Credit Union Loan Fraud: How Attackers Skip the Hack

Key Takeaways

- Fraudsters target credit unions through identity fraud, not software exploits
- Knowledge-based authentication questions can be answered using leaked data and social media
- Small to mid-sized credit unions are preferred targets due to perceived weaker fraud controls
No Hacking Required
The attackers do not break into systems. They walk through the front door. Flare researchers recently identified a detailed loan fraud method circulating in underground chat groups. The approach outlines how to move through credit checks, identity verification, and loan approval using stolen identities. No software vulnerabilities involved.
The method treats legitimate lending workflows as the attack surface. Attackers submit loan applications as if they were genuine borrowers, using enough personal data to pass each checkpoint. The process is entirely digital, and the structure of the instructions suggests this is not opportunistic. It is organized and repeatable.
Why Credit Unions Are Attractive Targets
Discussions in underground forums single out small and mid-sized credit unions as preferred targets. The reasoning: perceived gaps in verification systems and limited fraud prevention resources compared to major banks.
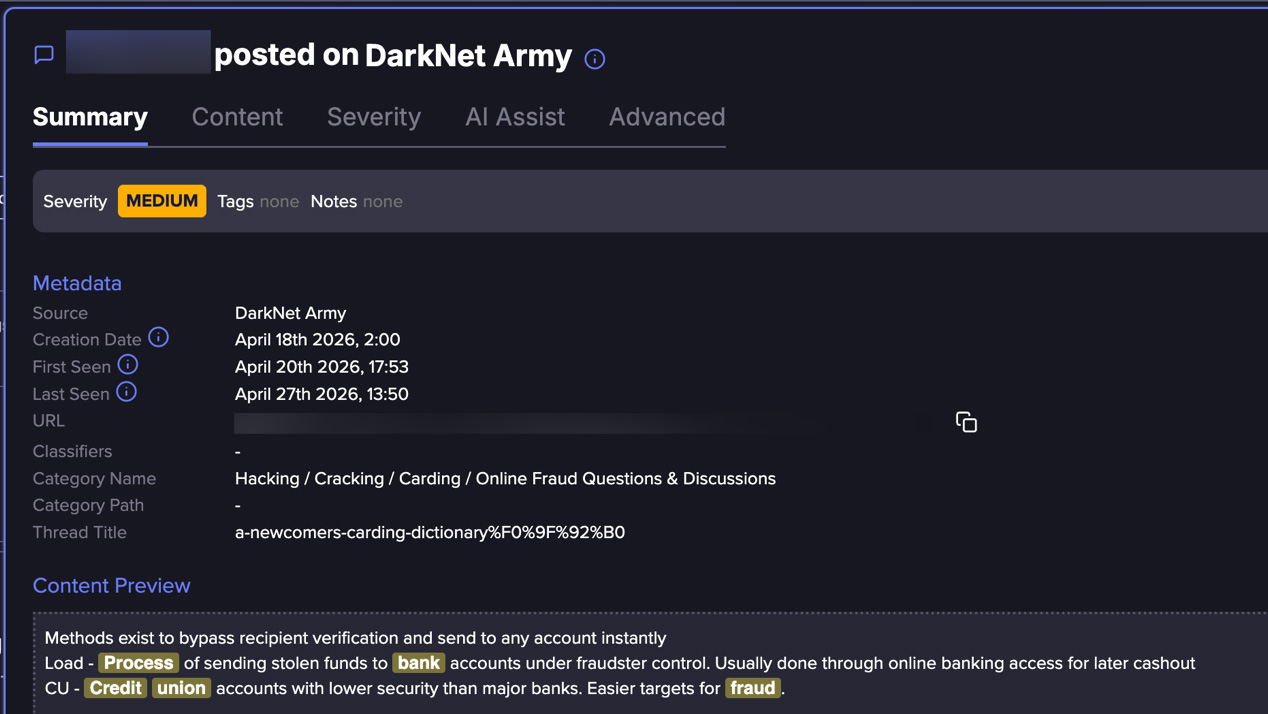
Large banks invest heavily in fraud detection. They have dedicated teams, machine learning models, and multi-layered verification. Smaller credit unions often rely on more traditional controls. Attackers know this and factor it into their targeting.
The Identity Data Supply Chain
The fraud method depends on obtaining enough personal data to impersonate a legitimate borrower. This includes names, addresses, dates of birth, and credit-related details. Underground forums sell packaged identity kits. Some include credit history fragments.
