DAEMON Tools Breached: Supply Chain Attack Backdoored Thousands

Key Takeaways

- DAEMON Tools Lite version 12.5.1 was compromised since April 8, 2025, and distributed through official channels
- Kaspersky found infections in over 100 countries, with a backdoor capable of executing commands and running code in memory
- Users must uninstall version 12.5.1, run a full system scan, and install version 12.6 from the official site
Disc Soft Limited, the company behind DAEMON Tools Lite, has confirmed what security researchers discovered earlier this week: its software was compromised in a supply chain attack. Anyone who downloaded the free version of DAEMON Tools Lite from the official website since April 8 may have installed malware.
The company released version 12.6 on May 5 and says it has secured its infrastructure. But it has not identified the attackers or explained how they got in.
What Happened
In a statement published May 6, Disc Soft acknowledged the breach in measured terms.
“Following an internal investigation, we identified unauthorized interference within our infrastructure. As a result, certain installation packages were impacted within our build environment and were released in a compromised state.”
— Disc Soft Limited
The trojanized installers were digitally signed, which means Windows would have accepted them as legitimate software. Versions 12.5.0.2421 through 12.5.0.2434 were affected. These were available for download from the official DAEMON Tools website for nearly a month before the compromise was discovered.
Disc Soft says paid versions of DAEMON Tools Lite, along with DAEMON Tools Ultra and DAEMON Tools Pro, were not affected.
The Malware Chain
According to Kaspersky, which published its analysis on Tuesday, the attack was methodical and multi-stage.
When users ran the compromised installer, embedded malicious code deployed a payload designed to survive reboots. The first stage was an information stealer that collected:
- Hostname and MAC address
- Running processes
- Installed software
- System locale
This data was sent to attacker-controlled servers. Based on what they found, the attackers selectively pushed a second-stage payload to certain victims. This lightweight backdoor could execute commands, download files, and run code directly in memory, making it harder to detect.
In at least one case, Kaspersky observed a third component: QUIC RAT malware. This tool can inject malicious code into legitimate processes and supports multiple communication protocols, which helps it evade network monitoring.
Who Was Targeted
Kaspersky found infections in more than 100 countries. The victims included both individual users and organizations in retail, scientific research, government, and manufacturing sectors.
The countries most affected were Russia, Belarus, Thailand, Brazil, and Turkey. The geographic spread and the variety of targets suggest the attackers may have been casting a wide net rather than pursuing specific organizations.
