Seiko USA Breach 2026: What E-Commerce Leaders Must Know

Key Takeaways

- Website defacements with ransom demands are becoming a preferred extortion tactic against retail brands
- Shopify backend access can expose customer names, emails, purchase history, and shipping addresses
- 72-hour ransom deadlines create pressure that leads to poor decision-making without incident response plans
According to [BleepingComputer](https://www.bleepingcomputer.com/news/security/seiko-usa-website-defaced-as-hacker-claims-customer-data-theft/), the Seiko USA website was defaced over the weekend with attackers claiming they stole the company's Shopify customer database and threatening to leak it unless a ransom is paid.
If you're running e-commerce operations on Shopify or any third-party platform, this attack should be on your Monday morning agenda. Here's why: the attackers didn't just steal data. They turned Seiko's own website into a billboard advertising their crime. That's a calculated move designed to maximize pressure and public embarrassment.
What Happened in the Seiko USA Website Attack?
Visitors to the Press Lounge section of Seiko USA's website were greeted with a page titled 'HACKED' that replaced normal content with what appeared to be a ransom demand. The attackers claim they breached Seiko's Shopify backend and downloaded the entire customer database.
The defacement message read: 'This is an urgent security notification regarding your Shopify store. Your customer database has been compromised. We have successfully breached your Shopify store's security systems and downloaded the entire customer database.'
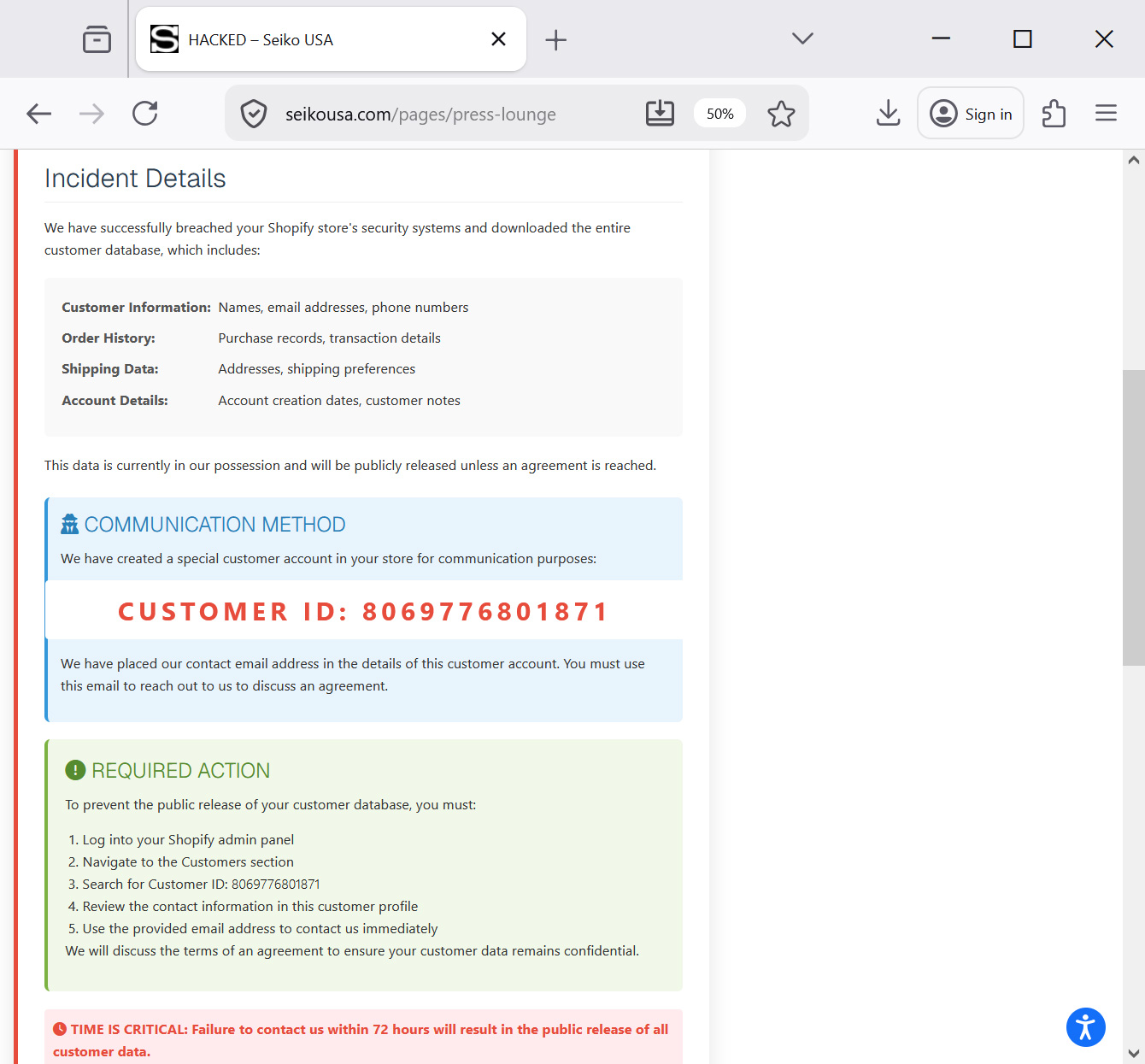
What Customer Data Was Allegedly Stolen?