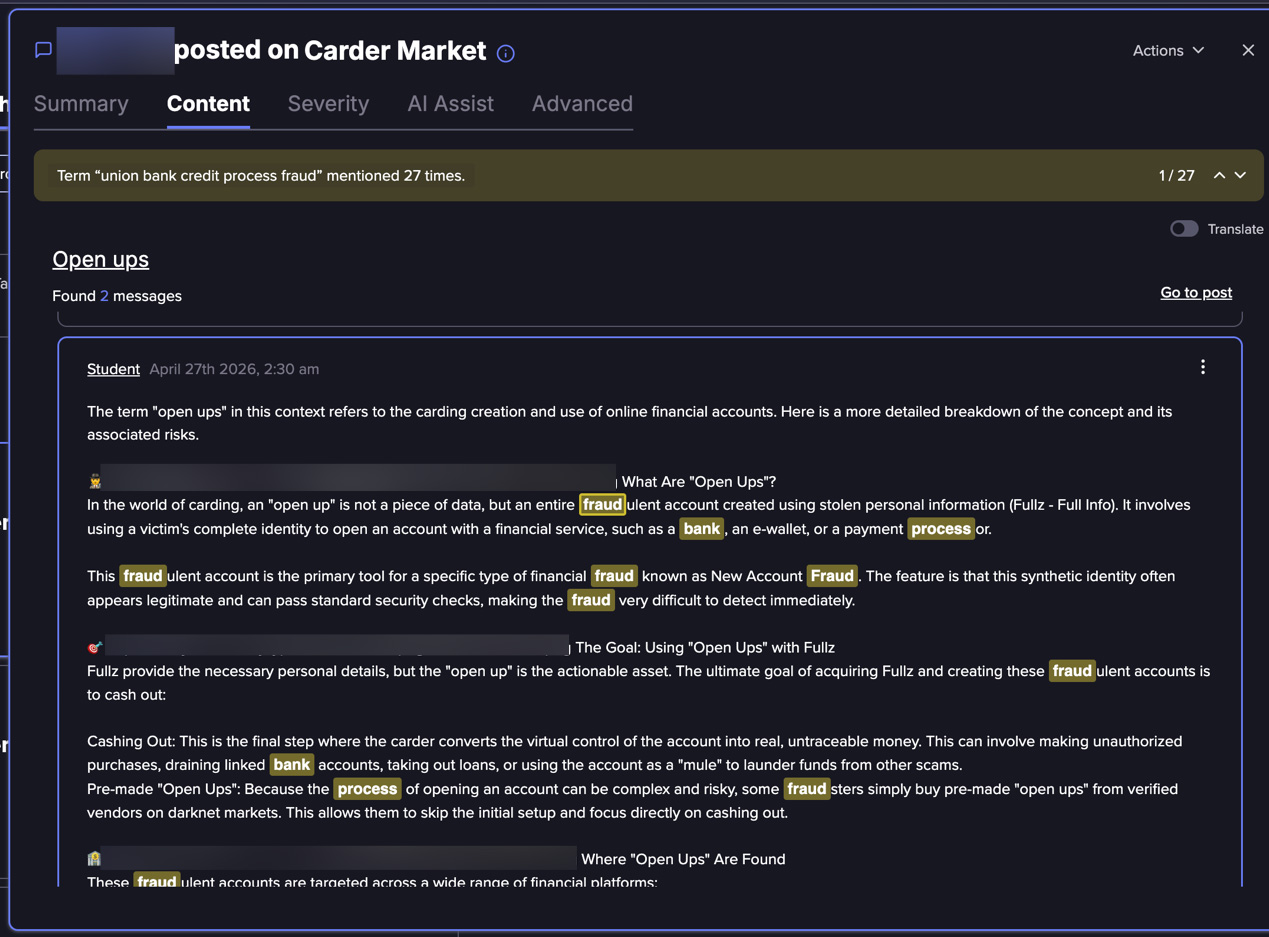
Where does this data come from? Previous breaches, aggregated public records, and social media profiles. The Flare research notes that attackers can reconstruct or infer much of what they need from these sources.
Knowledge-Based Authentication Is the Weak Link
A central component of the method is passing knowledge-based authentication (KBA). These are the security questions credit unions ask to verify identity. Typical KBA questions draw from past addresses, loan or credit history, and employment or family associations.
The problem: this information is often available or inferable. Previous addresses appear in public records. Employment history sits on LinkedIn. Family associations show up on Facebook. Loan history may exist in previously leaked datasets.
