You Won't Believe How Hackers Just Hijacked a Top Developer Tool

The popular Axios HTTP client was compromised by North Korean hackers, who used a clever social engineering tactic to gain access to a maintainer's account. This led to the release of two malicious versions of Axios, putting countless systems at risk. The incident highlights the importance of cybersecurity and the evolving tactics of threat actors.
Key Takeaways
- North Korean hackers compromised the Axios HTTP client using social engineering
- Two malicious versions of Axios were released, putting systems at risk
- The attack highlights the importance of cybersecurity and evolving tactics of threat actors
In This Article
- Introduction to the Attack
- The Social Engineering Tactic
- Insights from the Maintainer
- The Impact of the Attack
- Conclusion and Next Steps
Introduction to the Attack
In a shocking turn of events, the maintainers of the popular Axios HTTP client discovered that one of their developers had fallen victim to a sophisticated social engineering campaign. This campaign, linked to North Korean hackers, led to the compromise of a maintainer's account and the release of two malicious versions of Axios.
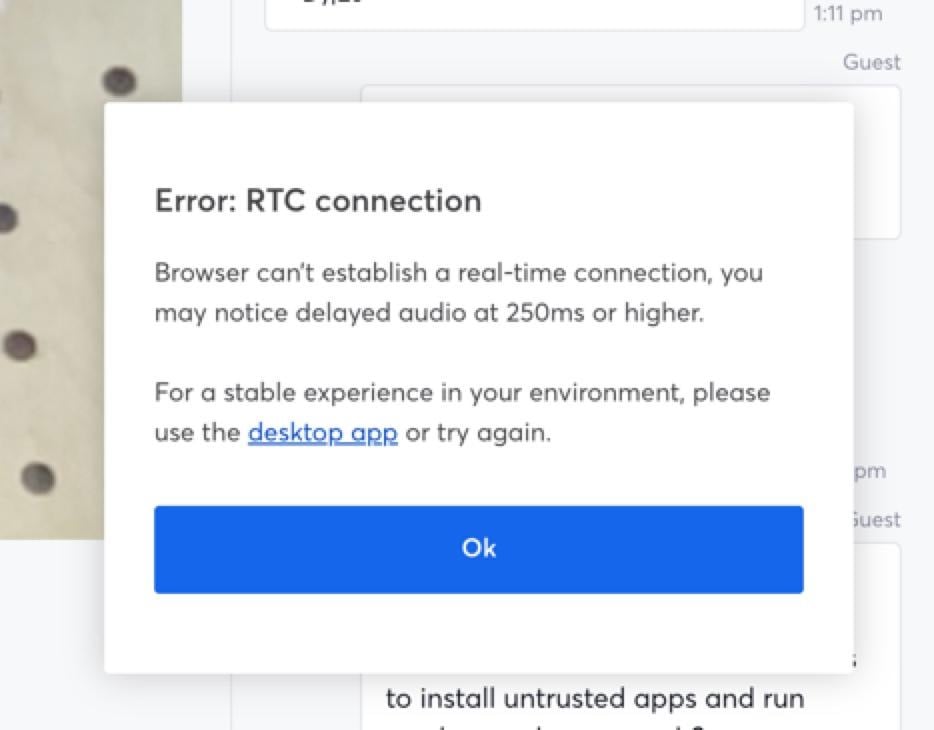
- The attackers used a fake Microsoft Teams error message to trick the maintainer into installing malware
- The malware gave the attackers remote access to the maintainer's device, allowing them to obtain npm credentials
The Social Engineering Tactic
The attackers used a clever social engineering tactic to gain the trust of the maintainer. They impersonated a legitimate company, created a fake Slack workspace, and even staged a meeting on Microsoft Teams. As Jason Saayman, the lead maintainer, explained:
- The attackers created a convincing Slack workspace with fake profiles and activity
- They scheduled a meeting on Microsoft Teams, which appeared to include numerous people
Insights from the Maintainer
Jason Saayman shared his experience with the social engineering attack, providing valuable insight into the tactics used by the attackers. As he noted, 'The slack was thought out very well, they had channels where they were sharing linked-in posts, the linked in posts I presume just went to the real companys account but it was super convincing etc.'
- The attackers used a fake error message to prompt the maintainer to install a malicious update
- The update gave the attackers remote access to the maintainer's device
The Impact of the Attack
The compromise of the Axios HTTP client had significant implications, as two malicious versions of the software were released to the npm package registry. These versions injected a dependency named plain-crypto-js, which installed a remote access trojan (RAT) on macOS, Windows, and Linux systems.
- The malicious versions were available for roughly three hours before being removed
- Systems that installed the malicious versions during this time should be considered compromised
Conclusion and Next Steps
The attack on the Axios HTTP client serves as a reminder of the importance of cybersecurity and the evolving tactics of threat actors. As the Google Threat Intelligence Group noted, 'GTIG attributes this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018.'
- The Axios maintainers have taken steps to prevent similar incidents in the future
- The incident highlights the need for increased vigilance and cybersecurity measures
“The slack was thought out very well, they had channels where they were sharing linked-in posts, the linked in posts I presume just went to the real companys account but it was super convincing etc.”
— Jason Saayman, Lead Maintainer
“GTIG attributes this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018.”
— Google Threat Intelligence Group
Final Thoughts
The attack on the Axios HTTP client is a wake-up call for the tech community, highlighting the importance of cybersecurity and the need for increased vigilance. As threat actors continue to evolve their tactics, it's essential for developers and maintainers to stay one step ahead and prioritize security. By learning from this incident and taking proactive measures, we can work towards a safer and more secure digital landscape.
Sources & Credits
Originally reported by BleepingComputer
Manaal Khan
Tech & Innovation Writer
More Articles

The Dark Side of AI: How Medvi's Billions Were Built on Deception

The Dark Side of AI: How Flattering Chatbots Can Manipulate Even the Most Rational Minds
