Ivanti EPMM Zero-Day Exploited: 850 Servers Exposed Online

Key Takeaways

- CVE-2026-6973 allows remote code execution on EPMM 12.8.0.0 and earlier versions
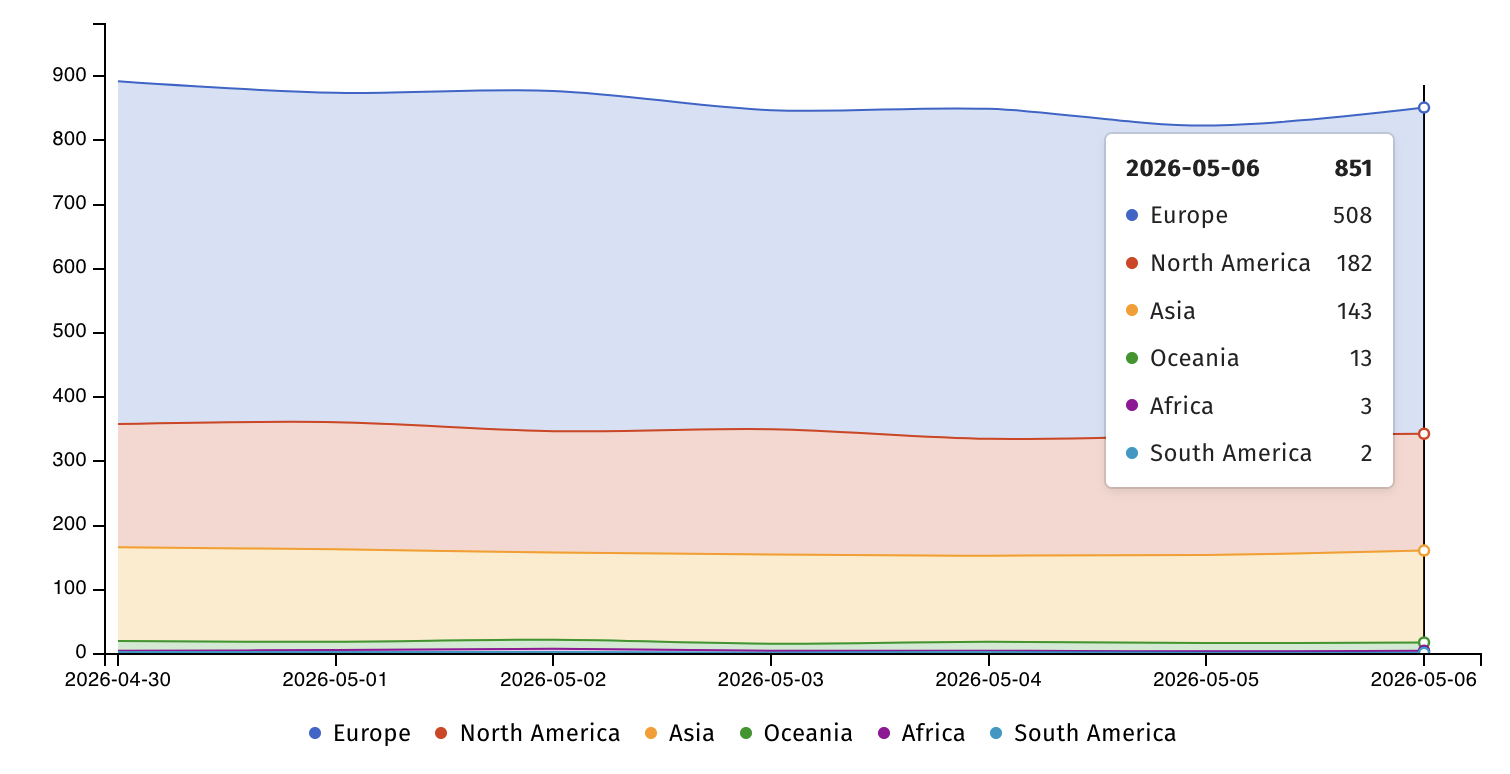
- Shadowserver tracks 850+ exposed EPMM instances, 508 in Europe alone
- Ivanti released patches for five high-severity vulnerabilities in total
What Happened
Ivanti issued an urgent security advisory on May 7 warning that attackers are exploiting a previously unknown vulnerability in its Endpoint Manager Mobile (EPMM) software. The flaw, tracked as CVE-2026-6973, carries a high severity rating and enables remote code execution on affected systems.
