ecosystem-wide compromises through trusted vendors
CPUID's Response and What They're Saying
To their credit, CPUID acted quickly once they discovered the compromise. However, the timing of the attack — when the lead developer was away on holiday — suggests the threat actors may have been watching and waiting for the perfect moment to strike.
- CPUID confirmed the breach was limited to a 'secondary feature' (a side API) rather than their core infrastructure
- The company emphasized that their original signed files were never compromised — only the download links were manipulated
- The website now serves clean, verified versions of both CPU-Z and HWMonitor
- Investigations are ongoing to determine the full scope of the attack and identify responsible parties
How to Protect Yourself From Supply Chain Attacks
The scary reality is that supply chain attacks exploit our natural trust in legitimate sources. When even official websites can serve malware, what can everyday users do? Actually, quite a lot.
- Always keep your operating system's built-in security features enabled — Windows Defender caught this threat for many users
- Verify file hashes when possible; legitimate developers often publish checksums you can compare against your download
- Be suspicious of unexpected installers, especially those in different languages or from unfamiliar frameworks
- Consider running new software downloads through VirusTotal before installation, even from trusted sources
- Keep your browser passwords in a dedicated password manager rather than built-in browser storage, limiting exposure if credentials are targeted
“As I began poking this with a stick, I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain, performs file masquerading, is multi-staged, operates almost entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly.”
— vxunderground, Security Researcher
“Investigations are still ongoing, but it appears that a secondary feature (basically a side API) was compromised for approximately six hours between April 9 and April 10, causing the main website to randomly display malicious links. Our signed original files were not compromised. The breach was found and has since been fixed.”
— CPUID Spokesperson
Final Thoughts
The CPUID breach serves as a stark reminder that in 2026, even the most trusted software sources can become attack vectors. As supply chain attacks continue to surge — targeting everything from system utilities to critical security tools — both developers and users need to adapt. For software makers, this means hardening build environments and implementing robust API security. For users, it means staying vigilant even when downloading from official sources. The era of blind trust in software distribution is officially over, and the sooner we all accept that reality, the safer our systems will be.
Sources & Credits
Originally reported by BleepingComputer
Manaal Khan
Tech & Innovation Writer
Related Articles
Browse all
AI Apocalypse: The Dark Side of Artificial Intelligence Exposed

The 'V' Word: Why Moderna is Ditching 'Vaccine' for its Cancer Breakthrough

The Clock is Ticking: Unlock the Secrets of TechCrunch Disrupt 2026 Before It's Too Late

Humanity Just Went Farther Into Space Than Ever Before — And Made It Back Alive
Also Read

France Declares Digital Independence: Ditching Windows for Linux in a Bold Move

The Dark Side of Green Tech: Why a $900 Million Battery Recycler Just Went Bust
