1.1 Million Baby Monitors Exposed by Single Security Key

Key Takeaways

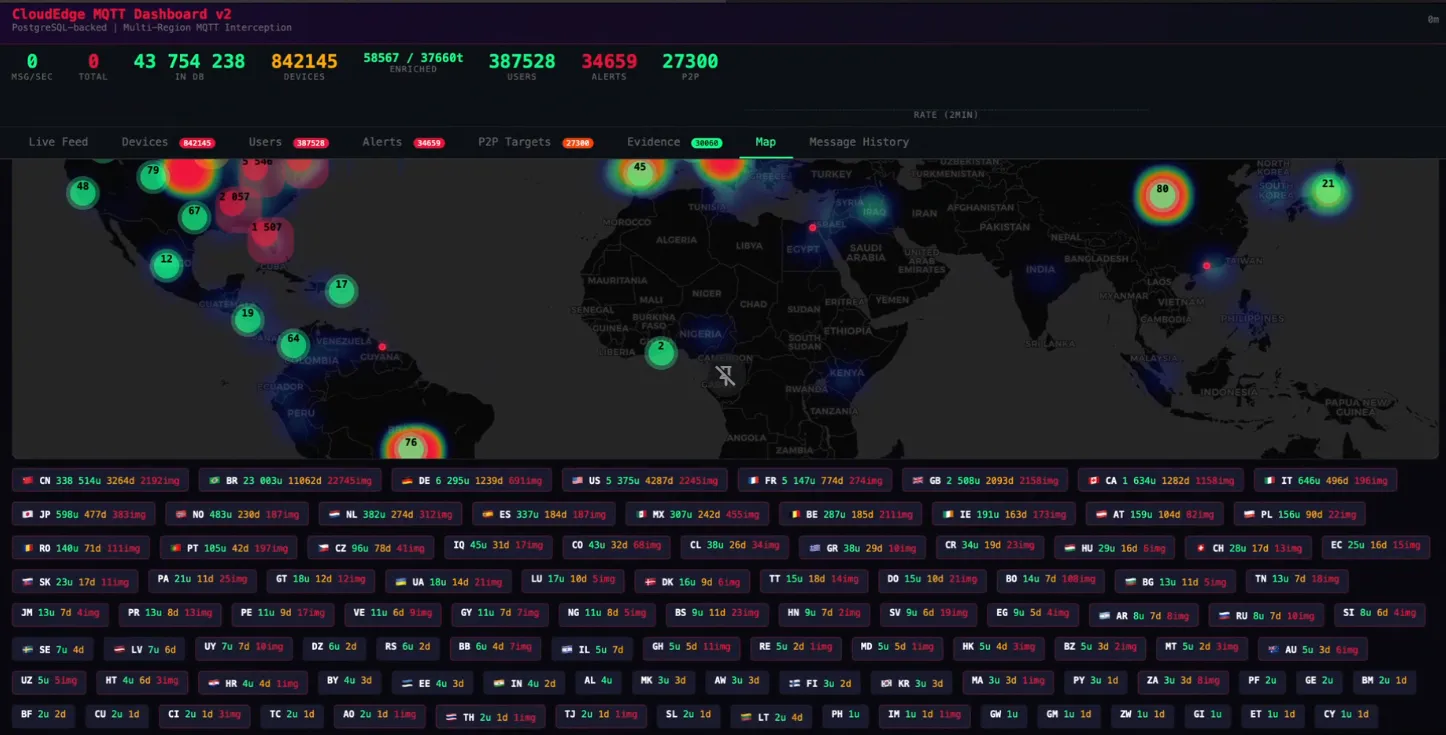
- 1.1 million cameras across 118 countries were accessible using one extracted key
- Default passwords included 'admin' and 'public' with no enforcement of changes
- Tens of thousands of photos were stored on public URLs without any password protection
A baby's eyes peer into a camera lens. A child in a policeman costume stands in frame. A messy bedroom with Hello Kitty decorations. These images, captured by home security cameras, were viewable by anyone who knew where to look.
French security researcher Sammy Azdoufal discovered that 1.1 million baby monitors and security cameras made by Meari Technology were accessible remotely. The cameras, sold under dozens of brand names, broadcast their data to anyone with the right key. Azdoufal extracted that key from the Android app.
The Scope of Exposure
Meari Technology is a Chinese white-label manufacturer. Their cameras ship under hundreds of different brand names on Amazon and other retailers. Names like Arenti, Anran, Boifun, and ieGeek. Financial records show the company's customers include major players: Wyze, Zhiyun, and Intelbras. At least one Petcube pet camera appears to be a Meari product as well.
If you bought a budget baby monitor or security camera online, there's a reasonable chance Meari made it.