According to the threat actors' claims, the stolen database contains four categories of sensitive information. While BleepingComputer has not verified whether these claims are legitimate, the scope of potential exposure is significant for any retail operation.
- Customer Information: Names, email addresses, phone numbers
- Order History: Purchase records, transaction details
- Shipping Data: Addresses, shipping preferences
- Account Details: Account creation dates, customer notes
For business leaders, this data combination is particularly toxic. It's not just emails that could be used for phishing. It's complete customer profiles that reveal purchasing behavior, physical addresses, and communication preferences. That's identity theft waiting to happen.
Why Are Hackers Using Website Defacement for Extortion?
This attack represents an evolution in extortion tactics. Traditional ransomware encrypts files and demands payment for the decryption key. This approach is different. The attackers are using public shame as a weapon.
By defacing the website, they accomplished several things simultaneously. They proved they had access to Seiko's systems. They created immediate reputational damage. And they put the company on a public clock, with customers and media watching.
The Extortion Playbook
The attackers instructed Seiko USA to locate a specific customer account (ID 8069776801871) within the Shopify admin panel, where they had added a contact email address. This proves backend access while forcing the victim to use their own systems to find negotiation details. It's a clever psychological tactic that demonstrates control.
Seiko USA has not publicly confirmed the incident or responded to press inquiries, but has since removed the extortion message from their website. This silence is common but problematic. It leaves customers wondering whether their data is compromised.
How Much Does a Shopify Data Breach Actually Cost?
The financial impact of an e-commerce breach extends far beyond any ransom payment. Business leaders need to consider the full cost stack when evaluating their security investments.
| Cost Category | Estimated Range | Timeline |
|---|---|---|
| Incident Response & Forensics | $50,000 - $500,000 | Immediate |
| Customer Notification (per record) | $1 - $3 per customer | 30-60 days |
| Legal & Regulatory Fines | $100,000 - $5M+ | 6-24 months |
| Brand Reputation Damage | 10-25% revenue impact | 12-36 months |
| Customer Churn | 5-15% of affected customers | 6-12 months |
For a brand like Seiko with significant e-commerce operations, even a conservative estimate puts potential costs in the millions. And that's before considering the operational disruption of taking systems offline for forensic investigation.
Another recent case study in how companies handle breach disclosures and what it means for technology leaders
Is Your Shopify Store at Risk of Similar Attacks?
This attack raises uncomfortable questions for any business running on Shopify or similar platforms. The attackers claimed they breached 'Shopify store's security systems,' but the exact attack vector remains unclear. This could mean compromised admin credentials, a vulnerable third-party app, or exploitation of API access.
Here's what we know about common Shopify attack vectors that every e-commerce leader should be evaluating:
- Compromised admin credentials through phishing or credential stuffing attacks
- Vulnerable third-party apps with excessive permissions accessing customer data
- API keys exposed in public code repositories or shared with contractors
- Session hijacking through unsecured staff workstations or networks
- Social engineering attacks targeting Shopify support to gain account access
The uncomfortable truth is that hosted platforms like Shopify handle core security well, but your admin access, app permissions, and staff practices create the attack surface. Most breaches trace back to human factors, not platform vulnerabilities.