The Flare research shows attackers prepare for these questions in advance. They treat verification as a predictable step, not a barrier. What was designed as a security control becomes a checklist item.
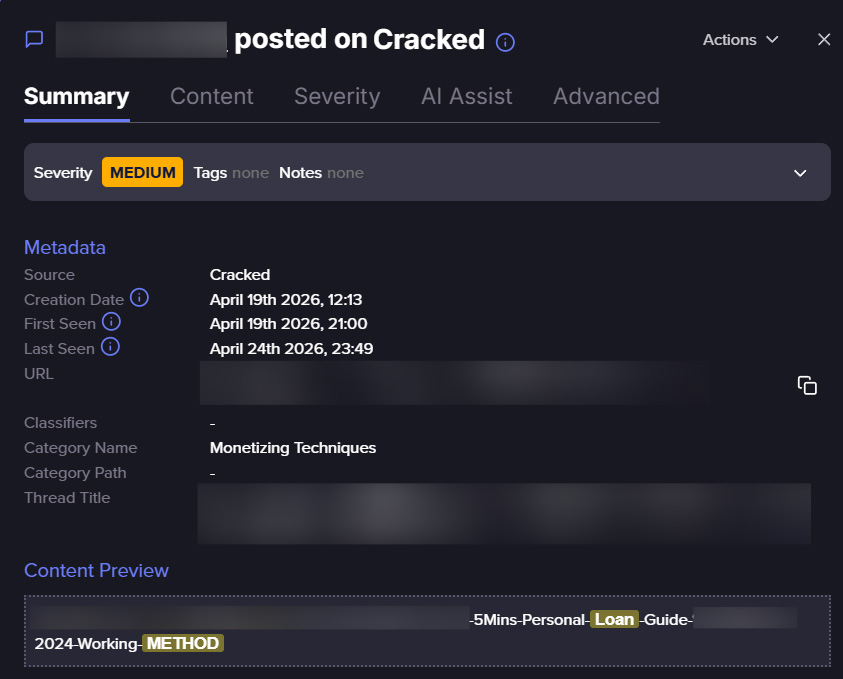
From Loan Application to Cash Out
The fraud method breaks down the process from identity acquisition to loan approval. Each step is documented for replication. The structure suggests this is being shared as a how-to guide, not a one-off trick.
Once approved, the loan funds go to accounts the attacker controls. The credit union believes it has lent money to a legitimate member. The real identity owner may not discover the fraud for months, often when collections start.
What This Means for Fraud Prevention
Traditional perimeter security does not address this threat. Firewalls and intrusion detection systems protect against technical attacks. They do not stop someone submitting a valid-looking loan application with stolen data.
- KBA alone is insufficient. Supplement with device fingerprinting, behavioral analytics, or document verification.
- Monitor for patterns in loan applications. Multiple applications from similar IP ranges or device profiles may indicate organized fraud.
- Check identity data against known breach databases. If the applicant's information appears in recent leaks, that is a red flag.
- Train staff to recognize social engineering. Some fraud methods include phone calls to build rapport before digital applications.
The Organized Fraud Economy
This is not a lone actor improvising. The structure of the forum posts reflects process-driven fraud. Methods are documented, refined, and shared. Successful techniques spread quickly through underground communities.
Credit unions face a mismatch. They often operate with the resources of a local institution while defending against a global fraud economy. The attackers have specialization: some acquire identities, some craft applications, some cash out. It is a supply chain.
Logicity's Take
Frequently Asked Questions
Why are credit unions targeted more than large banks?
Attackers perceive credit unions as having weaker verification systems and fewer fraud prevention resources than major banks, making them easier targets for identity-based fraud.
How do fraudsters pass identity verification checks?
They use data from breaches, public records, and social media to answer knowledge-based authentication questions. This information is often available or can be inferred from existing datasets.
What is knowledge-based authentication and why is it vulnerable?
KBA asks security questions based on personal history like past addresses or credit details. It is vulnerable because much of this information is publicly available or has been exposed in data breaches.
How can credit unions protect against this type of fraud?
Supplement KBA with device fingerprinting, behavioral analytics, and document verification. Monitor for application patterns and check identity data against breach databases.
Are these fraud methods shared openly?
Yes. Flare researchers found detailed, structured methods circulating in underground forums and chat groups, formatted as step-by-step guides for replication.
Need Help Implementing This?
Source: BleepingComputer
Huma Shazia
Senior AI & Tech Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.