What You Should Do
If you downloaded or installed DAEMON Tools Lite (free version) since April 8, Disc Soft recommends the following steps:
- Uninstall DAEMON Tools Lite version 12.5.1 immediately
- Run a full system scan using antivirus or security software
- Download and install version 12.6 from the official DAEMON Tools website
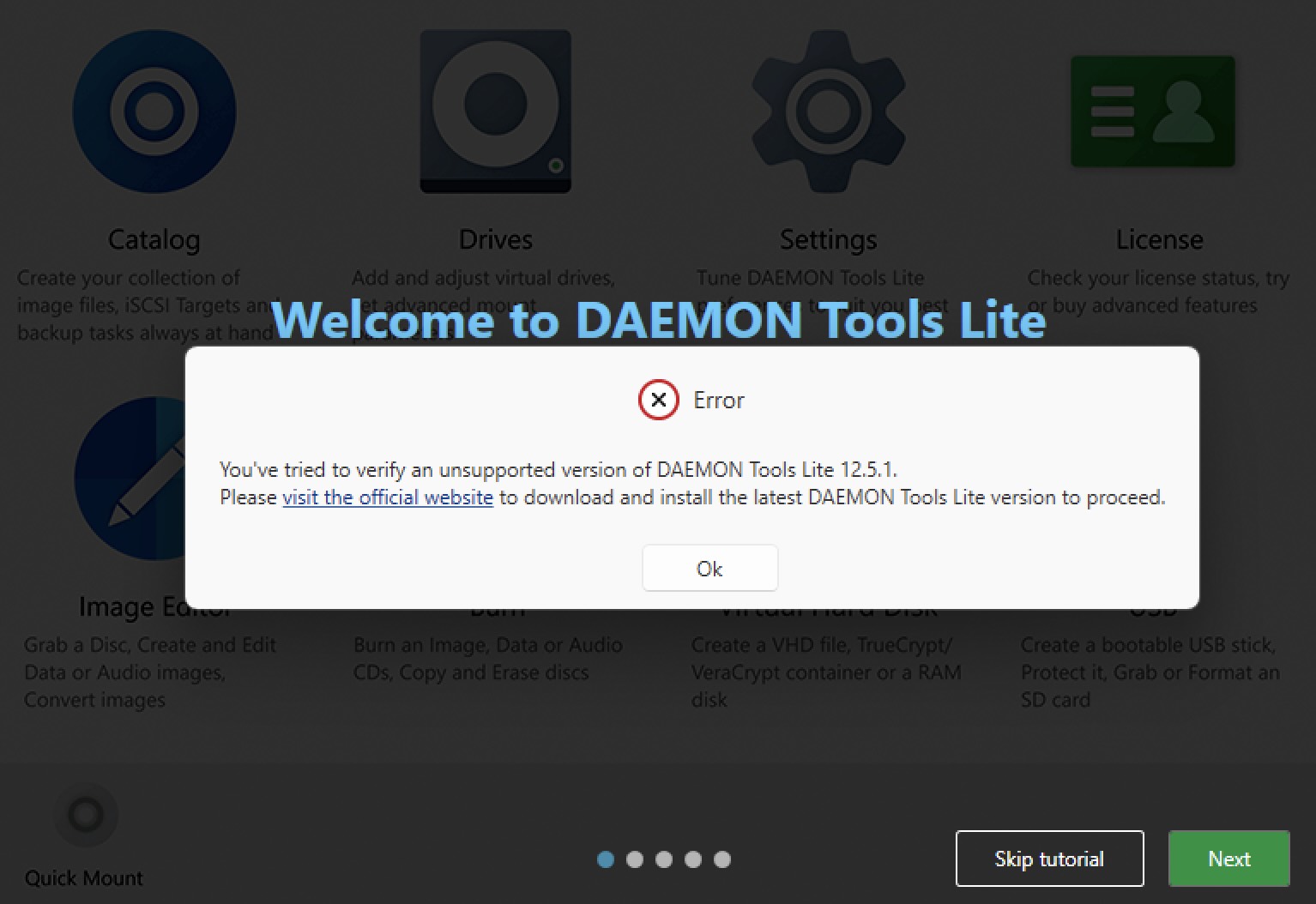
The company has removed the trojanized version from distribution. Users who try to run version 12.5.1 will now see a warning prompting them to update.
Supply Chain Attacks Are Getting Harder to Spot
This incident follows a pattern that security teams have seen repeatedly. Attackers compromise a software vendor's build environment, inject malicious code, and let the vendor's own distribution channels do the work. Because the installers are signed with legitimate certificates, they pass most security checks.
The SolarWinds attack in 2020 was the highest-profile example. The 3CX breach in 2023 hit business communication software. Now DAEMON Tools joins the list. Each attack reaches thousands or millions of users through a single point of compromise.
Disc Soft has not said whether it will publish a detailed post-mortem or timeline. The investigation is ongoing.
Logicity's Take
The DAEMON Tools breach is another reminder that software supply chains are prime targets. If attackers can get into a vendor's build system, they can bypass every security measure you have. Organizations need to treat software updates with the same scrutiny as unknown downloads, especially for utilities with system-level access.
Frequently Asked Questions
Frequently Asked Questions
How do I know if my DAEMON Tools installation is compromised?
If you downloaded or installed DAEMON Tools Lite (free) version 12.5.1 between April 8 and May 5, 2025, from the official website, your system may be affected. Uninstall the software and run a full antivirus scan.
Are paid versions of DAEMON Tools affected?
No. Disc Soft says paid versions of DAEMON Tools Lite, DAEMON Tools Ultra, and DAEMON Tools Pro were not compromised.
What should I do if my system was infected?
Uninstall version 12.5.1, run a full system scan with reputable antivirus software, and monitor for unusual activity. If you handle sensitive data, consider a deeper forensic review.
Who is behind the attack?
Disc Soft has not attributed the attack to any specific threat actor. The investigation is ongoing.
Is version 12.6 safe to install?
According to Disc Soft, version 12.6 does not contain the compromised files and was released after the company secured its infrastructure.
Need Help Implementing This?
If your organization uses DAEMON Tools or needs to assess supply chain security risks, Logicity can connect you with security experts. Contact our team for guidance on incident response and software vetting practices.
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.