Azdoufal found the vulnerability the same way he previously discovered access to thousands of DJI Romo robot vacuums. By inspecting the Android app, he extracted a single key that unlocked devices across 118 countries. Every one of those million devices was broadcasting information to anyone who knew how to listen.
Related: how companies are addressing security vulnerabilities
Passwords Set to 'Admin' and 'Public'
The technical failures went beyond the shared key. Many cameras were still using default passwords. One password was simply "admin." Another was "public." Users were never required to change them.
When Azdoufal connected the MQTT datastream to a world map, he could see everything. He could see into people's homes. He could see email addresses and rough locations of camera owners.
Tens of thousands of photos captured by these cameras sat on Alibaba servers at public web addresses. No password. No encryption. No protection at all.
“I can retrieve the picture without any passwords, no cracking, no hacking. I just click on the URL and this image is showing.”
— Sammy Azdoufal, security researcher
A Pattern of Poor IoT Security
This is not Azdoufal's first discovery of mass IoT vulnerabilities. He previously found that DJI Romo robot vacuums had security so poor he could remotely access thousands of them. The pattern suggests systemic failures in how budget IoT devices handle authentication and data protection.
The white-label model makes accountability murky. Consumers buy from brands like Wyze or Intelbras. Those brands source hardware from Meari. Security flaws originate at the manufacturer level but affect users across dozens of retail brands.
What Camera Owners Should Do
If you own a baby monitor or security camera from any of the mentioned brands, check if it's a Meari device. Look for the Meari name in the app settings or on the device itself. The company sells under so many labels that identifying affected products is difficult.
- Change default passwords immediately if you haven't already
- Check if your camera app is connected to Meari's cloud services
- Consider cameras from manufacturers with established security track records
- Segment IoT devices on a separate network from computers and phones
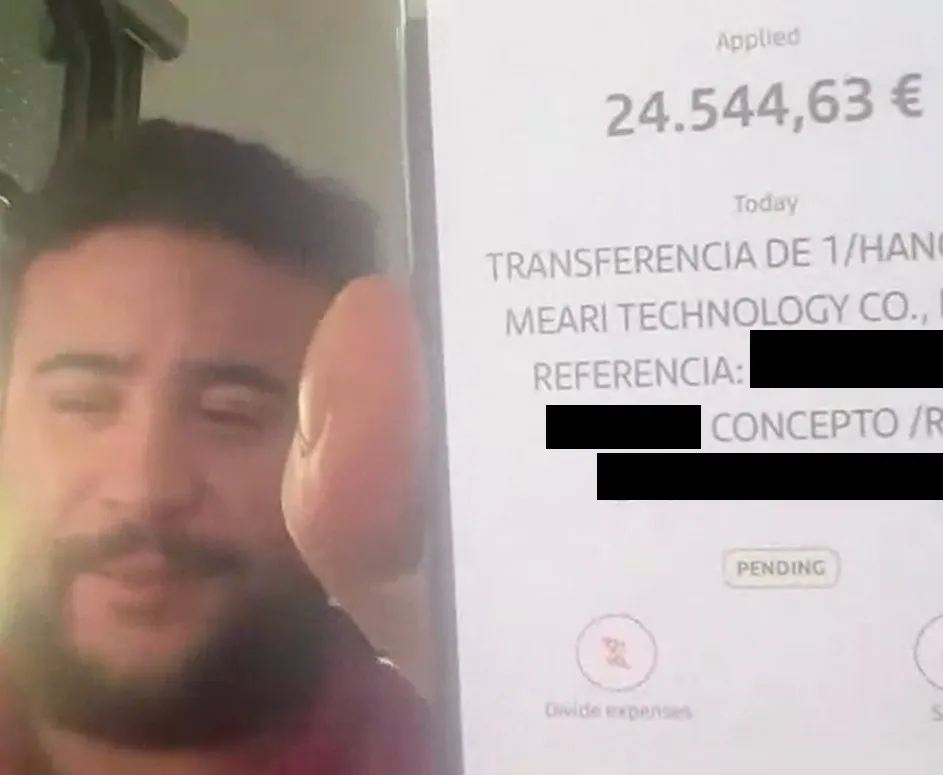
Azdoufal reported the vulnerability through responsible disclosure. Meari paid a bug bounty, suggesting they acknowledged the flaw.
Logicity's Take
Frequently Asked Questions
Which baby monitor brands are affected by the Meari security flaw?
Cameras from Arenti, Anran, Boifun, ieGeek, Intelbras, and potentially Wyze and Petcube. Meari manufactures white-label products for hundreds of brands.
How were 1.1 million cameras accessed?
A security researcher extracted a single authentication key from the Android app. This key provided access to devices across 118 countries. Many cameras also used default passwords like "admin" or "public."
Were photos from these cameras actually exposed?
Yes. Tens of thousands of photos were stored on Alibaba servers at public URLs with no password protection. Anyone with the URL could view them.
How do I know if my camera is made by Meari?
Check the app settings or device documentation for Meari branding. Many budget cameras sold on Amazon under generic names are Meari products.
Has Meari fixed the vulnerability?
The company paid a bug bounty to the researcher who disclosed the flaw, indicating they acknowledged it. The current status of patches is unclear.
Need Help Implementing This?
Manaal Khan
Tech & Innovation Writer
اقرأ أيضاً

رأي مغاير: كيف يؤثر اختراق الأمن الداخلي الأميركي على شركاتنا الخاصة؟
في ظل اختراق عقود الأمن الداخلي الأميركي مع شركات خاصة، نناقش تأثير هذا الاختراق على مستقبل الأمن السيبراني. نستعرض الإحصاءات الموثوقة ونناقش كيف يمكن للشركات الخاصة أن تتعامل مع هذا التهديد. استمتع بقراءة هذا التحليل العميق

الإنسان في زمن ما بعد الوجود البشري: نحو نظام للتعايش بين الإنسان والروبوت - Centre for Arab Unity Studies
في هذا المقال، سنناقش كيف يمكن للبشر والروبوتات التعايش في نظام متكامل. سنستعرض التحديات والحلول المحتملة التي تضعها شركات مثل جوجل وأمازون. كما سنلقي نظرة على التوقعات المستقبلية وفقًا لتقرير ماكنزي

إطلاق ناسا لمهمة مأهولة إلى القمر: خطوة تاريخية نحو استكشاف الفضاء
تعتبر المهمة الجديدة خطوة هامة نحو استكشاف الفضاء وتطوير التكنولوجيا. سوف تشمل المهمة إرسال رواد فضاء إلى سطح القمر لconducting تجارب علمية. ستسهم هذه المهمة في تطوير فهمنا للفضاء وتحسين التكنولوجيا المستخدمة في استكشاف الفضاء.