What Should E-Commerce Leaders Do Right Now?
If you're responsible for e-commerce operations, this incident should trigger an immediate security review. Here's a prioritized action list based on the attack patterns we're seeing in 2026.
Immediate Actions (This Week)
1. Audit all admin accounts and remove inactive users 2. Enable mandatory 2FA for all staff with backend access 3. Review third-party app permissions and remove unused integrations 4. Check for API key exposure in any public code repositories 5. Verify your incident response plan includes website defacement scenarios
Beyond the immediate checklist, this is a conversation for your next leadership meeting. The question isn't whether you'll face an attack. It's whether your response plan accounts for the reputational dimensions of modern extortion tactics.
Traditional incident response focuses on containment and recovery. But when attackers use your own website to broadcast their ransom demands, your PR and legal teams need to be activated immediately. Do you have those relationships established before an incident?
The Bigger Picture: Retail Cyber Extortion Is Accelerating
This Seiko attack doesn't exist in isolation. We're seeing a clear pattern of threat actors targeting retail and e-commerce operations with increasingly sophisticated extortion schemes.
Recent incidents include the Kraken crypto-exchange extortion following an insider breach, stolen Rockstar Games analytics data leaked by extortion gangs, and the Snowflake customer data theft that impacted multiple companies through a SaaS integrator breach. The common thread: attackers are finding that data theft and public pressure often pay better than ransomware.
For business leaders, this means security spending needs to account for both prevention and response capabilities. You can't stop every attack, but you can control how quickly and effectively you respond. The companies that weather these incidents best have practiced their response before they need it.
Another cost optimization analysis for business decision-makers managing operational expenses
Seiko USA Breach FAQ: What Business Leaders Are Asking
Frequently Asked Questions
Was the Seiko USA data breach confirmed by the company?
No. Seiko USA has not publicly confirmed the breach or responded to press inquiries. They have removed the defacement message from their website, but haven't issued a statement about whether customer data was actually compromised.
How much would a ransom like this typically cost?
Ransom demands in retail data theft cases typically range from $100,000 to several million dollars, depending on the company's size and the sensitivity of stolen data. However, paying doesn't guarantee the data won't be leaked, and many organizations face regulatory issues if they pay.
Should my company pay if we face a similar extortion attempt?
This requires legal counsel, but generally paying is discouraged. The FBI advises against ransom payments as they fund criminal operations and don't guarantee data deletion. Focus instead on incident response, customer notification, and long-term security improvements.
How can I tell if my Shopify store has been compromised?
Check admin activity logs for unfamiliar logins or actions. Review recent changes to customer accounts, especially look for newly created accounts with unusual patterns. Audit third-party app permissions and API access. Consider hiring a security firm for a professional assessment if you suspect compromise.
What's the timeline for customer notification after a breach?
This varies by jurisdiction. GDPR requires notification within 72 hours of discovery. US state laws vary from 30 to 90 days. California's CCPA requires 'expedient' notification. Have your legal team review applicable requirements before an incident occurs.
Logicity's Take
At Logicity, we build e-commerce integrations and have implemented security hardening for clients running on Shopify and custom platforms. This Seiko attack highlights something we stress in every project: your platform's security is only as strong as your access management practices. We've seen Indian e-commerce businesses assume that hosting on Shopify or similar platforms means security is handled. It's not that simple. The platform handles infrastructure security, but admin credentials, third-party app permissions, and API access are your responsibility. For any business running online retail operations, our practical advice is this: conduct a quarterly audit of who has admin access and what third-party apps are installed. Remove anything unused. Enable 2FA without exceptions. And have a documented plan for what happens if someone defaces your website at 2 AM on a Saturday. The attackers chose a weekend for a reason. Your response capability shouldn't take weekends off.
Need Help Securing Your E-Commerce Operations?
Logicity helps businesses implement security best practices for their web applications and e-commerce platforms. From access management audits to incident response planning, we bring practical experience to protecting your customer data. Reach out to discuss your security posture before you need to discuss a breach.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.