The vulnerability stems from improper input validation. Attackers with administrative privileges can exploit it to run arbitrary code on EPMM servers running version 12.8.0.0 or earlier. While the requirement for admin access limits the attack surface, Ivanti confirmed that exploitation is already happening in the wild.
"At the time of disclosure, we are aware of very limited exploitation of CVE-2026-6973, which requires admin authentication for successful exploitation," Ivanti stated in its advisory.
Exposure Scale
Internet security watchdog Shadowserver identified over 850 IP addresses with Ivanti EPMM fingerprints exposed online. Europe accounts for 508 of these instances. North America has 182. The remaining servers are spread across other regions.
Shadowserver did not provide data on how many of these exposed servers have been patched. Organizations running on-premises EPMM deployments should assume they are at risk until they verify their patch status.
The vulnerability does not affect Ivanti Neurons for MDM, the company's cloud-based unified endpoint management platform. It also does not impact Ivanti EPM (a separate product despite the similar name), Ivanti Sentry, or other Ivanti products.
Patches and Mitigation
Ivanti released patched versions: 12.6.1.1, 12.7.0.1, and 12.8.0.1. The company recommends immediate installation for all on-premises EPMM deployments.
Beyond patching, Ivanti advises administrators to review all accounts with admin rights and rotate credentials where necessary. This is especially critical for organizations that were previously targeted.
Customers who rotated credentials after the January 2026 zero-day disclosures (CVE-2026-1281 and CVE-2026-1340) have reduced risk from this new vulnerability. "If customers followed Ivanti's recommendation in January to rotate credentials if you were exploited with CVE-2026-1281 and CVE-2026-1340, then your risk of exploitation from CVE-2026-6973 is significantly reduced," the company noted.
Four Additional Vulnerabilities Patched
The same advisory addressed four other high-severity EPMM flaws. Ivanti said it has no evidence these have been exploited.
- CVE-2026-5786: Allows attackers to gain admin access
- CVE-2026-5787: Enables impersonation of registered Sentry hosts to obtain valid CA-signed client certificates
- CVE-2026-5788: Permits invocation of arbitrary methods
- CVE-2026-7821: Grants access to restricted information (affects only users with Apple Device Enrollment configured)
CVE-2026-7821 is the only one exploitable without privileges, but its impact is limited to a specific configuration scenario.
Pattern of EPMM Zero-Days
This is not the first time Ivanti EPMM has been targeted. In January 2026, the company disclosed two critical code-injection vulnerabilities (CVE-2026-1281 and CVE-2026-1340) that were exploited in zero-day attacks. Ivanti described the impact at the time as affecting "a very limited number of customers."
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) took swift action in April, giving federal agencies just four days to secure their systems against CVE-2026-1340 attacks. CISA has flagged multiple Ivanti EPMM zero-days over recent years, reflecting the product's appeal as a target for attackers seeking access to government and enterprise networks.
Mobile device management platforms like EPMM are high-value targets. They control security policies for fleets of mobile devices and often hold credentials and certificates that provide broad network access.
Logicity's Take
Immediate Actions for IT Teams
- Identify all on-premises EPMM deployments and verify current version numbers
- Apply patches (12.6.1.1, 12.7.0.1, or 12.8.0.1) immediately
- Audit admin accounts and remove unnecessary privileges
- Rotate credentials for all admin accounts, prioritizing any that may have been compromised
- Review logs for signs of unauthorized access or unusual admin activity
Frequently Asked Questions
What is CVE-2026-6973?
CVE-2026-6973 is a high-severity remote code execution vulnerability in Ivanti Endpoint Manager Mobile (EPMM) caused by improper input validation. It requires admin authentication to exploit.
Which Ivanti EPMM versions are affected?
All EPMM versions 12.8.0.0 and earlier are affected. Patched versions are 12.6.1.1, 12.7.0.1, and 12.8.0.1.
Does this vulnerability affect Ivanti's cloud MDM product?
No. Ivanti Neurons for MDM, the cloud-based unified endpoint management solution, is not affected. Only on-premises EPMM deployments are vulnerable.
Is CVE-2026-6973 being actively exploited?
Yes. Ivanti confirmed "very limited exploitation" at the time of disclosure, though specific targets have not been named.
How many EPMM servers are exposed online?
Shadowserver tracks over 850 IP addresses with EPMM fingerprints exposed online, with 508 in Europe and 182 in North America.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.